Important: The GCConnex decommission will not affect GCCollab or GCWiki. Thank you and happy collaborating!
Difference between revisions of "GC Service & Digital Target Enterprise Architecture"
John.currah (talk | contribs) (June 2021 Graphical update) |
John.currah (talk | contribs) (L’objectif de l'architecture intégrée) |
||
| (7 intermediate revisions by the same user not shown) | |||
| Line 37: | Line 37: | ||
This white paper is not meant to replace existing documents that address the government’s strategic direction on digital services. | This white paper is not meant to replace existing documents that address the government’s strategic direction on digital services. | ||
| − | === | + | === Digital government === |
| − | + | A digital government puts people and their needs first. It is accountable to its citizens and shares information with them. It involves them when making policies and designing services. It values inclusion and accessibility. It designs services for the people who need them, not for the organizations that deliver them. | |
| − | Digitally, the Government of Canada must operate as one to benefit | + | <blockquote>The Government of Canada is an open and service-oriented organization that operates and delivers programs and services to people and businesses in simple, modern and effective ways that are optimized for digital and available anytime, anywhere and from any device. |
| + | |||
| + | Digitally, the Government of Canada must operate as one to benefit each and every Canadian.<ref>Digital Operations Strategic Plan: 2021–2024 - Canada.ca</ref> | ||
| + | </blockquote> | ||
=== ''Policy on Service and Digital'' === | === ''Policy on Service and Digital'' === | ||
| Line 83: | Line 86: | ||
[[Image:Service and Digital Target State Architecture-vJun2021.png|Service_and_Digital_Target_State_Architecture-vJun2021.png|frameless|900px]] | [[Image:Service and Digital Target State Architecture-vJun2021.png|Service_and_Digital_Target_State_Architecture-vJun2021.png|frameless|900px]] | ||
| − | The goal of the Service and Digital Target State Enterprise Architecture is to depict the Government of Canada’s future state | + | <div class="mw-collapsible mw-collapsed" data-expandtext="Text Version" data-collapsetext="Hide Text Version"> |
| + | <div class="sidetable"> | ||
| + | <table class="wikitable"> | ||
| + | <tr> | ||
| + | <td> | ||
| + | <h1> | ||
| + | Service and Digital Target Enterprise Architecture - Text version | ||
| + | </h1> | ||
| + | </td> | ||
| + | <tr> | ||
| + | <td> | ||
| + | <p>The top row of the diagram shows examples of business programs and services, divided into two categories: front-office and back-office. </p> | ||
| + | <p>Examples of front-office business programs and services:</p> | ||
| + | <ul> | ||
| + | <li>Pensions</li> | ||
| + | <li>Employment Insurance</li> | ||
| + | <li>Licensing</li> | ||
| + | <li>Payments</li> | ||
| + | <li>Grants and contributions</li> | ||
| + | <li>Tax filing</li> | ||
| + | </ul> | ||
| + | <p>Examples of back-office programs and services:</p> | ||
| + | <ul> | ||
| + | <li>Core finance (FMT)</li> | ||
| + | <li>Security screening</li> | ||
| + | <li>NextGen HR and Pay</li> | ||
| + | <li>Enterprise procurement</li> | ||
| + | <li>Cloud-brokering service</li> | ||
| + | </ul> | ||
| + | <p>The second row of the architecture shows the top‑level business capabilities:</p> | ||
| + | <ul> | ||
| + | <li>Legislation, regulation and policy management</li> | ||
| + | <li>Enterprise planning</li> | ||
| + | <li>Outcomes management </li> | ||
| + | <li>Relationship management </li> | ||
| + | <li>Compliance management</li> | ||
| + | <li>Program and service delivery</li> | ||
| + | <li>Information management </li> | ||
| + | <li>Government resources management</li> | ||
| + | <li>Corporate management </li> | ||
| + | </ul> | ||
| + | <p>The third row lists the DevSecOps principles: Continuous integration and continuous deployments, automation of testing for security and functionality, inclusion of stakeholders</p> | ||
| + | <p>The fourth row identifies the various stakeholders: </p> | ||
| + | <p>Externally, examples include:</p> | ||
| + | <ul> | ||
| + | <li>Citizens</li> | ||
| + | <li>Businesses</li> | ||
| + | <li>International</li> | ||
| + | <li>Partnerships</li> | ||
| + | </ul> | ||
| + | <p>Internally, examples include:</p> | ||
| + | <ul> | ||
| + | <li>Employees, delegates, elected officials </li> | ||
| + | </ul> | ||
| + | <p>Two examples of user authentication are presented under the external stakeholder:</p> | ||
| + | <ul> | ||
| + | <li>Identity management </li> | ||
| + | <li>Sign-in Canada</li> | ||
| + | </ul> | ||
| + | <p>A third example related to the internal stakeholders is GCPass. </p> | ||
| + | <p>The fifth row identifies channels and interfaces.</p> | ||
| + | <p>Externally accessible solution examples are:</p> | ||
| + | <ul> | ||
| + | <li>OneGC platform: providing a tell-us-once experience</li> | ||
| + | <li>Omni-channel </li> | ||
| + | </ul> | ||
| + | <p>The third example is related to internal users:</p> | ||
| + | <ul> | ||
| + | <li>Digital workspace: GCexchange, GCTools</li> | ||
| + | </ul> | ||
| + | <p>The next part of the graphic show the elements of the information architecture, application architecture and technology architecture. </p> | ||
| + | <p><strong>Information architecture</strong></p> | ||
| + | <ul> | ||
| + | <li>For example, master data management, privacy (protection of personal data) </li> | ||
| + | </ul> | ||
| + | <p>Canada’s Digital Exchange Platform offers the following capabilities:</p> | ||
| + | <ul> | ||
| + | <li>API store</li> | ||
| + | <li>Event broker </li> | ||
| + | <li>Bulk data </li> | ||
| + | </ul> | ||
| + | <p><strong>Application architecture </strong>is divided into two categories based on security requirements:</p> | ||
| + | <ul> | ||
| + | <li>SaaS subscription feature</li> | ||
| + | <li>PaaS serverless hosted feature</li> | ||
| + | <li>IaaS broken into three parts: | ||
| + | <ul> | ||
| + | <li>Feature: IaaS</li> | ||
| + | <li>Runtime: IaaS</li> | ||
| + | <li>Data store: IaaS</li> | ||
| + | </ul> | ||
| + | </li> | ||
| + | <li>Automations can be achieved through tools such as: | ||
| + | <ul> | ||
| + | <li>artificial intelligence</li> | ||
| + | <li>workflow engines</li> | ||
| + | <li>machine learning</li> | ||
| + | <li>low‐code platforms</li> | ||
| + | </ul> | ||
| + | </li> | ||
| + | <li>Open source: solutions listed on open resource exchange</li> | ||
| + | </ul> | ||
| + | <p>The information from these application architecture options is shared back to the <strong>Canada’s Digital Exchange Platform</strong> via APIs (application programming interfaces).</p> | ||
| + | <p>Secret and above Secret systems, features, data, and storage exposed and consumed via API plus exceptions to cloud-first policy.</p> | ||
| + | <p><strong>Technology architecture</strong></p> | ||
| + | <p>Public cloud is the recommended architecture for solutions that are considered Protected B or below from an identified security level.</p> | ||
| + | <p>Solutions above Protected B must use Enterprise Data Centres. </p> | ||
| + | <p>All the layers of the Service and Digital Target Enterprise Architecture rely on <strong>enterprise network connectivity</strong>.</p> | ||
| + | <p>Examples of enterprise network connectivity include:</p> | ||
| + | <ul> | ||
| + | <li>Cloud-to-ground connectivity</li> | ||
| + | <li>secure cloud enablement and defence </li> | ||
| + | <li>cloud guardrails</li> | ||
| + | <li>network and cybermonitoring</li> | ||
| + | <li>LAN/WAN </li> | ||
| + | <li>GCSI </li> | ||
| + | <li>Related business continuity infrastructure</li> | ||
| + | </ul> | ||
| + | <p>Along the right side of the graphic are two overarching principles:</p> | ||
| + | <ul> | ||
| + | <li>Security by design: zero-trust authentication, authorization, encryption, tokenization and accreditation</li> | ||
| + | <li>Privacy: collection, use, accuracy, retention, and disposition</li> | ||
| + | </ul> | ||
| + | </td> | ||
| + | |||
| + | </tr> | ||
| + | </table> | ||
| + | </div> | ||
| + | </div> | ||
| + | |||
| + | <br/> | ||
| + | <br/> | ||
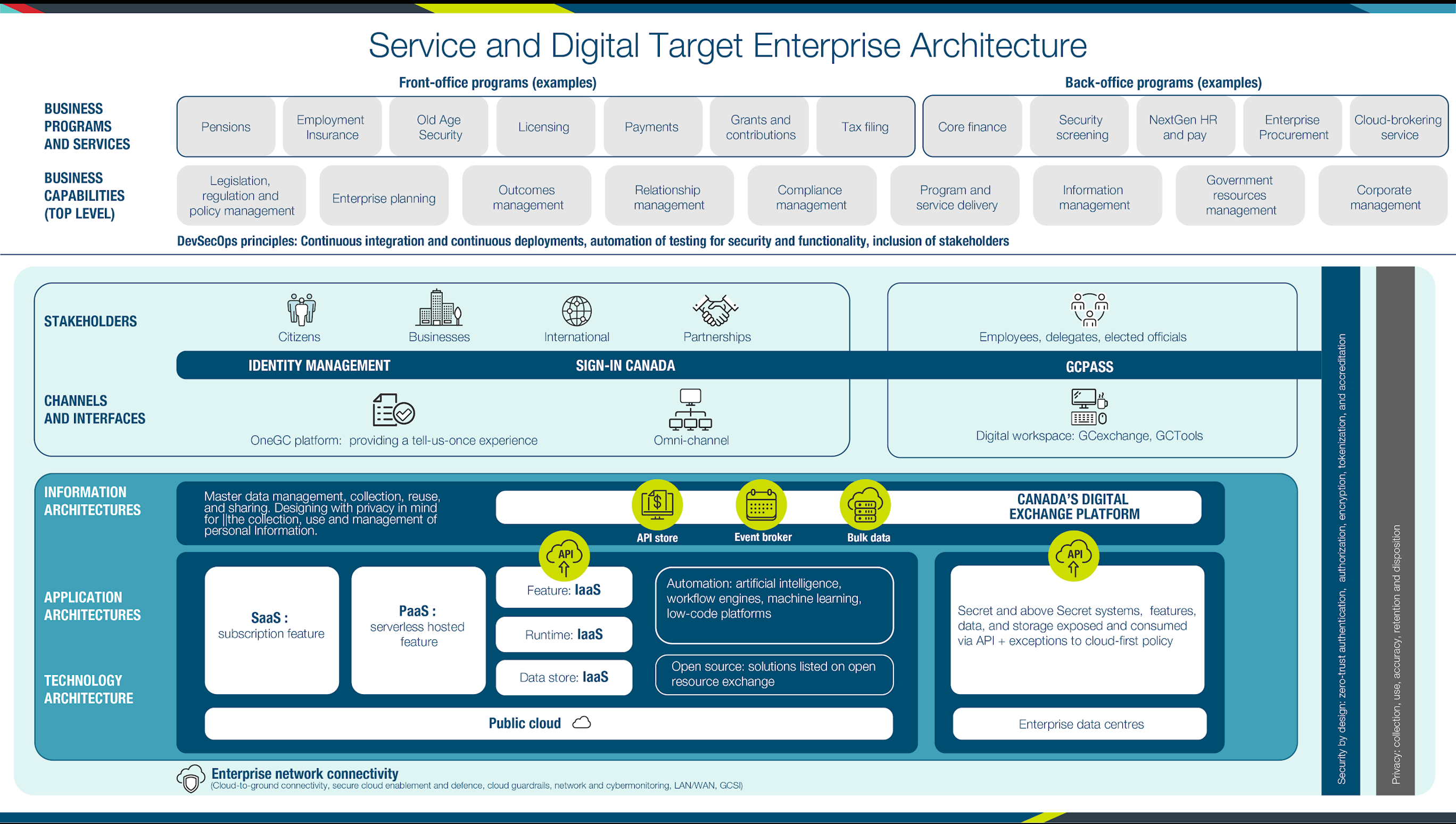
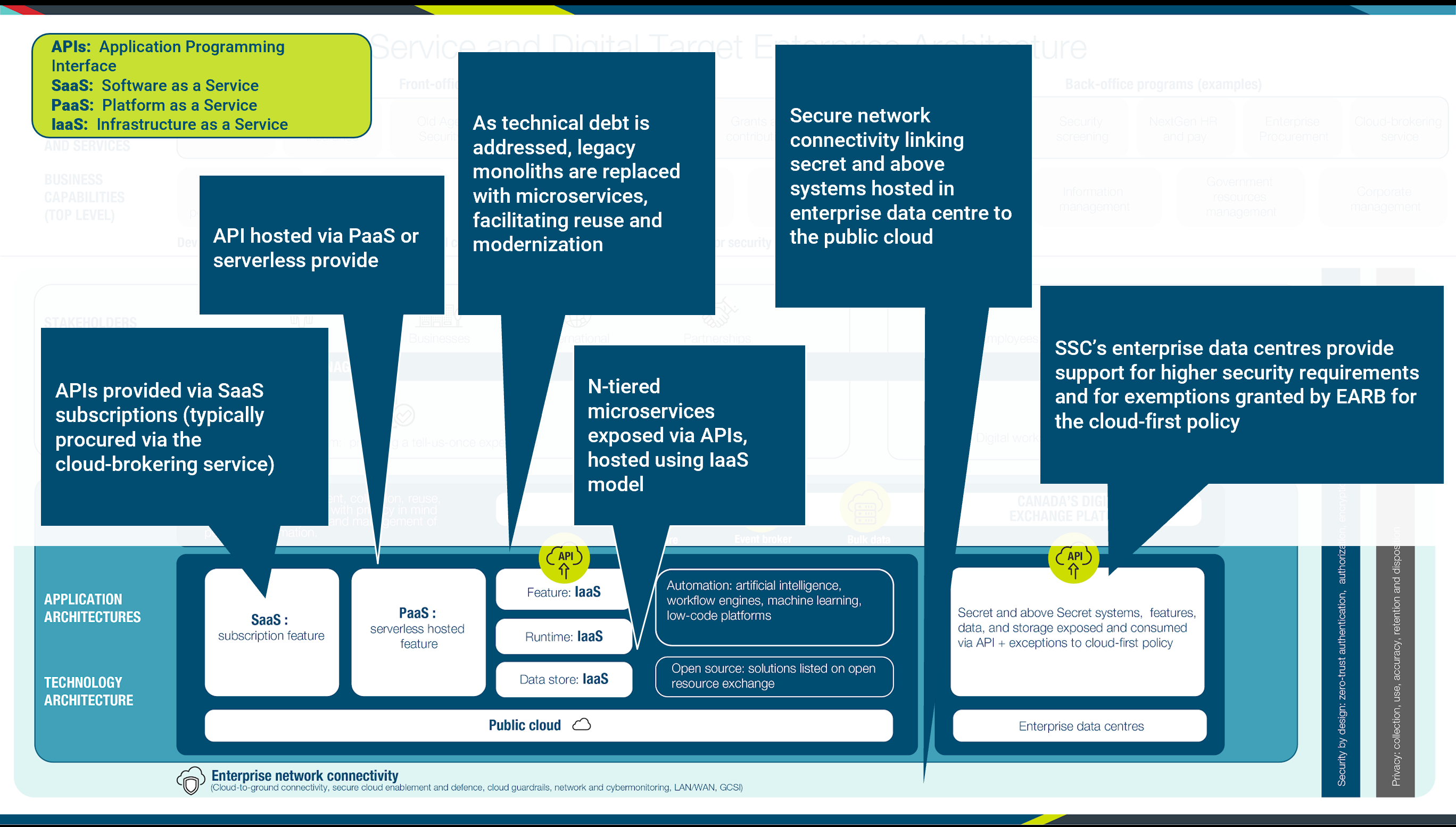
| + | The goal of the Service and Digital Target State Enterprise Architecture is to depict the Government of Canada’s future state in one picture. The diagram is divided into several parts, which are based on The Open Architecture Framework (TOGAF) framework explained in a subsequent section. This framework views business, information and data, applications, technology and security each as separate layers, having their own concerns and architecture. | ||
The top layer of the diagram represents business architecture. The programs in this layer are categorized as front office, which provides services directly to citizens, academic institutions, and Canadian businesses, and back‑office services which support the government itself. Examples of front office programs include Employment Insurance and tax filing services, and examples of back‑end programs include finance security screening, pay, enterprise procurement, and business continuity. | The top layer of the diagram represents business architecture. The programs in this layer are categorized as front office, which provides services directly to citizens, academic institutions, and Canadian businesses, and back‑office services which support the government itself. Examples of front office programs include Employment Insurance and tax filing services, and examples of back‑end programs include finance security screening, pay, enterprise procurement, and business continuity. | ||
| Line 98: | Line 233: | ||
The next layer projects the idea of a service‑oriented government, with a user‑centred approach to the business of government that puts citizens and their needs as the primary focus of our work, using “tell‑us‑once” service approaches, integrated services across the GC program and service landscape in a way that provides real‑time information to Canadians about their service applications. It is a perspective centred on users and service delivery when considering new IT solutions or modernizing older solutions. It builds on business architecture guidance to design for users first, focusing on the needs of users, using agile, iterative, and user‑centred methods in a whole-of-government context. | The next layer projects the idea of a service‑oriented government, with a user‑centred approach to the business of government that puts citizens and their needs as the primary focus of our work, using “tell‑us‑once” service approaches, integrated services across the GC program and service landscape in a way that provides real‑time information to Canadians about their service applications. It is a perspective centred on users and service delivery when considering new IT solutions or modernizing older solutions. It builds on business architecture guidance to design for users first, focusing on the needs of users, using agile, iterative, and user‑centred methods in a whole-of-government context. | ||
| − | [[ | + | |
| + | [[Image:SandD_External_Stakeholders-vJune2021.png|SandD_External_Stakeholders-vJune2021.png|frameless|900px]] | ||
| + | |||
| + | |||
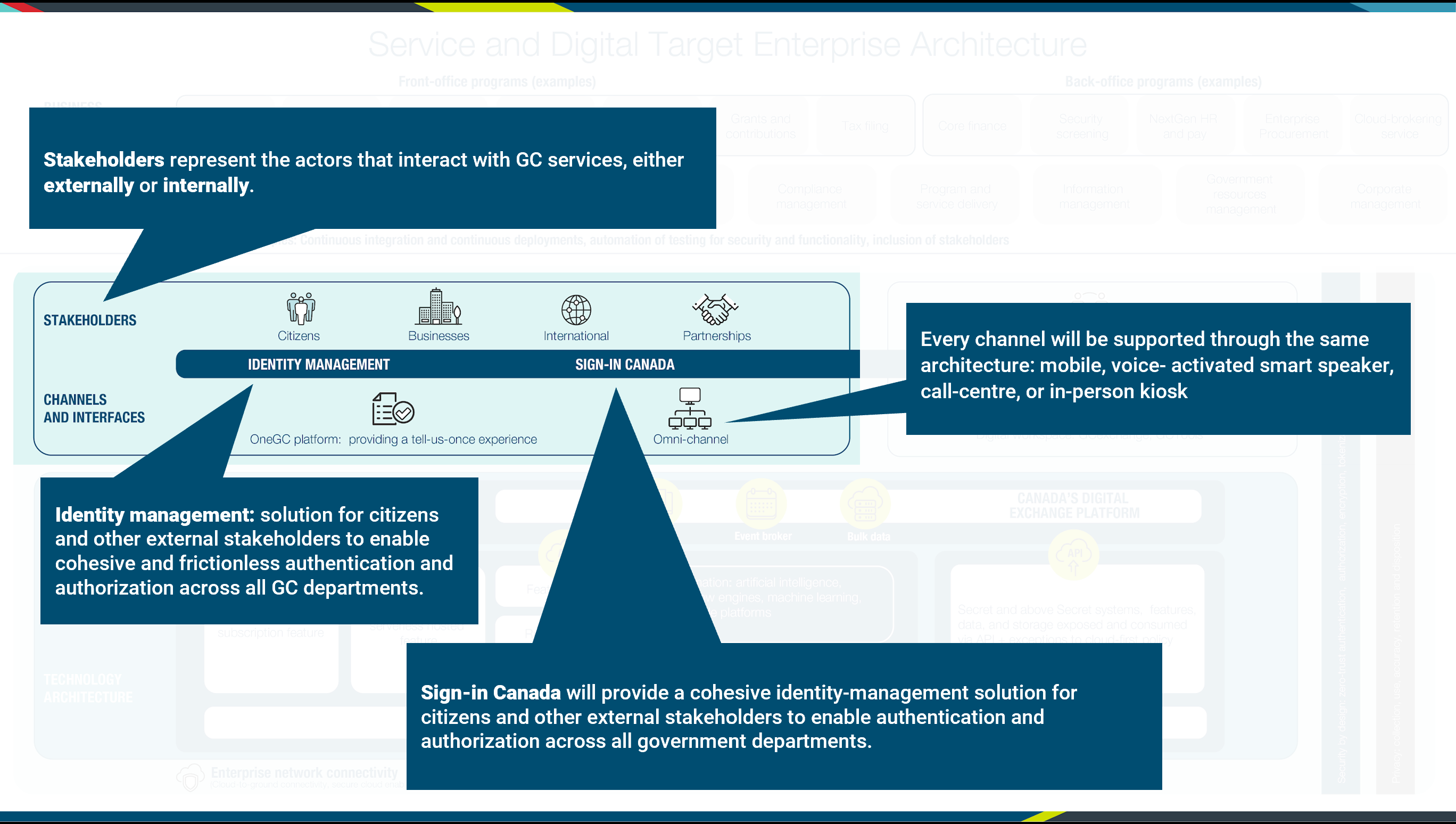
Leveraging the concept of harmonization described for external users through Sign‑in Canada, GCPass will enable authentication and authorization to GC Systems for Internal stakeholders. The digital workplace will uniformly enable the work of public servants, building on a standard design. | Leveraging the concept of harmonization described for external users through Sign‑in Canada, GCPass will enable authentication and authorization to GC Systems for Internal stakeholders. The digital workplace will uniformly enable the work of public servants, building on a standard design. | ||
| − | [[ | + | |
| + | |||
| + | [[Image:SandD_Internal_Stakeholders-vJune2021.png|SandD_Internal_Stakeholders-vJune2021.png|frameless|900px]] | ||
| + | |||
| + | |||
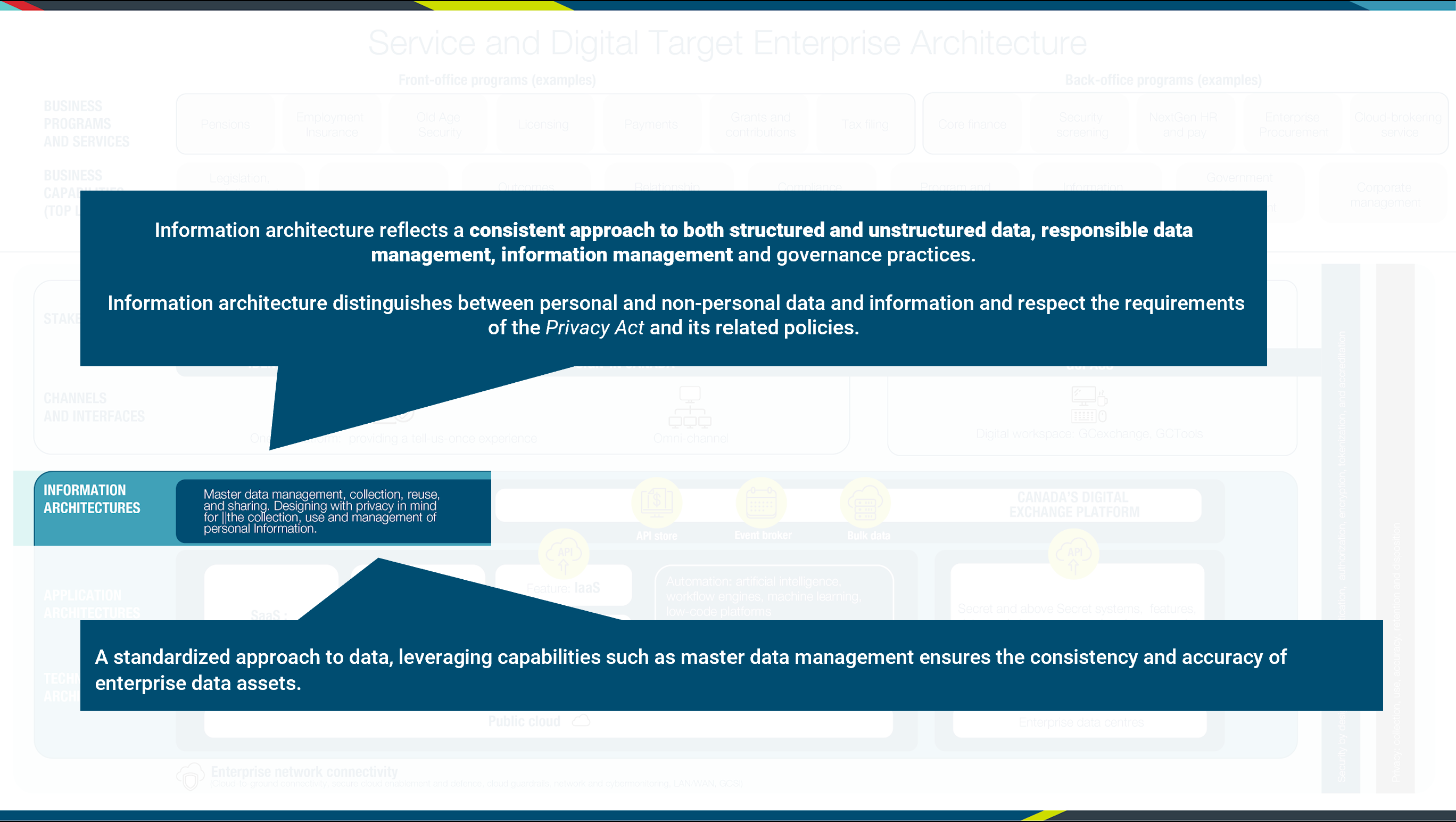
Information architecture is depicted in the following layer. Information architecture best practices and principles aim to support the needs of a business service and business capability orientation. To facilitate effective sharing of data and information across government, information architectures should be designed to reflect a consistent approach to data, such as the adoption of federal and international standards. Information architecture should also reflect responsible data management, information management and governance practices, including the source, quality, interoperability, and associated legal and policy obligations related to the data assets. | Information architecture is depicted in the following layer. Information architecture best practices and principles aim to support the needs of a business service and business capability orientation. To facilitate effective sharing of data and information across government, information architectures should be designed to reflect a consistent approach to data, such as the adoption of federal and international standards. Information architecture should also reflect responsible data management, information management and governance practices, including the source, quality, interoperability, and associated legal and policy obligations related to the data assets. | ||
Information architectures should also distinguish between personal and non‑personal data and information as the collection, use, sharing (disclosure), and management of personal information must respect the requirements of the ''Privacy Act'' and its related policies. | Information architectures should also distinguish between personal and non‑personal data and information as the collection, use, sharing (disclosure), and management of personal information must respect the requirements of the ''Privacy Act'' and its related policies. | ||
| − | [[ | + | |
| + | [[Image:SandD_Information_Architecture-vJune2021.png|SandD_Information_Architecture-vJune2021.png|frameless|900px]] | ||
| + | |||
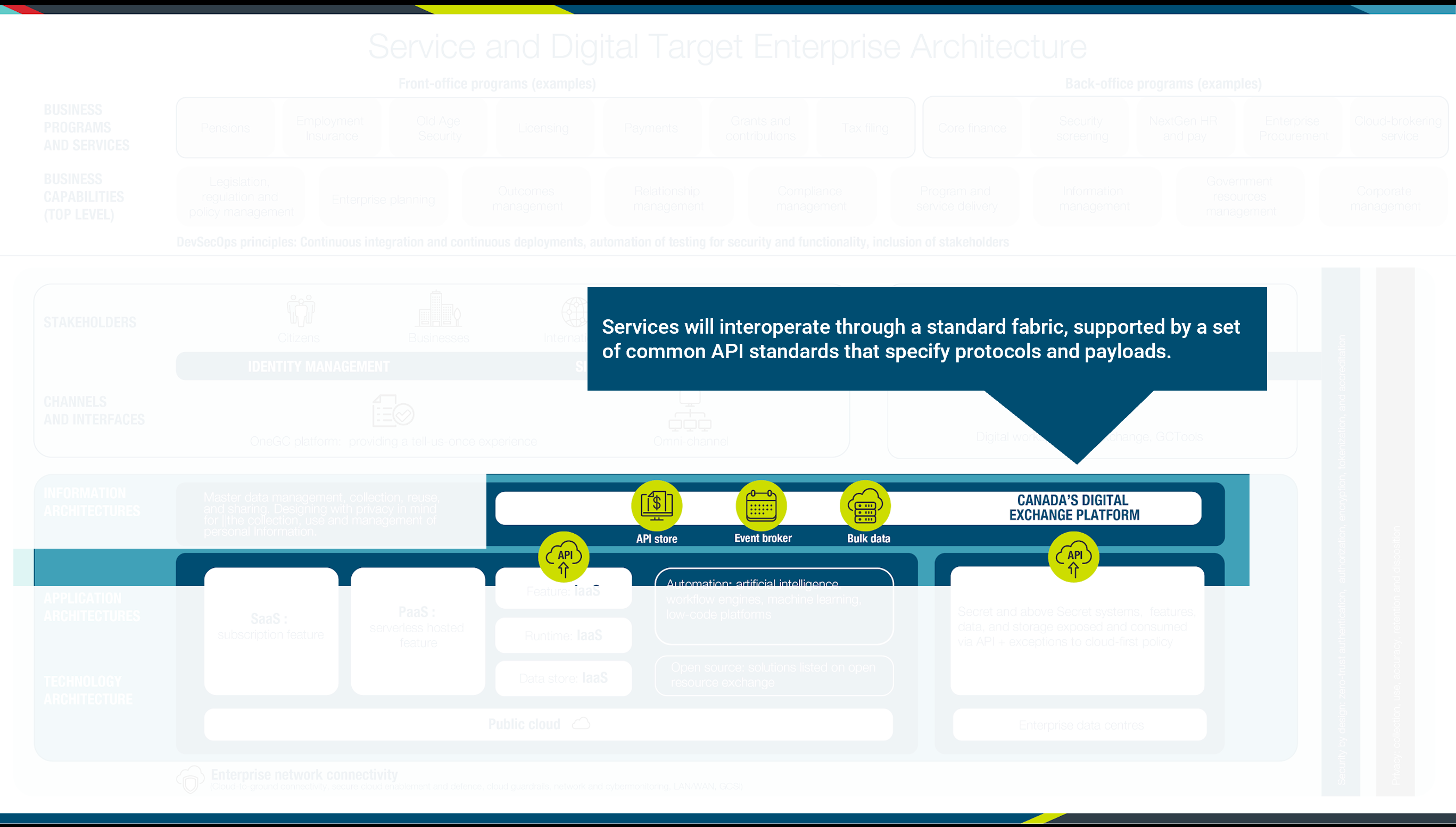
The following layer depicts how services will interoperate through a standard fabric, supported by a set of common API standards specifying protocols and payloads. These services will be published in the API Store to facilitate reuse. APIs will be brokered through an API gateway to manage traffic, ensure version control, and monitor how services are exposed and consumed, either directly, or through a common event broker. Procurement of software as a service (SaaS) offerings will be facilitated through Shared Services Canada’s (SSC’s) Cloud Brokering Service and supported through their managed services. These are services that are available to steward infrastructure that are offered by SSC include database management services, cabling, facility management, transition planning and support, system integration services, and project management, among others. GC business programs and services and their enabling capabilities are built on resources within the application and information landscapes. | The following layer depicts how services will interoperate through a standard fabric, supported by a set of common API standards specifying protocols and payloads. These services will be published in the API Store to facilitate reuse. APIs will be brokered through an API gateway to manage traffic, ensure version control, and monitor how services are exposed and consumed, either directly, or through a common event broker. Procurement of software as a service (SaaS) offerings will be facilitated through Shared Services Canada’s (SSC’s) Cloud Brokering Service and supported through their managed services. These are services that are available to steward infrastructure that are offered by SSC include database management services, cabling, facility management, transition planning and support, system integration services, and project management, among others. GC business programs and services and their enabling capabilities are built on resources within the application and information landscapes. | ||
| − | [[ | + | |
| − | Also highlighted in this layer are automation capabilities such as artificial intelligence and open source solutions listed on an open resource exchange. | + | [[Image:SandD_Interop-vJune2021.png|SandD_Interop-vJune2021.png|frameless|900px]] |
| − | [[ | + | |
| + | Also highlighted in this layer are automation capabilities such as artificial intelligence and open source solutions listed on an open resource exchange. | ||
| + | |||
| + | |||
| + | [[Image:SandD_Application_Architecture_and_Technical_Architecture-vJune2021.png|SandD_Application_Architecture_and_Technical_Architecture-vJune2021.png|frameless|900px]] | ||
| + | |||
| + | |||
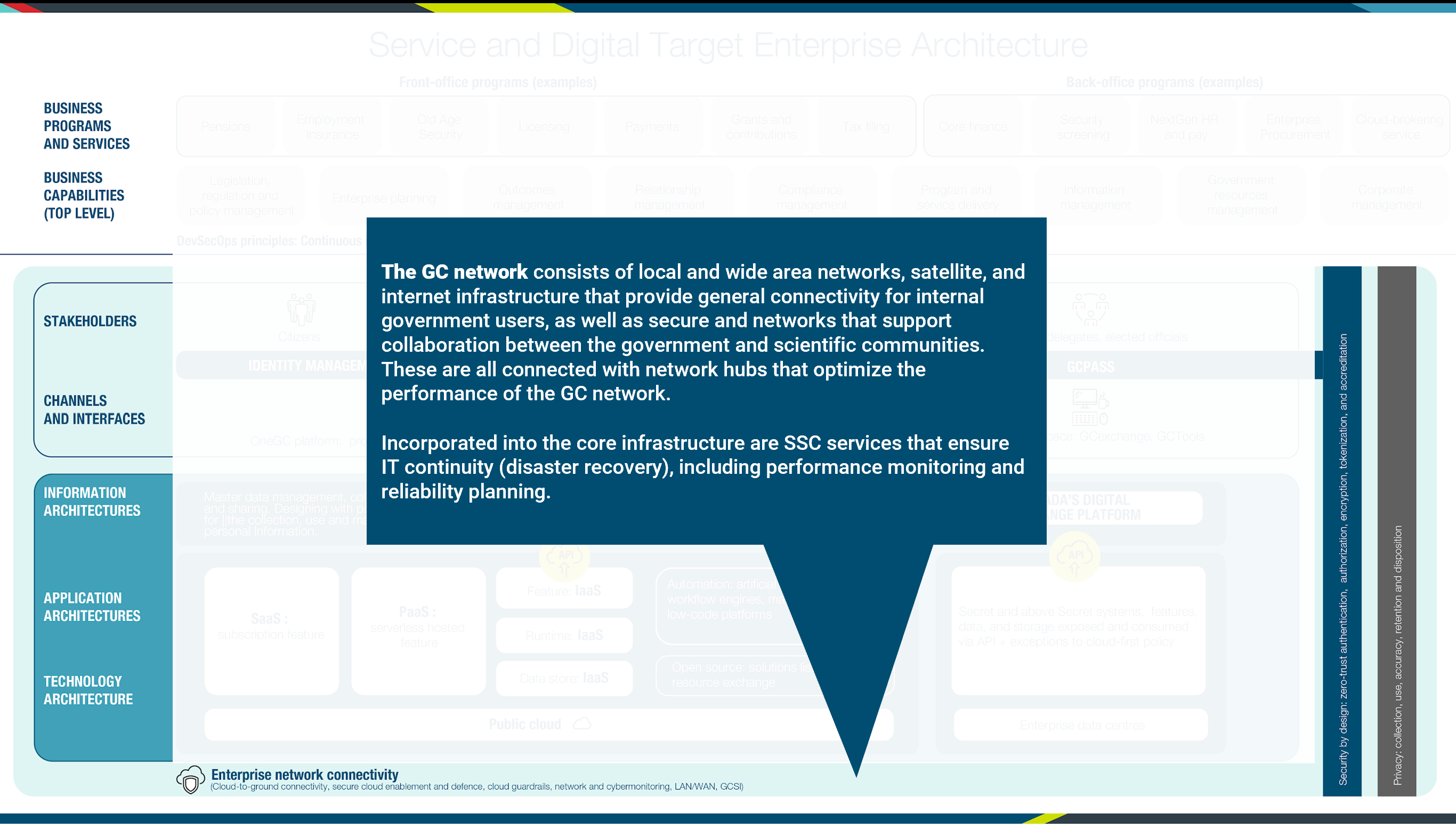
In the bottom‑most view of the Service and Digital Target Enterprise Architecture, the focus is on the technology infrastructure that acts as the glue to bring everything together: the network. The GC network consists of local area network (LAN), wide area network (WAN), satellite, and internet infrastructure that provides general connectivity for internal government users, as well as secure and networks that support collaboration between the government and scientific communities. These are all connected with network hubs that optimize the performance of the GC network. The core infrastructure includes SSC services that ensure IT continuity (disaster recovery), including performance monitoring and reliability planning. | In the bottom‑most view of the Service and Digital Target Enterprise Architecture, the focus is on the technology infrastructure that acts as the glue to bring everything together: the network. The GC network consists of local area network (LAN), wide area network (WAN), satellite, and internet infrastructure that provides general connectivity for internal government users, as well as secure and networks that support collaboration between the government and scientific communities. These are all connected with network hubs that optimize the performance of the GC network. The core infrastructure includes SSC services that ensure IT continuity (disaster recovery), including performance monitoring and reliability planning. | ||
| − | [[ | + | |
| + | [[Image:SandD_Enterprise_Network_Connectivity-vJune2021.png|SandD_Enterprise_Network_Connectivity-vJune2021.png|frameless|900px]] | ||
| + | |||
Security is reflected in the Service and Digital Target Enterprise Architecture diagram as a cross‑cutting factor that spans all horizontal layers. The goal is to ensure security at all architectural levels, from design to implementation to operations; and to ensure authentication, authorization, auditing, monitoring, tokenization, and encryption of all data, whether at rest or in motion. | Security is reflected in the Service and Digital Target Enterprise Architecture diagram as a cross‑cutting factor that spans all horizontal layers. The goal is to ensure security at all architectural levels, from design to implementation to operations; and to ensure authentication, authorization, auditing, monitoring, tokenization, and encryption of all data, whether at rest or in motion. | ||
| − | [[ | + | |
| + | [[Image:SandD_Security_Architecture-vJune2021.png|SandD_Security_Architecture-vJune2021.png|frameless|900px]] | ||
=== Improved outcomes === | === Improved outcomes === | ||
| Line 409: | Line 562: | ||
Ce livre blanc ne vise pas à remplacer les documents actuels qui traitent de l’orientation stratégique du gouvernement en matière de services numériques. | Ce livre blanc ne vise pas à remplacer les documents actuels qui traitent de l’orientation stratégique du gouvernement en matière de services numériques. | ||
| − | === | + | === Le gouvernement numérique === |
| − | + | ||
| + | Le gouvernement numérique accorde la priorité aux citoyens et à leurs besoins. Il est responsable devant ses citoyens et partage les renseignements avec eux. Il les implique dans l’élaboration des politiques et la conception des services. Il valorise l’inclusion et l’accessibilité. Il conçoit des services pour les personnes qui en ont besoin, et non pour les organisations qui les fournissent. | ||
| + | |||
| + | <blockquote>Le gouvernement du Canada est une organisation ouverte et orientée vers les services qui offre des programmes et des services aux citoyens et aux entreprises de manières simples, modernes et efficaces qui sont optimisés pour la voie numérique et disponibles n’importe quand, n’importe où et sur n’importe quel appareil. | ||
| − | + | Le gouvernement du Canada doit se comporter numériquement de façon uniforme afin que tous les Canadiens puissent en profiter | |
| + | <ref>Plan stratégique des opérations numériques : de 2021 à 2024</ref> | ||
=== ''Politique sur les services et le numérique'' === | === ''Politique sur les services et le numérique'' === | ||
| Line 458: | Line 615: | ||
L’architecture intégrée cible des services et du numérique définit un modèle pour l’habilitation numérique des services du gouvernement du Canada qui visent à répondre à plusieurs des défis pressants concernant l’écosystème d’entreprise actuel du GC. Elle cherche à abolir le cloisonnement au sein de l’écosystème actuel du GC en demandant aux ministères d’adopter une perspective axée sur l’utilisateur et la prestation de services lorsqu’ils envisagent de nouvelles solutions de TI ou lorsqu’ils modernisent des solutions plus anciennes. Elle préconise une approche pangouvernementale où les TI sont harmonisées avec les services opérationnels et les solutions prennent appui sur des composantes réutilisables mettant en œuvre des capacités opérationnelles qui sont optimisées de manière à réduire la redondance. Cette réutilisation est rendue possible au moyen d’IPA qui sont partagées dans l’ensemble du gouvernement. Cette approche permet au gouvernement de se concentrer sur l’amélioration de sa prestation de services aux Canadiens tout en relevant les défis liés aux anciens systèmes. | L’architecture intégrée cible des services et du numérique définit un modèle pour l’habilitation numérique des services du gouvernement du Canada qui visent à répondre à plusieurs des défis pressants concernant l’écosystème d’entreprise actuel du GC. Elle cherche à abolir le cloisonnement au sein de l’écosystème actuel du GC en demandant aux ministères d’adopter une perspective axée sur l’utilisateur et la prestation de services lorsqu’ils envisagent de nouvelles solutions de TI ou lorsqu’ils modernisent des solutions plus anciennes. Elle préconise une approche pangouvernementale où les TI sont harmonisées avec les services opérationnels et les solutions prennent appui sur des composantes réutilisables mettant en œuvre des capacités opérationnelles qui sont optimisées de manière à réduire la redondance. Cette réutilisation est rendue possible au moyen d’IPA qui sont partagées dans l’ensemble du gouvernement. Cette approche permet au gouvernement de se concentrer sur l’amélioration de sa prestation de services aux Canadiens tout en relevant les défis liés aux anciens systèmes. | ||
| − | [[ | + | [[Image:Service and Digital Target State Architecture-vJun2021_fr.png|Service_and_Digital_Target_State_Architecture-vJun2021_fr.png|frameless|900px|Architecture intégrée cible des services et du numérique]] |
| + | |||
| + | <div class="mw-collapsible mw-collapsed" data-expandtext="Afficher la version textuelle" data-collapsetext="Cacher la version textuelle"> | ||
| + | <div class="sidetable"> | ||
| + | <table class="wikitable"> | ||
| + | <tr> | ||
| + | <td> | ||
| + | <h1> | ||
| + | Architecture intégrée cible des services et du numérique - Version textuelle | ||
| + | </h1> | ||
| + | </td> | ||
| + | <tr> | ||
| + | <td> | ||
| + | <p>La couche supérieure du diagramme présente des exemples de programmes et de services opérationnels, répartis en deux catégories : les services de première ligne et les services administratifs.</p> | ||
| + | <p>Exemples de programmes et de services opérationnels de première ligne :</p> | ||
| + | <ul> | ||
| + | <li>Pensions</li> | ||
| + | <li>Assurance-emploi</li> | ||
| + | <li>Délivrance de permis</li> | ||
| + | <li>Paiements</li> | ||
| + | <li>Subventions et contributions</li> | ||
| + | <li>Déclaration de revenus</li> | ||
| + | </ul> | ||
| + | <p>Exemples de programmes et de services administratifs :</p> | ||
| + | <ul> | ||
| + | <li>Activités financières principales (TGF)</li> | ||
| + | <li>Filtrage de sécurité</li> | ||
| + | <li>Prochaine génération des RH et de la paye</li> | ||
| + | <li>Approvisionnement intégré</li> | ||
| + | <li>Service de courtage en matière d’informatique en nuage</li> | ||
| + | </ul> | ||
| + | <p>La seconde couche de l’architecture présente les capacités opérationnelles de premier niveau :</p> | ||
| + | <ul> | ||
| + | <li>Gestion des lois, des règlements et des politiques</li> | ||
| + | <li>Planification organisationnelle</li> | ||
| + | <li>Gestion des résultats </li> | ||
| + | <li>Gestion des relations </li> | ||
| + | <li>Gestion de la conformité</li> | ||
| + | <li>Prestation des programmes et des services</li> | ||
| + | <li>Gestion de l’information </li> | ||
| + | <li>Gestion des ressources du gouvernement</li> | ||
| + | <li>Gestion ministérielle </li> | ||
| + | </ul> | ||
| + | <p>La troisième couche présente les principes DevSecOps : Intégration continue et déploiements continus, automatisation des essais pour la sécurité et la fonctionnalité, inclusion des intervenants</p> | ||
| + | <p>La quatrième couche présente les différents intervenants : </p> | ||
| + | <p>Exemples d’intervenants externes :</p> | ||
| + | <ul> | ||
| + | <li>Citoyens</li> | ||
| + | <li>Entreprises</li> | ||
| + | <li>International</li> | ||
| + | <li>Partenariats</li> | ||
| + | </ul> | ||
| + | <p>Exemples d’intervenants internes :</p> | ||
| + | <ul> | ||
| + | <li>Employés, délégués, représentants élus.</li> | ||
| + | </ul> | ||
| + | <p>Deux exemples d’authentification des utilisateurs dans la catégorie des intervenants externes :</p> | ||
| + | <ul> | ||
| + | <li>Gestion de l’identité </li> | ||
| + | <li>Connexion Canada (Authenti-Canada)</li> | ||
| + | </ul> | ||
| + | <p>Le troisième exemple concerne les intervenants internes : GCpass.</p> | ||
| + | <p>La cinquième couche présente les canaux et les interfaces.</p> | ||
| + | <p>Exemples de solutions accessibles à l’externe :</p> | ||
| + | <ul> | ||
| + | <li>Plateforme UnGC : offrir une expérience « Une fois suffit »</li> | ||
| + | <li>Omnicanal </li> | ||
| + | </ul> | ||
| + | <p>Le troisième exemple concerne les utilisateurs internes :</p> | ||
| + | <ul> | ||
| + | <li>Espace de travail numérique : gcéchange, OutilsGC</li> | ||
| + | </ul> | ||
| + | <p>La portion suivante du graphique présente les éléments de l’architecture de l’information, de l’architecture des applications et de l’architecture technologique.</p> | ||
| + | <p><strong>Architecture de l’information </strong></p> | ||
| + | <ul> | ||
| + | <li>Par exemple, la gestion des données de base, la confidentialité (protection des données personnelles) </li> | ||
| + | </ul> | ||
| + | <p>La plateforme d’échange numérique canadienne offre les capacités suivantes :</p> | ||
| + | <ul> | ||
| + | <li>Magasin des API</li> | ||
| + | <li>Courtier en événements </li> | ||
| + | <li>Données en bloc </li> | ||
| + | </ul> | ||
| + | <p>L’<strong>architecture des applications</strong> est divisée en deux catégories en fonction des exigences de sécurité :</p> | ||
| + | <ul> | ||
| + | <li>SaaS : fonctionnalité d’abonnement</li> | ||
| + | <li>PaaS : fonctionnalité d’hébergement sans serveur</li> | ||
| + | <li>L’infrastructure comme service (IaaS) est divisée en trois parties : | ||
| + | <ul> | ||
| + | <li>Fonctionnalité : IaaS</li> | ||
| + | <li>Exécution : IaaS</li> | ||
| + | <li>Stockage des données : IaaS</li> | ||
| + | </ul> | ||
| + | </li> | ||
| + | <li>Les automatisations peuvent être réalisées au moyen d’outils tels que : | ||
| + | <ul> | ||
| + | <li>l’intelligence artificielle</li> | ||
| + | <li>les moteurs de déroulement des opérations</li> | ||
| + | <li>l’apprentissage automatique</li> | ||
| + | <li>les plateformes à peu de codes</li> | ||
| + | </ul> | ||
| + | </li> | ||
| + | <li>Source ouverte : solutions inscrites à l’Échange de ressources ouvert</li> | ||
| + | </ul> | ||
| + | <p>L’information provenant de ces options de l’architecture des applications est transmise à la <strong>plateforme d’échange numérique canadienne</strong> par l’intermédiaire des interfaces de protocole d’application (API).</p> | ||
| + | <p>Systèmes, fonctionnalités, données et stockage classifiés au niveau Secret ou plus et consommés via l’API, et exceptions à la Politique sur l’Informatique en nuage d’abord.</p> | ||
| + | <p><strong>Architecture technique </strong></p> | ||
| + | <p>Le nuage public est l’architecture recommandée pour les solutions qui sont considérées comme Protégé B ou inférieures à un niveau de sécurité déterminé.</p> | ||
| + | <p>Les solutions de niveau supérieur à Protégé B doivent utiliser les centres de données intégrées.</p> | ||
| + | <p>Toutes les couches de l’architecture intégrée cible des services et du numérique reposent sur la <strong>connectivité réseau intégrée</strong>.</p> | ||
| + | <p>Exemples de connectivité réseau intégrée :</p> | ||
| + | <ul> | ||
| + | <li>Connectivité entre le nuage et le sol</li> | ||
| + | <li>Activation et défense du nuage sécurisé </li> | ||
| + | <li>Mesures de protection du nuage</li> | ||
| + | <li>Surveillances des réseaux et cybersurveillance</li> | ||
| + | <li>RL/RE </li> | ||
| + | <li>ISGC </li> | ||
| + | <li>Infrastructure connexe de continuité des activités</li> | ||
| + | </ul> | ||
| + | <p>Le côté droit du graphique présente deux principes fondamentaux :</p> | ||
| + | <ul> | ||
| + | <li>La sécurité à la conception : authentification, autorisation, cryptage, utilisation de jetons et accréditation.</li> | ||
| + | <li>Renseignements personnels : collecte, utilisation, exactitude, conservation et élimination.</li> | ||
| + | </ul> | ||
| + | </td> | ||
| + | |||
| + | </tr> | ||
| + | </table> | ||
| + | </div> | ||
| + | </div><br><br> | ||
| − | L’objectif de | + | L’objectif de l'architecture intégrée cible des services et du numérique est de présenter l’état à venir du gouvernement du Canada en une seule image. Le diagramme est divisé en plusieurs parties, qui sont fondées sur le cadre d’architecture de l’Open Group (TOGAF) expliqué dans une section subséquente. En vertu de ce cadre, les activités, l’information et les données, les applications, la technologie et la sécurité représentent des couches distinctes, ayant chacune ses propres préoccupations et sa propre architecture. |
La couche supérieure du diagramme représente l’architecture opérationnelle. Les programmes de cette couche sont classés comme l’avant-guichet, qui fournit des services directement aux citoyens, aux établissements universitaires et aux entreprises canadiennes, et l’arrière-guichet, qui soutient le gouvernement lui-même. Des exemples de programmes de l’avant-guichet comprennent les services d’assurance-emploi et les services de déclaration de revenus, et des exemples de programmes de l’arrière-guichet comprennent le filtrage de sécurité financière, la paie, l’approvisionnement d’entreprise et la continuité des activités. | La couche supérieure du diagramme représente l’architecture opérationnelle. Les programmes de cette couche sont classés comme l’avant-guichet, qui fournit des services directement aux citoyens, aux établissements universitaires et aux entreprises canadiennes, et l’arrière-guichet, qui soutient le gouvernement lui-même. Des exemples de programmes de l’avant-guichet comprennent les services d’assurance-emploi et les services de déclaration de revenus, et des exemples de programmes de l’arrière-guichet comprennent le filtrage de sécurité financière, la paie, l’approvisionnement d’entreprise et la continuité des activités. | ||
La couche suivante illustre les aspects clés du niveau supérieur du modèle de capacité opérationnelle du GC. Cela tient compte du cadre d’investissement du plan de TI et procure un mécanisme pour déterminer les investissements potentiellement redondants, cerner les possibilités de rationalisation et identifier des occasions pour les solutions d’entreprise. | La couche suivante illustre les aspects clés du niveau supérieur du modèle de capacité opérationnelle du GC. Cela tient compte du cadre d’investissement du plan de TI et procure un mécanisme pour déterminer les investissements potentiellement redondants, cerner les possibilités de rationalisation et identifier des occasions pour les solutions d’entreprise. | ||
| − | [[ | + | [[Image:SandD_Align_with_DOSP-vJune2021_fr.png|SandD_Align_with_DOSP-vJune2021_fr.png|frameless|900px]] |
Dans la couche suivante, les intervenants représentent les participants qui interagissent avec les services du GC, soit à l’externe (comme les citoyens, les entreprises, les organisations avec lesquelles le GC est en partenariat, comme les universités ou les acteurs internationaux), soit à l’interne (comme les employés du GC, les délégués, ou les représentants élus). Ils ont différents besoins en matière d’accès (utilisation de mobiles, de haut-parleurs intelligents à commande vocale, de centres de contact et de kiosques) et d’accessibilité, et peuvent communiquer dans l’une ou l’autre des langues officielles. Connexion Canada fournira une solution cohérente de gestion de l’identité aux citoyens et aux autres intervenants externes pour permettre l’authentification et l’autorisation dans tous les ministères du GC. | Dans la couche suivante, les intervenants représentent les participants qui interagissent avec les services du GC, soit à l’externe (comme les citoyens, les entreprises, les organisations avec lesquelles le GC est en partenariat, comme les universités ou les acteurs internationaux), soit à l’interne (comme les employés du GC, les délégués, ou les représentants élus). Ils ont différents besoins en matière d’accès (utilisation de mobiles, de haut-parleurs intelligents à commande vocale, de centres de contact et de kiosques) et d’accessibilité, et peuvent communiquer dans l’une ou l’autre des langues officielles. Connexion Canada fournira une solution cohérente de gestion de l’identité aux citoyens et aux autres intervenants externes pour permettre l’authentification et l’autorisation dans tous les ministères du GC. | ||
L’objectif est de répondre aux utilisateurs externes qui, en tant que clients, veulent que leurs interactions entre les gouvernements soient gérées avec cohérence, intégrité et confiance afin qu’ils puissent avoir une expérience avantageuse, personnalisée et harmonieuse. | L’objectif est de répondre aux utilisateurs externes qui, en tant que clients, veulent que leurs interactions entre les gouvernements soient gérées avec cohérence, intégrité et confiance afin qu’ils puissent avoir une expérience avantageuse, personnalisée et harmonieuse. | ||
| + | |||
| + | [[Image:SandD_External_Stakeholders-vJune2021_fr.png|SandD_External_Stakeholders-vJune2021_fr.png|frameless|900px]] | ||
Pour assurer la cohérence, chaque canal sera pris en charge par la même architecture. Parmi les divers types de canaux, mentionnons le mobile, le haut-parleur intelligent à commande vocale, le centre d’appels ou le kiosque en personne. Ce concept s’appelle l’approche omnicanal. | Pour assurer la cohérence, chaque canal sera pris en charge par la même architecture. Parmi les divers types de canaux, mentionnons le mobile, le haut-parleur intelligent à commande vocale, le centre d’appels ou le kiosque en personne. Ce concept s’appelle l’approche omnicanal. | ||
| Line 474: | Line 763: | ||
La couche suivante projette l’idée d’un gouvernement axé sur les services, doté d’une approche axée sur l’utilisateur qui place les citoyens et leurs besoins au cœur de notre travail, en utilisant des approches de service « une fois suffit », des services intégrés à l’échelle des programmes et des services du GC d’une manière qui fournit aux Canadiens de l’information en temps réel sur leurs demandes de services. Il s’agit d’une perspective axée sur l’utilisateur et la prestation de services lorsque de nouvelles solutions de TI sont envisagées ou des solutions plus anciennes sont modernisées. Elle s’appuie sur des conseils d’architecture d’entreprise pour concevoir d’abord pour les utilisateurs, en se concentrant sur les besoins des utilisateurs, en utilisant des méthodes agiles, itératives et centrées sur l’utilisateur dans un contexte pangouvernemental. | La couche suivante projette l’idée d’un gouvernement axé sur les services, doté d’une approche axée sur l’utilisateur qui place les citoyens et leurs besoins au cœur de notre travail, en utilisant des approches de service « une fois suffit », des services intégrés à l’échelle des programmes et des services du GC d’une manière qui fournit aux Canadiens de l’information en temps réel sur leurs demandes de services. Il s’agit d’une perspective axée sur l’utilisateur et la prestation de services lorsque de nouvelles solutions de TI sont envisagées ou des solutions plus anciennes sont modernisées. Elle s’appuie sur des conseils d’architecture d’entreprise pour concevoir d’abord pour les utilisateurs, en se concentrant sur les besoins des utilisateurs, en utilisant des méthodes agiles, itératives et centrées sur l’utilisateur dans un contexte pangouvernemental. | ||
| − | [[ | + | |
| + | [[Image:SandD_Internal_Stakeholders-vJune2021_fr.png|SandD_Internal_Stakeholders-vJune2021_fr.png|frameless|900px]] | ||
Tirant parti du concept d’harmonisation décrit pour les utilisateurs externes dans Connexion Canada, GCpass permettra l’authentification et l’autorisation des intervenants internes aux systèmes du GC. Le milieu de travail numérique permettra, de manière uniforme, aux fonctionnaires de faire leur travail, en s’appuyant sur une conception standard. | Tirant parti du concept d’harmonisation décrit pour les utilisateurs externes dans Connexion Canada, GCpass permettra l’authentification et l’autorisation des intervenants internes aux systèmes du GC. Le milieu de travail numérique permettra, de manière uniforme, aux fonctionnaires de faire leur travail, en s’appuyant sur une conception standard. | ||
| Line 480: | Line 770: | ||
La couche suivante illustre l’architecture de l’information, dont les pratiques exemplaires et les principes visent à soutenir les besoins de l’orientation des services opérationnels et des capacités opérationnelles. Afin de faciliter le partage efficace des données et de l’information à l’échelle du gouvernement, les architectures d’information devraient être conçues de manière à tenir compte d’une approche cohérente de la gestion des données, comme l’adoption de normes fédérales et internationales. L’architecture de l’information devrait également refléter une gestion des données et de l’information et des pratiques de gouvernance responsables, notamment la source, la qualité, l’interopérabilité et les obligations juridiques et stratégiques connexes liées aux actifs de données. | La couche suivante illustre l’architecture de l’information, dont les pratiques exemplaires et les principes visent à soutenir les besoins de l’orientation des services opérationnels et des capacités opérationnelles. Afin de faciliter le partage efficace des données et de l’information à l’échelle du gouvernement, les architectures d’information devraient être conçues de manière à tenir compte d’une approche cohérente de la gestion des données, comme l’adoption de normes fédérales et internationales. L’architecture de l’information devrait également refléter une gestion des données et de l’information et des pratiques de gouvernance responsables, notamment la source, la qualité, l’interopérabilité et les obligations juridiques et stratégiques connexes liées aux actifs de données. | ||
| − | [[ | + | [[Image:SandD_Information_Architecture-vJune2021_fr.png|SandD_Information_Architecture-vJune2021_fr.png|frameless|900px]] |
Les architectures d’information devraient également faire la distinction entre les données et les personnels et non personnels, étant donné que la collecte, l’utilisation, le partage (divulgation) et la gestion des renseignements personnels doivent respecter les exigences de la Loi sur la protection des renseignements personnels et de ses politiques connexes. | Les architectures d’information devraient également faire la distinction entre les données et les personnels et non personnels, étant donné que la collecte, l’utilisation, le partage (divulgation) et la gestion des renseignements personnels doivent respecter les exigences de la Loi sur la protection des renseignements personnels et de ses politiques connexes. | ||
| Line 486: | Line 776: | ||
La couche suivante décrit comment les services interagiront par une structure standard et prise en charge par un ensemble de normes communes de l’IPA spécifiant les protocoles et les charges utiles. Ces services seront publiés dans la boutique d’IPA pour faciliter la réutilisation. Les IPA seront négociées au moyen d’une passerelle IPA pour gérer le trafic, assurer le contrôle des versions et surveiller la manière dont les services sont exposés et consommés, soit directement, soit par l’entremise d’un courtier d’événements commun. L’achat d’offres selon le modèle de solution de logiciel comme service (SaaS) sera facilité par le Service de courtage infonuagique de Services partagés Canada (SPC) et soutenu par leurs services gérés. Ces services sont disponibles pour gérer l’infrastructure offerte par SPC, notamment les services de gestion de base de données, le câblage, la gestion des installations, la planification et le soutien de la transition, les services d’intégration de système et la gestion de projet, entre autres. Les programmes et les services opérationnels du GC et leurs capacités habilitantes reposent sur des ressources dans le paysage des applications et de l’information. | La couche suivante décrit comment les services interagiront par une structure standard et prise en charge par un ensemble de normes communes de l’IPA spécifiant les protocoles et les charges utiles. Ces services seront publiés dans la boutique d’IPA pour faciliter la réutilisation. Les IPA seront négociées au moyen d’une passerelle IPA pour gérer le trafic, assurer le contrôle des versions et surveiller la manière dont les services sont exposés et consommés, soit directement, soit par l’entremise d’un courtier d’événements commun. L’achat d’offres selon le modèle de solution de logiciel comme service (SaaS) sera facilité par le Service de courtage infonuagique de Services partagés Canada (SPC) et soutenu par leurs services gérés. Ces services sont disponibles pour gérer l’infrastructure offerte par SPC, notamment les services de gestion de base de données, le câblage, la gestion des installations, la planification et le soutien de la transition, les services d’intégration de système et la gestion de projet, entre autres. Les programmes et les services opérationnels du GC et leurs capacités habilitantes reposent sur des ressources dans le paysage des applications et de l’information. | ||
| − | [[ | + | [[Image:SandD_Interop-vJune2021_fr.png|SandD_Interop-vJune2021_fr.png|frameless|900px]] |
Les capacités d’automatisation, telles que l’intelligence artificielle et les solutions libres répertoriées dans un échange de ressources ouvert, sont également mises en évidence dans cette couche. | Les capacités d’automatisation, telles que l’intelligence artificielle et les solutions libres répertoriées dans un échange de ressources ouvert, sont également mises en évidence dans cette couche. | ||
| − | [[ | + | [[Image:SandD_Application_Architecture_and_Technical_Architecture-vJune2021_fr.png|SandD_Application_Architecture_and_Technical_Architecture-vJune2021_fr.png|frameless|900px]] |
Au niveau inférieur de l’architecture intégrée cible des services et du numérique, l’accent est mis sur l’infrastructure technologique qui sert de ciment pour réunir tous les morceaux : le réseau. Le réseau du GC consiste en un réseau local (LAN), un réseau étendu (WAN), une infrastructure à satellites et Internet qui offre une connectivité générale aux utilisateurs internes du gouvernement, ainsi que des réseaux sécurisés qui soutiennent la collaboration entre le gouvernement et les milieux scientifiques et qui sont tous connectés à des centres de réseau qui optimisent le rendement du réseau du GC. L’infrastructure de base comprend des services de SPC qui assurent la continuité de la TI (récupération en cas de catastrophe), y compris la surveillance du rendement et la planification de la fiabilité. | Au niveau inférieur de l’architecture intégrée cible des services et du numérique, l’accent est mis sur l’infrastructure technologique qui sert de ciment pour réunir tous les morceaux : le réseau. Le réseau du GC consiste en un réseau local (LAN), un réseau étendu (WAN), une infrastructure à satellites et Internet qui offre une connectivité générale aux utilisateurs internes du gouvernement, ainsi que des réseaux sécurisés qui soutiennent la collaboration entre le gouvernement et les milieux scientifiques et qui sont tous connectés à des centres de réseau qui optimisent le rendement du réseau du GC. L’infrastructure de base comprend des services de SPC qui assurent la continuité de la TI (récupération en cas de catastrophe), y compris la surveillance du rendement et la planification de la fiabilité. | ||
| − | [[ | + | [[Image:SandD_Enterprise_Network_Connectivity-vJune2021_fr.png|SandD_Enterprise_Network_Connectivity-vJune2021_fr.png|frameless|900px]] |
La sécurité est reflétée dans le diagramme de l’architecture intégrée cible des services et du numérique comme un facteur commun touchant de nombreux domaines et s’étendant à tous les niveaux horizontaux. L’objectif est d’assurer la sécurité à tous les niveaux architecturaux, de la conception à la mise en œuvre en passant par les opérations, de même que l’authentification, l’autorisation, la vérification, la surveillance, la tokenisation et le chiffrement de toutes les données – qu’elles soient inactives ou en mouvement. | La sécurité est reflétée dans le diagramme de l’architecture intégrée cible des services et du numérique comme un facteur commun touchant de nombreux domaines et s’étendant à tous les niveaux horizontaux. L’objectif est d’assurer la sécurité à tous les niveaux architecturaux, de la conception à la mise en œuvre en passant par les opérations, de même que l’authentification, l’autorisation, la vérification, la surveillance, la tokenisation et le chiffrement de toutes les données – qu’elles soient inactives ou en mouvement. | ||
| − | [[ | + | [[Image:SandD_Security_Architecture-vJune2021_fr.png|SandD_Security_Architecture-vJune2021_fr.png|frameless|900px]] |
=== Amélioration des résultats === | === Amélioration des résultats === | ||
Latest revision as of 13:22, 21 July 2021
The GC EARB information is now maintained on GCX
GC Service and Digital Target Enterprise Architecture Whitepaper[edit | edit source]
Version: 1.33
November 4, 2020
Office of the Chief Information Officer of Canada, Treasury Board of Canada Secretariat, Government of Canada
Executive summary[edit | edit source]
The Service and Digital Target Enterprise Architecture is an enabler for the Policy on Service and Digital.
The Service and Digital Target Enterprise Architecture defines a model for the digital enablement of GC services that address many of the critical challenges with the current GC enterprise ecosystem. It seeks to reduce the silos within the current GC ecosystem by having departments adopt a user‑ and service‑delivery‑centric perspective when considering new IT solutions or modernizing older solutions. It advocates a whole‑of‑government approach where IT is aligned with business services and where solutions are based on reusable components implementing business capabilities optimized to reduce unnecessary redundancy. This reuse is enabled using published application programming interfaces (APIs) shared across government. This approach allows the government to focus on improving its service delivery to Canadians while addressing its challenges with legacy systems.
The Policy on Service and Digital and the Service and Digital Target Enterprise Architecture are guided by a commitment to the guiding principles and best practices of the Government of Canada Digital Standards:
- design with users
- iterate and improve frequently
- work in the open by default
- use open standards and solutions
- address security and privacy risks
- build in accessibility from the start
- empower staff to deliver better services
- be good data stewards
- design ethical services
- collaborate widely
Purpose of this paper[edit | edit source]
This paper is intended to assist federal institutions by providing recommendations on how systems could be implemented over the next several years to provide Canadian citizens with a more cohesive and sustainable digital landscape when interacting with the Government of Canada.
The intended audience is those involved in the delivery of digital services within the Government of Canada including deputy heads and chief information officers. The white paper will also inform suppliers of the enterprise architecture direction, assisting them to align their services when interacting with the government. Finally, the white paper will inform the Canadian public and the international community of the Government of Canada’s enterprise architecture direction for digital transition.
Unless otherwise specified, any example mentioned in this white paper does not represent any existing plans of the Government of Canada.
This white paper is not meant to replace existing documents that address the government’s strategic direction on digital services.
Digital government[edit | edit source]
A digital government puts people and their needs first. It is accountable to its citizens and shares information with them. It involves them when making policies and designing services. It values inclusion and accessibility. It designs services for the people who need them, not for the organizations that deliver them.
The Government of Canada is an open and service-oriented organization that operates and delivers programs and services to people and businesses in simple, modern and effective ways that are optimized for digital and available anytime, anywhere and from any device.
Digitally, the Government of Canada must operate as one to benefit each and every Canadian.[1]
Policy on Service and Digital[edit | edit source]
The Policy on Service and Digital and supporting instruments serve as an integrated set of rules that articulate how Government of Canada organizations manage service delivery, information and data, information technology, and cybersecurity in the digital era. Other requirements, including but not limited to, requirements for privacy, official languages and accessibility, also apply to the management of service delivery, information and data, information management and cybersecurity. Those policies, set out in Section 8, must be applied in conjunction with the Policy on Service and Digital. The Policy on Service and Digital focuses on the client, ensuring proactive consideration at the design stage of key requirements of these functions in the development of operations and services. It establishes an enterprise‑wide, integrated approach to governance, planning and management. Overall, the Policy on Service and Digital advances the delivery of services and the effectiveness of government operations through the strategic management of government information and data and leveraging of information technology.
Section 4.1.2.3 of the Policy on Service and Digital. The Chief Information Officer (CIO) of Canada is responsible for: Prescribing expectations with regard to enterprise architecture.
Section 4.1.2.4 of the Policy on Service and Digital. The Chief Information Officer (CIO) of Canada is responsible for: Establishing and chairing an enterprise architecture review board that is mandated to define current and target architecture standards for the Government of Canada and review departmental proposals for alignment.
Section 4.1.1.1 of the Directive on Service and Digital. The departmental Chief Information Officer (CIO) is responsible for: Chairing a departmental architecture review board that is mandated to review and approve the architecture of all departmental digital initiatives and ensure their alignment with enterprise architectures.
What problems does the Service and Digital Target Enterprise Architecture address?[edit | edit source]
Canadians rely on the federal government for programs and services, which in turn depend on reliable, authoritative data and enabling information technology capabilities to ensure successful delivery. The GC enterprise ecosystem consists of all the information technology used by the Government of Canada and all related environmental factors. The interdependence of all elements with the ecosystem is an essential aspect of what makes it an ecosystem. When discussing information technology within the GC enterprise, one must consider the ecosystem.
What is the issue?[edit | edit source]
The Government of Canada has reached a critical point in its management of the IT systems that are used to enable the delivery of government services. There is an increasing gap between the expectations of Canadian citizens and the ability of the government’s legacy systems to meet those expectations. The total accumulated technical debt associated with legacy systems has reached a tipping point where a simple system‑by‑system replacement approach for individual systems has increasingly become cost and risk prohibitive. The business processes in place to manage the life cycles of these IT systems have become barriers rather than enablers.
How did we get here?[edit | edit source]
| Changing expectations | The rapid evolution of the internet as the ubiquitous platform for service delivery has outstripped the government’s ability to address the demand. Citizens have an increased expectation that all government services will be reliably delivered 24 hours a day, 7 days a week with no artificial differentiation based on which department provides the service. The introduction of new disruptive technologies outside of government can quickly shift the citizen’s expectations as they become aware of new approaches or capabilities. |
| Separate mandates | Government information systems have long mirrored the legislative separation of the functional mandates of departments. In part, this is because the original approaches to a delegation of authority and accountability in legislation did not contemplate the cross‑cutting dependency on information technology that exists today. Beyond authority and accountability, there are legislative constraints on intragovernmental information sharing has historically impeded the integration of business processes across government. Budget and funding models have further reinforced this separation. As a result, there have been limited opportunities to reduce overhead and eliminate redundancies across systems and across government. |
| Evolution of technology | Initially, business process automation within government was implemented as standalone solutions, in many cases monolithic and mainframe solutions. As time passed, the life cycle evolution of individual systems tended to limit their scope to those individual systems; reinforced by a desire to restrict procurement, technical, and change complexity and risk. Current technologies that could be used to implement cohesive enterprise approaches were introduced relatively recently, many years after most government systems were implemented. This gap has been exacerbated over time by the significant difference between the ability of the private sector and the public sector to adopt and leverage new technologies. |
Why is the problem so intractable? Why isn’t “business as usual” a workable way forward?[edit | edit source]
| “Business as usual” not effective | The “business‑as‑usual” approach would be to try to address each legacy system in isolation; in other words, a simplistic system‑by‑system replacement. The costs and risks associated with this approach for major legacy systems are prohibitive in most cases. Dealing with each system in isolation results in missed opportunities for reuse and for eliminating redundancies. In addition, these “big bang” methods dramatically increase business service delivery risk. By the time a significant replacement project is completed, there is also a substantial possibility that the underlying technology is out of date. To mitigate these issues, approaches that allow for an incremental and managed transition over time are suggested. |
| An alternative strategy | One alternative strategy is to incrementally migrate legacy systems by gradually replacing functional elements with new applications and services; in other words, an “evolve‑and‑transcend” strategy. This strategy implements an architectural pattern named the “Strangler Fig,” a metaphor for refactoring rather than replacing legacy systems, by incrementally replacing functional parts of a legacy application slowly and systematically over time, thus spreading costs and mitigating risks. |
Service and Digital Target Enterprise Architecture[edit | edit source]
The Service and Digital Target Enterprise Architecture defines a model for the digital enablement of Government of Canada services that address many of the critical challenges with the current GC enterprise ecosystem. It seeks to reduce the silos within the current GC ecosystem by having departments adopt a user‑ and service‑delivery‑centric perspective when considering new IT solutions or modernizing older solutions. It advocates a whole‑of‑government approach where IT is aligned to business services and solutions are based on reusable components implementing business capabilities optimized to reduce unnecessary redundancy. This reuse is enabled using published APIs shared across government. This approach allows the government to focus on improving its service delivery to Canadians while addressing the challenges with legacy systems.
Service and Digital Target Enterprise Architecture - Text version |
|
The top row of the diagram shows examples of business programs and services, divided into two categories: front-office and back-office. Examples of front-office business programs and services:
Examples of back-office programs and services:
The second row of the architecture shows the top‑level business capabilities:
The third row lists the DevSecOps principles: Continuous integration and continuous deployments, automation of testing for security and functionality, inclusion of stakeholders The fourth row identifies the various stakeholders: Externally, examples include:
Internally, examples include:
Two examples of user authentication are presented under the external stakeholder:
A third example related to the internal stakeholders is GCPass. The fifth row identifies channels and interfaces. Externally accessible solution examples are:
The third example is related to internal users:
The next part of the graphic show the elements of the information architecture, application architecture and technology architecture. Information architecture
Canada’s Digital Exchange Platform offers the following capabilities:
Application architecture is divided into two categories based on security requirements:
The information from these application architecture options is shared back to the Canada’s Digital Exchange Platform via APIs (application programming interfaces). Secret and above Secret systems, features, data, and storage exposed and consumed via API plus exceptions to cloud-first policy. Technology architecture Public cloud is the recommended architecture for solutions that are considered Protected B or below from an identified security level. Solutions above Protected B must use Enterprise Data Centres. All the layers of the Service and Digital Target Enterprise Architecture rely on enterprise network connectivity. Examples of enterprise network connectivity include:
Along the right side of the graphic are two overarching principles:
|
The goal of the Service and Digital Target State Enterprise Architecture is to depict the Government of Canada’s future state in one picture. The diagram is divided into several parts, which are based on The Open Architecture Framework (TOGAF) framework explained in a subsequent section. This framework views business, information and data, applications, technology and security each as separate layers, having their own concerns and architecture.
The top layer of the diagram represents business architecture. The programs in this layer are categorized as front office, which provides services directly to citizens, academic institutions, and Canadian businesses, and back‑office services which support the government itself. Examples of front office programs include Employment Insurance and tax filing services, and examples of back‑end programs include finance security screening, pay, enterprise procurement, and business continuity.
In the following layer, key aspects of the top level of the GC Business Capability Model are depicted. This takes into consideration the IT plan investment framework and provides a mechanism to identify potentially redundant investments across, opportunities for rationalization, and identification of opportunities for enterprise solutions.
In the following layer, stakeholders represent the actors that interact with GC services, either externally (such as citizens, businesses, those which the GC is in partnership with such as universities or international actors), or internally, such as GC employees, delegates, or elected officials. They have different access (use of mobile, voice‑activated smart speakers, contact centres, and kiosks) and accessibility requirements, and may communicate in either official language. Sign‑in Canada will provide a cohesive identity management solution for citizens and other external stakeholders to enable authentication and authorization across all GC departments.
The goal is to respond to external users, who as clients, want interactions across governments to be managed with consistency, integrity, and trust so that they have a beneficial, personalized, and seamless experience.
To ensure consistency, every channel will be supported through the same architecture. Examples of these channels include mobile, voice‑activated smart speaker, call centre, or in‑person kiosk. This concept is called omni‑channel.
The next layer projects the idea of a service‑oriented government, with a user‑centred approach to the business of government that puts citizens and their needs as the primary focus of our work, using “tell‑us‑once” service approaches, integrated services across the GC program and service landscape in a way that provides real‑time information to Canadians about their service applications. It is a perspective centred on users and service delivery when considering new IT solutions or modernizing older solutions. It builds on business architecture guidance to design for users first, focusing on the needs of users, using agile, iterative, and user‑centred methods in a whole-of-government context.
Leveraging the concept of harmonization described for external users through Sign‑in Canada, GCPass will enable authentication and authorization to GC Systems for Internal stakeholders. The digital workplace will uniformly enable the work of public servants, building on a standard design.
Information architecture is depicted in the following layer. Information architecture best practices and principles aim to support the needs of a business service and business capability orientation. To facilitate effective sharing of data and information across government, information architectures should be designed to reflect a consistent approach to data, such as the adoption of federal and international standards. Information architecture should also reflect responsible data management, information management and governance practices, including the source, quality, interoperability, and associated legal and policy obligations related to the data assets.
Information architectures should also distinguish between personal and non‑personal data and information as the collection, use, sharing (disclosure), and management of personal information must respect the requirements of the Privacy Act and its related policies.
The following layer depicts how services will interoperate through a standard fabric, supported by a set of common API standards specifying protocols and payloads. These services will be published in the API Store to facilitate reuse. APIs will be brokered through an API gateway to manage traffic, ensure version control, and monitor how services are exposed and consumed, either directly, or through a common event broker. Procurement of software as a service (SaaS) offerings will be facilitated through Shared Services Canada’s (SSC’s) Cloud Brokering Service and supported through their managed services. These are services that are available to steward infrastructure that are offered by SSC include database management services, cabling, facility management, transition planning and support, system integration services, and project management, among others. GC business programs and services and their enabling capabilities are built on resources within the application and information landscapes.
Also highlighted in this layer are automation capabilities such as artificial intelligence and open source solutions listed on an open resource exchange.
In the bottom‑most view of the Service and Digital Target Enterprise Architecture, the focus is on the technology infrastructure that acts as the glue to bring everything together: the network. The GC network consists of local area network (LAN), wide area network (WAN), satellite, and internet infrastructure that provides general connectivity for internal government users, as well as secure and networks that support collaboration between the government and scientific communities. These are all connected with network hubs that optimize the performance of the GC network. The core infrastructure includes SSC services that ensure IT continuity (disaster recovery), including performance monitoring and reliability planning.
Security is reflected in the Service and Digital Target Enterprise Architecture diagram as a cross‑cutting factor that spans all horizontal layers. The goal is to ensure security at all architectural levels, from design to implementation to operations; and to ensure authentication, authorization, auditing, monitoring, tokenization, and encryption of all data, whether at rest or in motion.
Improved outcomes[edit | edit source]
| Improved digital services that meet citizens’ expectations | Canadian citizens expect reliable digital services that deliver a cohesive user experience.
Their expectation for cohesive user experience is founded on their perception that digital services are being delivered by “one” government and not a collection of departments. By aligning digital service delivery to a common set of services defined within a GC Service Inventory and implemented using reusable components based on a common taxonomy of business capabilities, GC can improve the user experience. Their expectations for reliability and availability are based on their experiences with modern private‑sector internet services. By transitioning to public cloud offerings and infrastructure, GC can leverage private sector investments to meet citizens’ expectations for reliability and availability. |
| Managed costs and improved agility | GC needs to achieve economies of scale realized by modernizing and standardizing IT and by reducing its reliance on costly and outdated technology.
By encouraging the sharing of reusable components based on business capabilities and by leveraging private sector cloud solutions and open source software, GC can both reduce redundancy and help manage costs. By transitioning to an architecture that leverages public cloud offerings and infrastructure, GC can become more agile in responding to changes in business needs, thus delivering future‑ready IT systems that can support the GC digital transformation journey. |
| Engaged and effective workforce | Retention has been identified as a significant IT workforce and talent management issue. The ability to attract and retain new talent is challenging due to the perception that government IT is decades out‑of‑date. Besides the drain on workforce capacity, attrition has negatively impacted morale, the level of engagement and overall workforce effectiveness.
By adopting modern technology and practices, the government is in a better position to attract and retain new talent. Reducing attrition and boosting recent talent acquisition will have a positive impact on morale and foster an engaged and effective workforce. |
Realization practices and principles[edit | edit source]
To realize the GC Enterprise Ecosystem Target Architecture, departments should align with the practices and principles as outlined below, when considering new IT solutions or modernizing older solutions. The architectural approach was developed to facilitate managed incremental transitions but requires more strategic planning on the part of departments to be implemented effectively.
The Government of Canada Enterprise Architecture Framework defined below presents the evaluation criteria being used by GC Enterprise Architecture Review Board to align solutions to the Service and Digital Target Enterprise Architecture. In the interest of effective communication to the architecture community of practice, the material has been organized based on the architectural domains business, information, application, technology, and security.
Enterprise architecture framework[edit | edit source]
The enterprise architecture framework is the criteria used by the Government of Canada enterprise architecture review board and departmental architecture review boards when reviewing digital initiatives to ensure their alignment with enterprise architectures across business, information, application, technology and security domains to support strategic outcomes.
Business architecture[edit | edit source]
Business architecture is a critical aspect for the successful implementation of the GC Enterprise Ecosystem Target Architecture. The architectural strategy advocates whole‑of‑government approach where IT is aligned to business services and solutions are based on re‑useable components implementing business capabilities in order to deliver a cohesive user experience. As such, it is essential that business services, stakeholder needs, opportunities to improve cohesion and opportunities for reuse across government be clearly understood. In the past these elements have not been a priority. It is expected that the IT culture and practices will have to change to make business architecture, in general, and these elements a primary focus.
| Design services digitally from end‑to‑end to meet the Government of Canada users and other stakeholders’ needs |
|
| Architect to be outcome‑driven and strategically aligned to the department and to the Government of Canada |
|
| Promote horizontal enablement of the enterprise |
|
Information architecture[edit | edit source]
Information architecture includes both structured and unstructured data. The best practices and principles aim to support the needs of a business service and business capability orientation. To facilitate effective sharing of data and information across government, information architectures should be designed to reflect a consistent approach to data, such as the adoption of federal and international standards. Information architecture should also reflect responsible data management, information management and governance practices, including the source, quality, interoperability, and associated legal and policy obligations related to the data assets. Information architectures should also distinguish between personal and non‑personal data and information as the collection, use, sharing (disclosure), and management of personal information must respect the requirements of the Privacy Act and its related policies.
| Collect data to address the needs of the users and other stakeholders |
|
| Manage and reuse data strategically and responsibly |
|
| Use and share data openly in an ethical and secure manner |
|
| Design with privacy in mind for the collection, use and management of personal Information |
|
Application architecture[edit | edit source]
Application architecture practices must evolve significantly for the successful implementation of the GC Enterprise Ecosystem Target Architecture. Transitioning from legacy systems based on monolithic architectures to architectures that oriented around business services and based on re‑useable components implementing business capabilities, is a major shift. Interoperability becomes a key element, and the number of stakeholders that must be considered increases.
| Use open source solutions
hosted in public cloud |
|
| Use software as a service (SaaS)
hosted in public cloud |
|
| Design for Interoperability |
|
Technology architecture[edit | edit source]
Technology architecture is an important enabler of highly available and adaptable solutions that must be aligned with the chosen application architecture. Cloud adoption provides many potential advantages by mitigating the logistical constraints that often negatively impacted legacy solutions hosted “on premises.” However, the application architecture must be able to enable these advantages.
| Use cloud first |
|
| Design for performance, availability and scalability |
|
| Follow DevSecOps principles |
|
Security architecture[edit | edit source]
The GC Enterprise Security Architecture program is a government‑wide initiative to provide a standardized approach to developing IT security architecture, ensuring that basic security blocks are implemented across the enterprise as the infrastructure is being renewed.
| Build security into the system life cycle across all architectural layers |
|
| Ensure secure access to systems and services |
|
| Maintain secure operations |
|
GC enterprise ecosystem transition[edit | edit source]
The realization of the Target Service and Digital Target Enterprise Architecture involves dozens of departments and thousands of applications and will involve many interim states. The technical strategy is to incrementally migrate legacy systems by gradually replacing functional elements with new applications and services thus spreading costs and mitigating risks. However, the fundamental nature of the change required demands more than just a technical strategy. To meet Canadians’ expectations for coherent digital service delivery, the government must modernize its policy and practices to support the technological transition to the target enterprise architecture.
Significant progress has already been made, particularly around enabling policy, and work has begun on changing practices, but much work remains.
Enabling policy and regulation[edit | edit source]
To support the change needed, the enabling policy and regulation must be aligned with the strategic direction. The policy must support the required changes and not be a barrier to adoption.
| Integrated policy and directive to enable change | Treasury Board approved a new Policy on Service and Digital and Directive on Service and Digital, which serve as an integrated set of rules that articulate how Government of Canada organizations manage service delivery, information and data, information technology and cybersecurity in the digital era. TBS, through the Office of the Chief Information Officer, developed guidance informed by departmental feedback, reviewed existing Treasury Board policy instruments and identified emerging areas.
TBS, through the Office of the Chief Information Officer, and departments will continue to update guidance and evolve Treasury Board policy instruments. |
GC enterprise focused practices[edit | edit source]
The proposed strategies and architectural principles are significant departures from past practices. Existing departmental practices for the management of IT have locked the government into a cycle that reinforces siloed approaches. The emphasis must shift from isolation and control to collaboration and sharing with the focus on cohesive service delivery to citizens rather than individual mandates.
| GC Target Enterprise Architecture | The Service and Digital Target Enterprise Architecture provides a framework and focal point for making informed decisions on the alignment of business solutions to GC needs. |
| GC Enterprise Architecture Framework | Business, information, application, technology, security, and privacy architecture domains defined by the GC to align solutions to the Service and Digital Target Enterprise Architecture. |
| GC Enterprise Architecture Review Board (GC EARB) | The GC Enterprise Architecture Review Board (GC EARB) provides a governance mechanism to assess if proposed solutions are aligned to the GC Enterprise Architecture Framework. |
| Establishment of GC Enterprise Portfolio Management (GC EPM) | GC Enterprise Portfolio Management (GC EPM) will support integrated planning, prioritization, and optimization of an achievable enterprise investment portfolio by enabling the integration of critical processes and data to inform decision‑making, visibility, and transparency.
|
| Including the business capability perspective in the IT plan | The inclusion of Business Capability Model mapping in the IT plan investment framework provides another mechanism to identify potentially redundant investments in business capabilities across government and opportunities for rationalization and to identify opportunities for enterprise solutions. |
| Including the application capability perspective in the Application Portfolio Management framework | The inclusion of Application Capability Model mapping into the GC Application Portfolio Management framework provides another mechanism to identify overlapping application capabilities and unused functions. Reducing the technology footprint will decrease operational expenses and free up funds for other priorities. |
| GC Cloud Brokering | The GC Cloud Brokering provides a way for departments to obtain public cloud services already vetted. It simplifies the procurement and fulfillment of cloud services by providing a unified process for requesting cloud services that have been thoroughly investigated and approved to comply with the requirements of the GC, as well as to offer central agencies with the visibility of all environments in the cloud. |
| API store | The API store provides a mechanism to publish reusable business capabilities and access to data. |
| Open source software | The Open Source Policy and White Paper guided the use of software, the need for contribution to open source software, the publishing of open source software, and the acquisition of open source software. |
| Digital workspace standards and profiles | GC EARB created standards for internal enterprise services, defined digital workspace user profiles, set departmental consumption of IT services, and sets consumption metrics and limits for each of SSC’s 31 services. |
| Framework for Government‑Wide Data Governance and Stewardship | GC EARB introduced a government‑wide framework for data governance and stewardship, for TBS work on the development of principles, policies and guidance concerning “prescribing enterprise‑wide data standards.” |
GC enterprise IT ecosystem[edit | edit source]
The government has made some limited progress in common application capabilities such as document management and others. However, the predominantly monolithic architectures of departmental applications have effectively limited sharing and reuse across government. The transition towards the GC Target Enterprise Architecture is needed to achieve progress in that area.
| GC enterprise solutions | The establishment of GC enterprise solutions has provided a standard implementation for common application capabilities such as document management (GCDOCS), collaboration (GCshare), and Customer Relationship Management CRM (GCcase). |
| GC enterprise digital workplace platform | The acquisition of Office 365 provides a secure cloud‑based, software‑as‑a‑service solution for the digital workspace. Its rollout will provide a coherent user experience across government over multiple devices and channels. |
| Sign‑in Canada | Sign‑in Canada is a proposal for a unified authentication mechanism for all government digital engagement with citizens. Users would only need to tell Sign‑in Canada one time who they are, and subsequently, there would be no need to sign up multiple times to access different government services. |
| GC internal authentication | Internally within the government, GCPass, when fully implemented, will provide streamlined secure and appropriate access to GC systems for public servants. |
| Canadian Geospatial Platform | Natural Resources Canada (NRCan) is launching the Canadian Geospatial Platform (CGP) as the next evolution of the Federal Geospatial Platform, with the transition to a new architecture for a GC enterprise platform that will enable NRCan to host solutions from other GC departments in a platform‑as‑a‑service model. CGP will continue to be aligned with the principles of open government and open data and thus is currently configured for unclassified data only. |
Summary[edit | edit source]
The Government of Canada is responding to the challenge of meeting Canadian citizens’ evolving expectations for cohesive digital service delivery in the face of aging IT systems and rising technical debt. To meet this challenge, the government is changing the way it approaches acquiring new solutions and modernizing older solutions. By advocating a whole‑of‑government approach where IT is aligned to business services, and solutions are based on reusable components implementing business capabilities optimized to reduce unnecessary redundancy, it is maintaining a clear focus on improving its service delivery to Canadians while addressing the technical challenges with its legacy systems.
The future digital landscape of the Government of Canada will be more agile in responding to changes in business needs and better able to leverage new disruptive technologies. Significant progress has already been made, particularly in enabling policy, and work has begun on changing practices, but much work remains.
An ongoing commitment is needed from everyone involved in digital service delivery to be engaged and active participants in these changes by adopting:
- a service‑centric perspective; and focusing on delivering a cohesive user experience for our citizens
- a business capability‑centric perspective when considering solutions, and embracing sharing and reuse
- a whole‑of‑government perspective; and embracing change
This white paper is just another small step of the larger journey.
- ↑ Digital Operations Strategic Plan: 2021–2024 - Canada.ca