Difference between revisions of "GC Enterprise Architecture/Framework/DataGuide"
m |
m |
||
| (21 intermediate revisions by 4 users not shown) | |||
| Line 1: | Line 1: | ||
| + | {{OCIO GCEA Header}} | ||
<multilang> | <multilang> | ||
| − | @en| | + | @en|__TOC__ |
== Information architecture == | == Information architecture == | ||
| − | Information architecture | + | Information architecture is defined as the management and organization of data for a business. The best practices and principles aim to support the needs of a business service and business capability orientation. To facilitate effective sharing of data and information across government, information architectures should be designed to reflect a consistent approach to both structured and unstructured data, such as the adoption of federal and international standards. Information architecture should also reflect responsible data management, information management and governance practices, including the source, quality, interoperability, and associated legal and policy obligations related to the data assets. Information architectures should also distinguish between personal and non‑personal data. How personal information is treated such as its collection, use, sharing (disclosure), and management must respect the requirements of the ''[https://laws-lois.justice.gc.ca/eng/ACTS/P-21/index.html Privacy Act]'' and its related policies. Under this paragraph is a model of Data Architecture demonstrating the core components that data flows through in an enterprise to obtain insights and analytics. |
| + | |||
| + | [[File:Generic Data Architecture Model.png|800px|center]] | ||
| + | |||
| + | Data Product: A service or device that collects, processes, and stores data for a business. Data producers also monitor the data obtains to ensure the quality of the data asset. | ||
| + | |||
| + | Data Source: A data source is made up of fields and groups. In the same way that folders on your hard disk contain and organize your files, fields contain the data that users enter into forms that are based on your form template, and groups contain and organize those fields. | ||
| + | |||
| + | Data Integration: Data integration is the process for combining data from several disparate sources to provide users with a single, unified view. | ||
| + | Integration is the act of bringing together smaller components into a single system so that it's able to function as one. And in an IT context, it's stitching together different data subsystems to build a more extensive, more comprehensive, and more standardized system between multiple teams, helping to build unified insights for all. | ||
| + | |||
| + | Data Lake: A data lake is a centralized repository that ingests and stores large volumes of data in its original form. The data can then be processed and used as a basis for a variety of analytic needs. Due to its open, scalable architecture, a data lake can accommodate all types of data from any source, from structured (database tables, Excel sheets) to semi-structured (XML files, webpages) to unstructured (images, audio files, tweets), all without sacrificing fidelity. The data files are typically stored in staged zones—raw, cleansed, and curated—so that different types of users may use the data in its various forms to meet their needs. Data lakes provide core data consistency across a variety of applications, powering big data analytics, machine learning, predictive analytics, and other forms of intelligent action. | ||
| + | |||
| + | Data Mart: A data warehouse is a system that aggregates data from multiple sources into a single, central, consistent data store to support data mining, artificial intelligence (AI), and machine learning—which, ultimately, can enhance sophisticated analytics and business intelligence. Through this strategic collection process, data warehouse solutions consolidate data from the different sources to make it available in one unified form. | ||
| + | |||
| + | A data mart (as noted above) is a focused version of a data warehouse that contains a smaller subset of data important to and needed by a single team or a select group of users within an organization. A data mart is built from an existing data warehouse (or other data sources) through a complex procedure that involves multiple technologies and tools to design and construct a physical database, populate it with data, and set up intricate access and management protocols. | ||
| + | |||
| + | Data Consumers: Data consumers are services or applications, such as Power BI or Dynamics 365 Customer Insights, that read data in Common Data Model folders in Data Lake Storage Gen2. Other data consumers include Azure data-platform services (such as Azure Machine Learning, Azure Data Factory, and Azure Databricks) and turnkey software as a service (SaaS) applications (such as Dynamics 365 Sales Insights). A data consumer might have access to many Common Data Model folders to read content throughout the data lake. If a data consumer wants to write back data or insights that it has derived from a data producer, the data consumer should follow the pattern described for data producers above and write within its own file system. | ||
| + | |||
| + | Outlined in the points below, are objectives to be fulfilled in order to maintain information architecture standards. | ||
=== Collect data to address the needs of the users and other stakeholders === | === Collect data to address the needs of the users and other stakeholders === | ||
| − | * assess | + | |
| + | Collecting data is an important activity to define a scope that meets all stakeholder requirements. Stakeholder requirements refer to what is expected out of an activity such as business capabilities being addressed, resource requirements, and timeline. Assessing these requirements will make it easier to draw boundaries around the activity and ensure that a high-quality result is being delivered. To track and demonstrate that requirements are being fulfilled throughout the activity, data must be collected first. Data collection is a systematic process of gathering observations for the purposes of addressing programs or policies in a business or the government. | ||
| + | |||
| + | The initial step to collecting data is to identify what information needs to be gathered and the source of data. For example, in creating a centralized system for a patient database at a hospital, once the user requirements are identified, the process of how data is collected should be considered. There are several ways of collecting data, such as interviews, surveys/ questionnaires, workshops, and observing consumers. The goal is to gather these requirements and prioritize them. Questions for surveys or interviews must be consistent to keep the data organized and easier to prioritize. The data itself should be reusable and easily transportable to another system to save time and money. | ||
| + | |||
| + | * assess program objectives based on data requirements, as well as users, business and stakeholder needs | ||
<b>How to achieve:</b> | <b>How to achieve:</b> | ||
* Summarize how the architecture meets the data needs of the users and other key stakeholders including: | * Summarize how the architecture meets the data needs of the users and other key stakeholders including: | ||
* How does the data asset contribute to outcomes/needs of the user and other stakeholders | * How does the data asset contribute to outcomes/needs of the user and other stakeholders | ||
* Gaps in the existing data assets to meet the needs of the users and other stakeholders and how the architecture addresses these gaps | * Gaps in the existing data assets to meet the needs of the users and other stakeholders and how the architecture addresses these gaps | ||
| − | * Gaps in data collection and analysis | + | * Gaps in data collection and analysis and how the architecture is addressing it so that department can ensure that we are serving the members of our society |
| − | * Alignment to the data foundation of the | + | * Alignment to the data foundation of the departmental information/data architecture practice |
| − | * Alignment to the theoretical foundation of the | + | * Alignment to the theoretical foundation of the departmental information/data architecture practice |
<b>Tools:</b> | <b>Tools:</b> | ||
| Line 30: | Line 55: | ||
* Supporting Performance Information Profiles (PIPs) used to assess a progress towards target and broader objectives | * Supporting Performance Information Profiles (PIPs) used to assess a progress towards target and broader objectives | ||
<b>Tools:</b> | <b>Tools:</b> | ||
| − | * Value Stream (Value Item and Value Proposition – Context on | + | * Value Stream (Value Item and Value Proposition – Context on what we measure) |
| − | * KPI Linked to benefits outcomes and objectives | + | * KPI (Linked to benefits, outcomes and objectives) |
* reuse existing data assets where permissible and only acquire new data if required | * reuse existing data assets where permissible and only acquire new data if required | ||
<b>How to achieve:</b> | <b>How to achieve:</b> | ||
| − | * Summarize | + | * Summarize reusability of the architecture’s data assets given: |
* Context of data assets and user and stakeholder needs | * Context of data assets and user and stakeholder needs | ||
* Data quality and fit for purpose | * Data quality and fit for purpose | ||
| − | * Privacy and Security | + | * Privacy and Security Regulatory Framework |
<b>Tools:</b> | <b>Tools:</b> | ||
* Legislative / Regulations | * Legislative / Regulations | ||
| Line 45: | Line 70: | ||
<b>How to achieve:</b> | <b>How to achieve:</b> | ||
* Summarize how the architecture meets the data quality requirements of third-party sources: | * Summarize how the architecture meets the data quality requirements of third-party sources: | ||
| − | * Data quality meets | + | * Data quality meets fit for purpose |
* Data quality dimensions including: | * Data quality dimensions including: | ||
* Relevance, | * Relevance, | ||
| Line 55: | Line 80: | ||
* Data quality mechanism | * Data quality mechanism | ||
<b>Tools:</b> | <b>Tools:</b> | ||
| − | * Data Foundation – Implement (Leverage the | + | * Data Foundation – Implement (Leverage the standard definition) |
* Data Catalogue | * Data Catalogue | ||
* Benefits Knowledge hub | * Benefits Knowledge hub | ||
| Line 62: | Line 87: | ||
=== Manage and reuse data strategically and responsibly === | === Manage and reuse data strategically and responsibly === | ||
| + | |||
| + | Data architecture is defined as the management of data by translating the business requirements into technical requirements for an organization. The management of data refers to the collection, storage, and usage of data in an information system. Furthermore, data management and the direction of its flow are guided by various framework of models, policies, rules, and standards used by the organization. They both provide a foundation to work efficiently with data as well as to govern data access by establishing roles, responsibilities and accountabilities. For example, an organization may have a system that they have conceptualized to store information. To ensure that the system succeeds in doing so, it must satisfy adequate data storage capabilities as well as role-based access functionalities. To assess said capabilities, an organization should review the system’s functions and compare them to the user/stakeholder requirements to ensure adequate support to organizational policies. The system must also ensure data lineage is maintained to be able to trace back data to its origin. | ||
| + | |||
| + | Data architectures define and set data standards and principles. To accomplish the process of translating business requirements into technical requirements, some duties may entail creating blueprints for data flow and data management as well as assessing potential data sources. Plans may be devised to make these sources accessible to all employees and keep them protected according to existing security and privacy policies. Data architecture identifies [data] consumers within an organization, then align with their varying requirements and allow them access at any moment with a synchronous process to deliver usable data. For example, within a hospital, nurses and doctors utilize and work with patient data. Depending on who it is, some may be required to update data such as illness or prescribed medicine, and some should view and direct based on the data, to coordinate rooms and available medical machines. It is a necessity to have a centralized system, or systems that are interoperable, with varying features and permissions to be able to access all this information at any given time. Otherwise, if non-interoperable multiple systems for different data sets were used, it would be difficult to maintain the flow of data throughout the hospital, which would cause loss opportunities of time-sensitive action that can harm patients in critical conditions. | ||
| + | |||
* define and establish clear roles, responsibilities, and accountabilities for data management | * define and establish clear roles, responsibilities, and accountabilities for data management | ||
<b>How to achieve:</b> | <b>How to achieve:</b> | ||
| − | * Summarize how the architecture assists in | + | * Summarize how the architecture assists in defining key data management roles and their responsibilities to ensure data is correct, consistent, and complete including: |
* Identifies the data steward responsibilities; | * Identifies the data steward responsibilities; | ||
* Identifies the data consumer responsibilities, and; | * Identifies the data consumer responsibilities, and; | ||
| Line 81: | Line 111: | ||
<b>Tools:</b> | <b>Tools:</b> | ||
* Target state (solution data elements) | * Target state (solution data elements) | ||
| − | * Data Foundation – Implement (Leverage the | + | * Data Foundation – Implement (Leverage the standard definition) |
* Data Catalogue | * Data Catalogue | ||
* Benefits Knowledge hub | * Benefits Knowledge hub | ||
| Line 107: | Line 137: | ||
<b>Tools:</b> | <b>Tools:</b> | ||
* Target State | * Target State | ||
| − | * Data Foundation – Implement (Leverage the | + | * Data Foundation – Implement (Leverage the standard definition) |
* Data Catalogue | * Data Catalogue | ||
* Benefits Knowledge hub | * Benefits Knowledge hub | ||
| Line 114: | Line 144: | ||
* contribute to and align with enterprise and international data taxonomy and classification structures to manage, store, search and retrieve data | * contribute to and align with enterprise and international data taxonomy and classification structures to manage, store, search and retrieve data | ||
<b>How to achieve:</b> | <b>How to achieve:</b> | ||
| − | * Summarize the | + | * Summarize the alignment to departmental/GC: |
* Data taxonomy structure | * Data taxonomy structure | ||
* Data classification structure | * Data classification structure | ||
<b>Tools:</b> | <b>Tools:</b> | ||
| − | * Data Foundation – Implement (Leverage the | + | * Data Foundation – Implement (Leverage the standard definition) |
* Data Catalogue | * Data Catalogue | ||
* Theoretical Foundation | * Theoretical Foundation | ||
| Line 125: | Line 155: | ||
=== Use and share data openly in an ethical and secure manner === | === Use and share data openly in an ethical and secure manner === | ||
| − | * share data openly by default as per the ''Directive on Open Government and Digital Standards'', while respecting security and privacy requirements; data shared should adhere to existing enterprise and international standards, including on data quality and ethics | + | |
| + | Organizations should be able to adhere to ethical guidelines on data sharing to address and meet emerging standards and legislative requirements. It is an organization’s responsibility to apply transparency and to respect how data is used within the organization. Using and sharing data in an ethical manner can build trust between the public and the organization. Failing to prioritize privacy, security, consent, and ownership of data can negatively harm an organization’s reputation and credibility (and create the risk of extinction). To share data ethically and legally, an organization must request participants’ consent. How personal data will be used and shared must be communicated transparently to avoid misleading anyone. Furthermore, to keep data private and more generic for future sharing purposes, it can be anonymized by removing participant’s tombstone information such as name, address, and occupation. If data anonymization is considered, it is ideal to plan it during the collection phase. It is necessary to inform third party readers when data has been anonymized. This may be done by using markings in the text for contents that have been previously removed. Additionally, an original data repository copy should always be kept separately and secured to keep a record of all data that has been anonymized in the final product. Third party readers should have valid reasons and the right qualifications to access the original data to ensure data is treated in a careful manner. Data must not be shared when: there is a conflict of interest with the need to protect personal identities; when an organization does not have ownership of the data; and when releasing the data presents a security risk. | ||
| + | |||
| + | * share data openly by default as per the ''Directive on [https://www.tbs-sct.canada.ca/pol/doc-eng.aspx?id=28108 Open Government] and Digital Standards'', while respecting security and privacy requirements; data shared should adhere to existing enterprise and international standards, including on data quality and ethics | ||
<b>How to achieve:</b> | <b>How to achieve:</b> | ||
* Summarize how the architecture supports sharing data openly by default as per Directive on Open Government and Digital Standards given: | * Summarize how the architecture supports sharing data openly by default as per Directive on Open Government and Digital Standards given: | ||
| − | * Existing | + | * Existing departmental and GC data standards and policies |
* International data standards; and the Privacy Act, | * International data standards; and the Privacy Act, | ||
* Fitness for purpose | * Fitness for purpose | ||
* Ethics | * Ethics | ||
<b>Tools:</b> | <b>Tools:</b> | ||
| − | * Data Foundation – Implement (Leverage the | + | * Data Foundation – Implement (Leverage the standard definition) |
* Data Catalogue | * Data Catalogue | ||
* Benefits Knowledge Hub | * Benefits Knowledge Hub | ||
| Line 145: | Line 178: | ||
* ensure data formatting aligns to existing enterprise and international standards on interoperability; where none exist, develop data standards in the open with key subject matter experts | * ensure data formatting aligns to existing enterprise and international standards on interoperability; where none exist, develop data standards in the open with key subject matter experts | ||
<b>How to achieve:</b> | <b>How to achieve:</b> | ||
| − | * Summarize how the architecture | + | * Summarize how the architecture utilises existing enterprise and international data standards |
* Summarize how the architecture has developed any data standards through open collaboration with key subject matter experts and the Enterprise Data Community of Practice. | * Summarize how the architecture has developed any data standards through open collaboration with key subject matter experts and the Enterprise Data Community of Practice. | ||
<b>Tools:</b> | <b>Tools:</b> | ||
| Line 156: | Line 189: | ||
* ensure that combined data does not risk identification or re‑identification of sensitive or personal information | * ensure that combined data does not risk identification or re‑identification of sensitive or personal information | ||
<b>How to achieve:</b> | <b>How to achieve:</b> | ||
| − | * Summarize how the architecture ensures the aggregation and combing of data does not pose a risk to | + | * Summarize how the architecture ensures the aggregation and combing of data does not pose a risk to information sensitivity or personal information |
=== Design with privacy in mind for the collection, use and management of personal Information === | === Design with privacy in mind for the collection, use and management of personal Information === | ||
| + | |||
| + | Keeping data protected in a company is important to keep sensitive information such as industry knowledge and personal information private and solely on a company server. It is a legal requirement for companies as outlined in the Privacy Act. Furthermore, when companies work with clients who are investing their money and time, it is expected for them to ensure that data will be held safely at the minimum. Data privacy can protect the reputation and credibility of a company as unprotected data can often fall victim to hackers and outside sources. For example, within a hospital, patient personal information should be kept secure and away from the public. This is expected of hospitals and failing to comply can result in legal and ethical issues. Additionally, it would be dangerous for strangers to get access to patient information such as their address and health implications. | ||
| + | |||
* ensure alignment with guidance from appropriate institutional ATIP Office with respect to interpretation and application of the ''Privacy Act'' and related policy instruments | * ensure alignment with guidance from appropriate institutional ATIP Office with respect to interpretation and application of the ''Privacy Act'' and related policy instruments | ||
<b>How to achieve:</b> | <b>How to achieve:</b> | ||
| Line 224: | Line 260: | ||
* Business Process Model | * Business Process Model | ||
| − | @fr| | + | @fr|__TOC__ |
| − | ==== | + | == ARCHITECTURE DE L'INFORMATION == |
| + | |||
L’architecture d’information comporte à la fois des données structurées et des données non structurées. Les pratiques exemplaires et les principes visent à soutenir les besoins de l’orientation des services opérationnels et des capacités opérationnelles. Afin de faciliter le partage efficace des données et de l’information à l’échelle du gouvernement, les architectures d’information devraient être conçues de manière à refléter une approche uniforme des données, comme l’adoption de normes fédérales et internationales. L’architecture de l’information devrait également refléter une gestion des données et de l’information et des pratiques de gouvernance responsables, notamment la source, la qualité, l’interopérabilité et les obligations juridiques et stratégiques connexes liées aux actifs de données. Les architectures d’information devraient également faire la distinction entre les données et l’information personnelles et non personnelles, étant donné que la collecte, l’utilisation, le partage (divulgation) et la gestion des renseignements personnels doivent respecter les exigences de la Loi sur la protection des renseignements personnels et de ses politiques connexes. | L’architecture d’information comporte à la fois des données structurées et des données non structurées. Les pratiques exemplaires et les principes visent à soutenir les besoins de l’orientation des services opérationnels et des capacités opérationnelles. Afin de faciliter le partage efficace des données et de l’information à l’échelle du gouvernement, les architectures d’information devraient être conçues de manière à refléter une approche uniforme des données, comme l’adoption de normes fédérales et internationales. L’architecture de l’information devrait également refléter une gestion des données et de l’information et des pratiques de gouvernance responsables, notamment la source, la qualité, l’interopérabilité et les obligations juridiques et stratégiques connexes liées aux actifs de données. Les architectures d’information devraient également faire la distinction entre les données et l’information personnelles et non personnelles, étant donné que la collecte, l’utilisation, le partage (divulgation) et la gestion des renseignements personnels doivent respecter les exigences de la Loi sur la protection des renseignements personnels et de ses politiques connexes. | ||
| − | + | ||
| − | + | === Recueillir les données requises pour répondre aux besoins des utilisateurs et des autres intervenants === | |
| − | + | ||
| − | * Évaluer les objectifs du programme fondés sur les exigences relatives aux données, ainsi que les besoins des utilisateurs, des entreprises et des intervenants | + | ==== * Évaluer les objectifs du programme fondés sur les exigences relatives aux données, ainsi que les besoins des utilisateurs, des entreprises et des intervenants ==== |
| − | * Recueillir seulement l’ensemble minimal de données nécessaire pour appuyer une politique, un programme ou un service | + | |
| − | * Réutiliser les actifs de données existants lorsque cela est permis et acquérir de nouvelles données seulement si cela est nécessaire | + | <b>Comment y parvenir :</b> |
| − | * Veiller à ce que les données recueillies, y compris celles provenant de sources tierces, soient de grande qualité | + | * Résumer comment l'architecture répond aux besoins de données des utilisateurs et des autres parties prenantes clés, notamment : |
| − | + | * Comment l'actif de données contribue-t-il aux résultats/besoins de l'utilisateur et des autres parties prenantes | |
| − | + | * Lacunes dans les actifs de données existants pour répondre aux besoins des utilisateurs et des autres parties prenantes et comment l'architecture comble ces lacunes | |
| − | + | * Lacunes dans la collecte et l'analyse des données et comment l'architecture y répond afin que le département puisse s'assurer que nous servons les membres de notre société | |
| − | * Définir et établir clairement les rôles, les responsabilités et la responsabilisation en matière de gestion des données; | + | * Alignement sur la base de données de la pratique d'architecture de l'information/des données du département |
| − | * Identifier et documenter la lignée des actifs de données | + | * Alignement sur le fondement théorique de la pratique de l'architecture de l'information/des données du département |
| − | * Définir les calendriers de conservation et d’élimination conformément à la valeur opérationnelle ainsi qu’aux politiques et aux lois applicables en matière de protection des renseignements personnels et de sécurité | + | |
| − | * Veiller à ce que les données soient gérées pour permettre, dans la mesure du possible, leurs interopérabilité, réutilisation et partage au sein des ministères et avec d’autres ministères à l’échelle du gouvernement afin d’éviter les répétitions et maximiser l’utilité, tout en respectant les exigences en matière de sécurité et de protection des renseignements personnels | + | <b>Outils :</b> |
| − | * Contribuer à la taxonomie et aux structures de classification des données d’entreprise et internationales afin de gérer, de stocker, de chercher et de récupérer des données | + | * Pour Data Foundation – Mettre en œuvre : |
| − | + | * Catalogue de données | |
| − | + | * Bénéfices Centre de connaissances | |
| − | + | * Data Lake (croissance) | |
| − | * Partager les données de façon ouverte par défaut conformément à la Directive sur le gouvernement ouvert et les normes numériques, tout en respectant les exigences en matière de sécurité et de protection des renseignements personnels. Les données partagées doivent respecter les normes organisationnelles et internationales existantes, notamment en matière de qualité et d’éthique des données; | + | * Science des données et plateforme machine |
| − | * Veiller à ce que le formatage des données soit conforme aux normes institutionnelles et internationales en matière d’interopérabilité. Quand aucune norme n’existe, élaborer des normes de données ouvertes avec des experts clés en la matière | + | * Exigences des parties prenantes |
| − | * S’assurer que les données combinées ne comportent pas de risque d’identification ou de réidentification de renseignements sensibles ou personnels | + | * Exigences de la solution |
| − | + | ||
| − | + | ==== * Recueillir seulement l’ensemble minimal de données nécessaire pour appuyer une politique, un programme ou un service ==== | |
| − | + | ||
| − | * Assurer l’harmonisation avec les directives du Bureau de l’accès à l’information et de la protection des renseignements personnels (AIPRP) approprié de l’établissement en ce qui concerne l’interprétation et l’application de la Loi sur la protection des renseignements personnels et des instruments de politique connexes; | + | <b>Comment y parvenir :</b> |
| − | * Évaluer les initiatives pour déterminer si les renseignements personnels seront recueillis, utilisés, communiqués, conservés, partagés et éliminés | + | * Résumez comment l'architecture s'aligne pour « collecter avec un objectif », y compris : |
| − | * Recueillir des renseignements personnels seulement s’ils ont un lien direct avec le fonctionnement des programmes ou des activités | + | * Ce qui est nécessaire (par opposition à ce qui est suffisant) pour répondre au besoin des parties prenantes |
| − | * Informer les personnes des fins de la collecte au point de collecte en incluant un avis de confidentialité | + | * Soutenir les profils d'information sur les performances (PIP) utilisés pour évaluer les progrès vers la cible et les objectifs plus larges |
| − | * Les renseignements personnels devraient, dans la mesure du possible, être recueillis directement auprès de personnes, mais ils peuvent provenir d’autres sources lorsque la Loi sur la protection des renseignements personnels le permet | + | <b>Outils :</b> |
| − | * Les renseignements personnels doivent être disponibles pour faciliter le droit d’accès et de correction des documents gouvernementaux des Canadiens | + | * Flux de valeur (élément de valeur et proposition de valeur - Contexte de ce que nous mesurons) |
| − | * Concevoir des contrôles d’accès dans tous les processus et dans toutes les couches architecturales dès les premières étapes de la conception pour limiter l’utilisation et la divulgation des renseignements personnels; | + | * KPI lié aux bénéfices et aux objectifs |
| − | * Concevoir des processus permettant que les renseignements personnels demeurent exacts, à jour et aussi complets que possible, et qu’ils puissent être corrigés au besoin | + | |
| − | * Il faut envisager des techniques de désidentification avant de partager des renseignements personnels | + | ==== * Réutiliser les actifs de données existants lorsque cela est permis et acquérir de nouvelles données seulement si cela est nécessaire ==== |
| − | * En collaboration avec le bureau de l’AIPRP approprié de l’établissement, déterminer si une évaluation des facteurs relatifs à la vie privée (ÉFVP) est requise pour déterminer et atténuer les risques pour la vie privée des programmes nouveaux ou considérablement modifiés ayant une incidence sur la vie privée des personnes | + | |
| − | * Établir des procédures pour identifier et traiter les atteintes à la vie privée pour qu’elles puissent être signalées rapidement et qu’il y soit répondu efficacement au bureau de l’AIPRP approprié de l’établissement | + | <b>Comment y parvenir :</b> |
| − | + | * Résumer la réutilisabilité des actifs de données de l'architecture étant donné : | |
| + | * Contexte des actifs de données et des besoins des utilisateurs et des parties prenantes | ||
| + | * Qualité des données et adéquation à l'usage | ||
| + | * Cadre réglementaire de confidentialité et de sécurité | ||
| + | <b>Outils :</b> | ||
| + | * Législatif / Réglementaire | ||
| + | |||
| + | ==== * Veiller à ce que les données recueillies, y compris celles provenant de sources tierces, soient de grande qualité ==== | ||
| + | |||
| + | <b>Comment y parvenir :</b> | ||
| + | * Résumer comment l'architecture répond aux exigences de qualité des données des sources tierces : | ||
| + | * La qualité des données répond à l'objectif | ||
| + | * Dimensions de la qualité des données, notamment : | ||
| + | * Pertinence, | ||
| + | * Ponctualité | ||
| + | * Cohérence, | ||
| + | * Fiabilité, | ||
| + | * Interprétabilité, | ||
| + | * Convivialité | ||
| + | * Mécanisme de qualité des données | ||
| + | <b>Outils :</b> | ||
| + | * Fondation de données - Mettre en œuvre (tirer parti de la définition standard) | ||
| + | * Catalogue de données | ||
| + | * Bénéfices Centre de connaissances | ||
| + | * Data Lake (croissance) | ||
| + | * Science des données et plateforme machine | ||
| + | |||
| + | === Gérer et réutiliser les données de manière stratégique et responsable === | ||
| + | |||
| + | ==== * Définir et établir clairement les rôles, les responsabilités et la responsabilisation en matière de gestion des données ==== | ||
| + | |||
| + | <b>Comment y parvenir :</b> | ||
| + | * Résumer comment l'architecture aide à définir les rôles clés de gestion des données et leurs responsabilités pour garantir que les données sont correctes, cohérentes et complètes, notamment : | ||
| + | * Identifie les responsabilités du gestionnaire de données ; | ||
| + | * Identifie les responsabilités du consommateur de données, et ; | ||
| + | * Identifie les responsabilités du dépositaire des données. | ||
| + | <b>Outils :</b> | ||
| + | * Les parties prenantes | ||
| + | * Modèle de processus d'affaires | ||
| + | * Exigences fonctionnelles | ||
| + | * Glossaire d'entreprise | ||
| + | |||
| + | ==== * Identifier et documenter la lignée des actifs de données ==== | ||
| + | |||
| + | <b>Comment y parvenir :</b> | ||
| + | * Résumer comment les actifs de données de l'architecture démontrent l'alignement avec la gouvernance et la stratégie des données du département, notamment : | ||
| + | * Alignement sur la base de données de la pratique d'architecture de l'information/des données d'EDSC | ||
| + | * Alignement sur le fondement théorique de la pratique de l'architecture de l'information/des données d'EDSC | ||
| + | <b>Outils :</b> | ||
| + | * État cible (éléments de données de la solution) | ||
| + | * Fondation de données - Mettre en œuvre (tirer parti de la définition standard) | ||
| + | * Catalogue de données | ||
| + | * Bénéfices Centre de connaissances | ||
| + | * Data Lake (croissance) | ||
| + | * Science des données et plateforme machine | ||
| + | * Fondement théorique | ||
| + | * EDRM (Conceptuel et Logique) | ||
| + | * Glossaire d'entreprise | ||
| + | * Stratégie de données ministérielle | ||
| + | |||
| + | ==== * Définir les calendriers de conservation et d’élimination conformément à la valeur opérationnelle ainsi qu’aux politiques et aux lois applicables en matière de protection des renseignements personnels et de sécurité ==== | ||
| + | |||
| + | <b>Comment y parvenir :</b> | ||
| + | * Résumez pour chaque actif de données clés : | ||
| + | * Calendriers de conservation et de disposition | ||
| + | * Processus de disposition | ||
| + | <b>Outils :</b> | ||
| + | * État cible (éléments de données de la solution) | ||
| + | * Prérogatives non fonctionnelles | ||
| + | * Meilleures pratiques et normes de GI | ||
| + | |||
| + | ==== * Veiller à ce que les données soient gérées pour permettre, dans la mesure du possible, leurs interopérabilité, réutilisation et partage au sein des ministères et avec d’autres ministères à l’échelle du gouvernement afin d’éviter les répétitions et maximiser l’utilité, tout en respectant les exigences en matière de sécurité et de protection des renseignements personnels ==== | ||
| + | |||
| + | <b>Comment y parvenir :</b> | ||
| + | * Résumer comment l'architecture permet l'interopérabilité, la réutilisation et le partage dans toute la mesure du possible au sein et entre les départements | ||
| + | * Résumer comment l'architecture évite la duplication des données | ||
| + | <b>Outils :</b> | ||
| + | * État cible | ||
| + | * Fondation de données - Mettre en œuvre (tirer parti de la définition standard) | ||
| + | * Catalogue de données | ||
| + | * Bénéfices Centre de connaissances | ||
| + | * Data Lake (croissance) | ||
| + | |||
| + | ==== * Contribuer à la taxonomie et aux structures de classification des données d’entreprise et internationales afin de gérer, de stocker, de chercher et de récupérer des données ==== | ||
| + | |||
| + | <b>Comment y parvenir :</b> | ||
| + | * Résumer l'alignement sur le département/GC : | ||
| + | * Structure de la taxonomie des données | ||
| + | * Structure de classification des données | ||
| + | <b>Outils :</b> | ||
| + | * Fondation de données - Mettre en œuvre (tirer parti de la définition standard) | ||
| + | * Catalogue de données | ||
| + | * Fondement théorique | ||
| + | * EDRM (Conceptuel et Logique) | ||
| + | * Glossaire d'entreprise | ||
| + | |||
| + | === Utiliser et partager ouvertement les données de manière éthique et sécuritaire === | ||
| + | |||
| + | ==== * Partager les données de façon ouverte par défaut conformément à la Directive sur le gouvernement ouvert et les normes numériques, tout en respectant les exigences en matière de sécurité et de protection des renseignements personnels. Les données partagées doivent respecter les normes organisationnelles et internationales existantes, notamment en matière de qualité et d’éthique des données ==== | ||
| + | |||
| + | <b>Comment y parvenir :</b> | ||
| + | * Résumez comment l'architecture prend en charge le partage de données ouvertement par défaut conformément à la directive sur le gouvernement ouvert et les normes numériques : | ||
| + | * Normes et politiques de données ministérielles et GC existantes | ||
| + | * Normes internationales de données ; et la Loi sur la protection des renseignements personnels, | ||
| + | * Aptitude à l'usage | ||
| + | * Ethique | ||
| + | <b>Outils :</b> | ||
| + | * Fondation de données - Mettre en œuvre (tirer parti de la définition standard) | ||
| + | * Catalogue de données | ||
| + | * Centre de connaissances sur les avantages | ||
| + | * Data Lake (croissance) | ||
| + | * Science des données et plateforme machine | ||
| + | * Fondement théorique | ||
| + | * EDRM (Conceptuel et Logique) | ||
| + | * Glossaire d'entreprise | ||
| + | * Stratégie de données ministérielle | ||
| + | |||
| + | ==== * Veiller à ce que le formatage des données soit conforme aux normes institutionnelles et internationales en matière d’interopérabilité. Quand aucune norme n’existe, élaborer des normes de données ouvertes avec des experts clés en la matière ==== | ||
| + | |||
| + | <b>Comment y parvenir :</b> | ||
| + | * Résumer comment l'architecture utilise les normes de données d'entreprise et internationales existantes | ||
| + | * Résumez comment l'architecture a développé des normes de données grâce à une collaboration ouverte avec des experts clés en la matière et la communauté de pratique des données d'entreprise. | ||
| + | <b>Outils :</b> | ||
| + | * Normes de données | ||
| + | * NIEM | ||
| + | * Données ouvertes | ||
| + | * Registre national des adresses | ||
| + | * Référentiel de données de référence | ||
| + | |||
| + | ==== * S’assurer que les données combinées ne comportent pas de risque d’identification ou de réidentification de renseignements sensibles ou personnels ==== | ||
| + | |||
| + | <b>Comment y parvenir :</b> | ||
| + | * Résumer comment l'architecture garantit que l'agrégation et le peignage des données ne présentent pas de risque pour la sensibilité des informations ou les informations personnelles | ||
| + | |||
| + | === Concevoir en tenant compte de la protection des renseignements personnels lors de la collecte, de l’utilisation et de la gestion des renseignements personnels === | ||
| + | |||
| + | ==== * Assurer l’harmonisation avec les directives du Bureau de l’accès à l’information et de la protection des renseignements personnels (AIPRP) approprié de l’établissement en ce qui concerne l’interprétation et l’application de la Loi sur la protection des renseignements personnels et des instruments de politique connexes ==== | ||
| + | |||
| + | <b>Comment y parvenir :</b> | ||
| + | * Décrire comment l'architecture s'aligne sur les directives du Bureau de l'AIPRP concernant le cadre réglementaire des renseignements personnels; cadre politique; et directives de consentement | ||
| + | |||
| + | ==== * Évaluer les initiatives pour déterminer si les renseignements personnels seront recueillis, utilisés, communiqués, conservés, partagés et éliminés ==== | ||
| + | |||
| + | <b>Comment y parvenir :</b> | ||
| + | * L'initiative a-t-elle évalué si les renseignements personnels seront recueillis, utilisés, divulgués, conservés, partagés et éliminés | ||
| + | |||
| + | ==== * Recueillir des renseignements personnels seulement s’ils ont un lien direct avec le fonctionnement des programmes ou des activités ==== | ||
| + | |||
| + | <b>Comment y parvenir :</b> | ||
| + | * Résumer comment l'architecture garantit que les informations personnelles collectées sont directement nécessaires au fonctionnement des programmes ou des activités | ||
| + | |||
| + | ==== * Informer les personnes des fins de la collecte au point de collecte en incluant un avis de confidentialité ==== | ||
| + | |||
| + | <b>Comment y parvenir :</b> | ||
| + | * L'avis de confidentialité de la solution fournit-il le but de la collecte de ces informations personnelles | ||
| + | * La solution fournit-elle un avis de confidentialité au moment de la collecte des informations personnelles | ||
| + | |||
| + | ==== * Les renseignements personnels devraient, dans la mesure du possible, être recueillis directement auprès de personnes, mais ils peuvent provenir d’autres sources lorsque la Loi sur la protection des renseignements personnels le permet ==== | ||
| + | |||
| + | <b>Comment y parvenir :</b> | ||
| + | * L'architecture collecte-t-elle des informations personnelles directement auprès de l'individu | ||
| + | * Si non, quels renseignements personnels sont recueillis auprès d'autres sources et sont-ils conformes à la Loi sur la protection des renseignements personnels et à la directive de consentement de la source | ||
| + | <b>Outils :</b> | ||
| + | * Architecture d'état cible | ||
| + | * Architecture d'État intérimaire | ||
| + | |||
| + | ==== * Les renseignements personnels doivent être disponibles pour faciliter le droit d’accès et de correction des documents gouvernementaux des Canadiens ==== | ||
| + | |||
| + | <b>Comment y parvenir :</b> | ||
| + | * Résumer comment l'architecture facilite le droit des Canadiens d'accéder à leurs dossiers de renseignements personnels | ||
| + | * Résumer comment l'architecture facilite le droit des Canadiens de corriger leurs dossiers de renseignements personnels | ||
| + | <b>Outils :</b> | ||
| + | * Architecture d'état cible | ||
| + | * Architecture d'État intérimaire | ||
| + | |||
| + | ==== * Concevoir des contrôles d’accès dans tous les processus et dans toutes les couches architecturales dès les premières étapes de la conception pour limiter l’utilisation et la divulgation des renseignements personnels ==== | ||
| + | |||
| + | <b>Comment y parvenir :</b> | ||
| + | * Résumer comment l'architecture limite l'utilisation et la divulgation des renseignements personnels conformément à la législation sur la protection de la vie privée ; cadres politiques et directives de consentement | ||
| + | |||
| + | ==== * Concevoir des processus permettant que les renseignements personnels demeurent exacts, à jour et aussi complets que possible, et qu’ils puissent être corrigés au besoin ==== | ||
| + | |||
| + | <b>Comment y parvenir :</b> | ||
| + | * Résumer comment l'architecture garantit que les informations personnelles restent exactes | ||
| + | * Résumer comment l'architecture garantit que les informations personnelles restent à jour | ||
| + | * Résumer comment l'architecture garantit que les informations personnelles restent aussi complètes que possible | ||
| + | * Résumer comment l'architecture garantit que les informations personnelles peuvent être corrigées si nécessaire | ||
| + | <b>Outils :</b> | ||
| + | * Prérogatives non fonctionnelles | ||
| + | * Exigences fonctionnelles | ||
| + | |||
| + | ==== * Il faut envisager des techniques de désidentification avant de partager des renseignements personnels ==== | ||
| + | |||
| + | <b>Comment y parvenir :</b> | ||
| + | * Décrire les techniques de désidentification utilisées par l'architecture pour partager des informations personnelles | ||
| + | |||
| + | ==== * En collaboration avec le bureau de l’AIPRP approprié de l’établissement, déterminer si une évaluation des facteurs relatifs à la vie privée (ÉFVP) est requise pour déterminer et atténuer les risques pour la vie privée des programmes nouveaux ou considérablement modifiés ayant une incidence sur la vie privée des personnes ==== | ||
| + | |||
| + | <b>Comment y parvenir :</b> | ||
| + | * Décrire comment l'architecture répond aux recommandations du PIA | ||
| + | * Si toutes les recommandations de l'ÉFVP ne sont pas prises en compte, expliquez comment l'entreprise fera face aux risques résiduels de l'ÉFVP | ||
| + | |||
| + | ==== * Établir des procédures pour identifier et traiter les atteintes à la vie privée pour qu’elles puissent être signalées rapidement et qu’il y soit répondu efficacement au bureau de l’AIPRP approprié de l’établissement ==== | ||
| + | |||
| + | <b>Comment y parvenir :</b> | ||
| + | * Des procédures sont-elles établies pour identifier et traiter les atteintes à la vie privée | ||
| + | * Résumer comment l'architecture permet/supporte ces procédures | ||
| + | <b>Outils :</b> | ||
| + | * Modèle de processus d'affaires | ||
</multilang> | </multilang> | ||
Latest revision as of 16:59, 22 February 2023
Information architecture[edit | edit source]
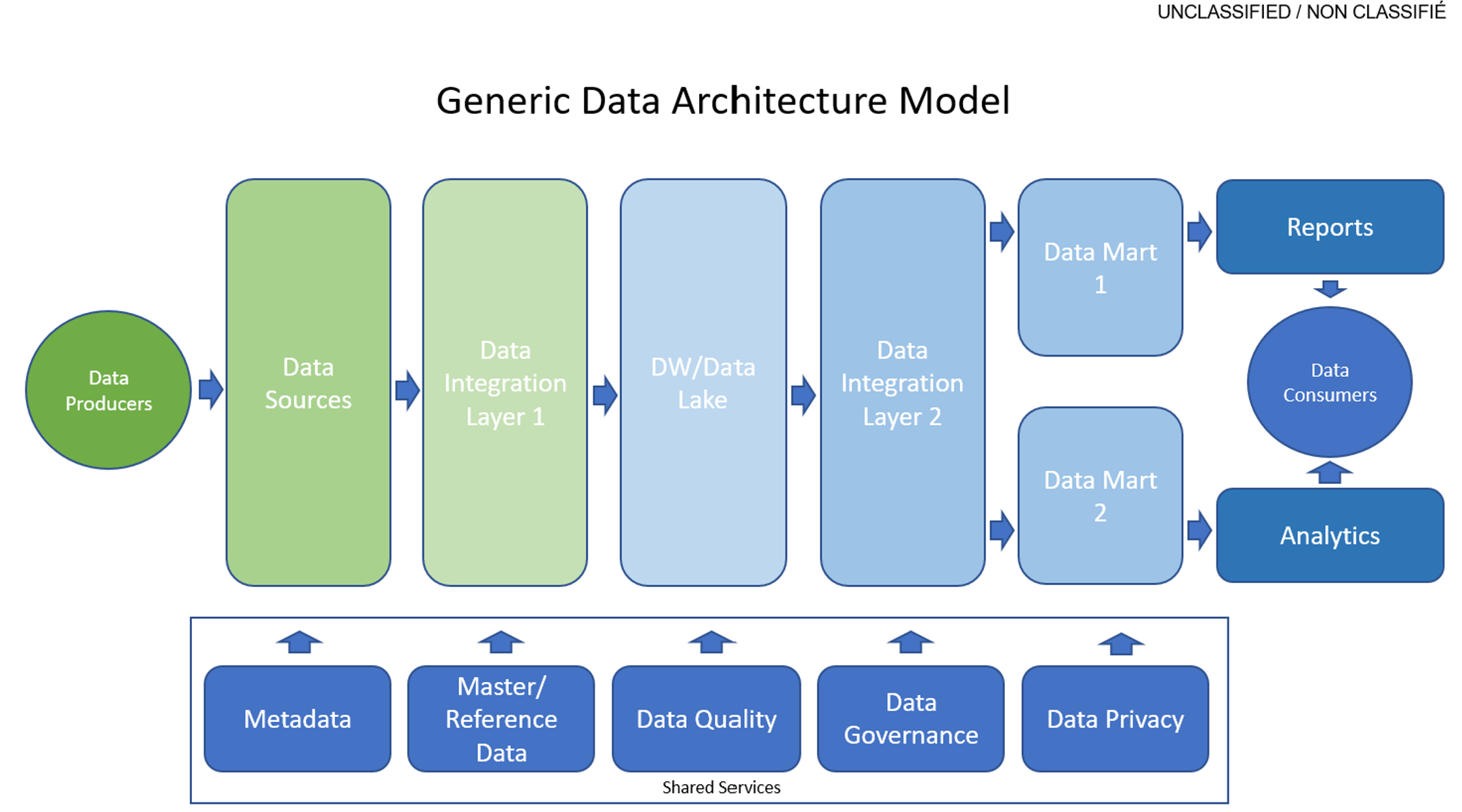
Information architecture is defined as the management and organization of data for a business. The best practices and principles aim to support the needs of a business service and business capability orientation. To facilitate effective sharing of data and information across government, information architectures should be designed to reflect a consistent approach to both structured and unstructured data, such as the adoption of federal and international standards. Information architecture should also reflect responsible data management, information management and governance practices, including the source, quality, interoperability, and associated legal and policy obligations related to the data assets. Information architectures should also distinguish between personal and non‑personal data. How personal information is treated such as its collection, use, sharing (disclosure), and management must respect the requirements of the Privacy Act and its related policies. Under this paragraph is a model of Data Architecture demonstrating the core components that data flows through in an enterprise to obtain insights and analytics.
Data Product: A service or device that collects, processes, and stores data for a business. Data producers also monitor the data obtains to ensure the quality of the data asset.
Data Source: A data source is made up of fields and groups. In the same way that folders on your hard disk contain and organize your files, fields contain the data that users enter into forms that are based on your form template, and groups contain and organize those fields.
Data Integration: Data integration is the process for combining data from several disparate sources to provide users with a single, unified view.
Integration is the act of bringing together smaller components into a single system so that it's able to function as one. And in an IT context, it's stitching together different data subsystems to build a more extensive, more comprehensive, and more standardized system between multiple teams, helping to build unified insights for all.
Data Lake: A data lake is a centralized repository that ingests and stores large volumes of data in its original form. The data can then be processed and used as a basis for a variety of analytic needs. Due to its open, scalable architecture, a data lake can accommodate all types of data from any source, from structured (database tables, Excel sheets) to semi-structured (XML files, webpages) to unstructured (images, audio files, tweets), all without sacrificing fidelity. The data files are typically stored in staged zones—raw, cleansed, and curated—so that different types of users may use the data in its various forms to meet their needs. Data lakes provide core data consistency across a variety of applications, powering big data analytics, machine learning, predictive analytics, and other forms of intelligent action.
Data Mart: A data warehouse is a system that aggregates data from multiple sources into a single, central, consistent data store to support data mining, artificial intelligence (AI), and machine learning—which, ultimately, can enhance sophisticated analytics and business intelligence. Through this strategic collection process, data warehouse solutions consolidate data from the different sources to make it available in one unified form.
A data mart (as noted above) is a focused version of a data warehouse that contains a smaller subset of data important to and needed by a single team or a select group of users within an organization. A data mart is built from an existing data warehouse (or other data sources) through a complex procedure that involves multiple technologies and tools to design and construct a physical database, populate it with data, and set up intricate access and management protocols.
Data Consumers: Data consumers are services or applications, such as Power BI or Dynamics 365 Customer Insights, that read data in Common Data Model folders in Data Lake Storage Gen2. Other data consumers include Azure data-platform services (such as Azure Machine Learning, Azure Data Factory, and Azure Databricks) and turnkey software as a service (SaaS) applications (such as Dynamics 365 Sales Insights). A data consumer might have access to many Common Data Model folders to read content throughout the data lake. If a data consumer wants to write back data or insights that it has derived from a data producer, the data consumer should follow the pattern described for data producers above and write within its own file system.
Outlined in the points below, are objectives to be fulfilled in order to maintain information architecture standards.
Collect data to address the needs of the users and other stakeholders[edit | edit source]
Collecting data is an important activity to define a scope that meets all stakeholder requirements. Stakeholder requirements refer to what is expected out of an activity such as business capabilities being addressed, resource requirements, and timeline. Assessing these requirements will make it easier to draw boundaries around the activity and ensure that a high-quality result is being delivered. To track and demonstrate that requirements are being fulfilled throughout the activity, data must be collected first. Data collection is a systematic process of gathering observations for the purposes of addressing programs or policies in a business or the government.
The initial step to collecting data is to identify what information needs to be gathered and the source of data. For example, in creating a centralized system for a patient database at a hospital, once the user requirements are identified, the process of how data is collected should be considered. There are several ways of collecting data, such as interviews, surveys/ questionnaires, workshops, and observing consumers. The goal is to gather these requirements and prioritize them. Questions for surveys or interviews must be consistent to keep the data organized and easier to prioritize. The data itself should be reusable and easily transportable to another system to save time and money.
- assess program objectives based on data requirements, as well as users, business and stakeholder needs
How to achieve:
* Summarize how the architecture meets the data needs of the users and other key stakeholders including:
* How does the data asset contribute to outcomes/needs of the user and other stakeholders
* Gaps in the existing data assets to meet the needs of the users and other stakeholders and how the architecture addresses these gaps
* Gaps in data collection and analysis and how the architecture is addressing it so that department can ensure that we are serving the members of our society
* Alignment to the data foundation of the departmental information/data architecture practice
* Alignment to the theoretical foundation of the departmental information/data architecture practice
Tools:
* For Data Foundation – Implement:
* Data Catalogue
* Benefits Knowledge hub
* Data Lake (growth)
* Data Science and Machine Platform
* Stakeholder Requirements
* Solution Requirements
- collect only the minimum set of data needed to support a policy, program, or service
How to achieve:
* Summarize how the architecture aligns to “collect with a purpose” including:
* What is necessary (as opposed to what is sufficient) to meet the stakeholder need
* Supporting Performance Information Profiles (PIPs) used to assess a progress towards target and broader objectives
Tools:
* Value Stream (Value Item and Value Proposition – Context on what we measure)
* KPI (Linked to benefits, outcomes and objectives)
- reuse existing data assets where permissible and only acquire new data if required
How to achieve:
* Summarize reusability of the architecture’s data assets given:
* Context of data assets and user and stakeholder needs
* Data quality and fit for purpose
* Privacy and Security Regulatory Framework
Tools:
* Legislative / Regulations
- ensure data collected, including from third-party sources, are of high quality
How to achieve:
* Summarize how the architecture meets the data quality requirements of third-party sources:
* Data quality meets fit for purpose
* Data quality dimensions including:
* Relevance,
* Timeliness
* Consistency,
* Reliability,
* Interpretability,
* Usability
* Data quality mechanism
Tools:
* Data Foundation – Implement (Leverage the standard definition)
* Data Catalogue
* Benefits Knowledge hub
* Data Lake (growth)
* Data Science and Machine Platform
Manage and reuse data strategically and responsibly[edit | edit source]
Data architecture is defined as the management of data by translating the business requirements into technical requirements for an organization. The management of data refers to the collection, storage, and usage of data in an information system. Furthermore, data management and the direction of its flow are guided by various framework of models, policies, rules, and standards used by the organization. They both provide a foundation to work efficiently with data as well as to govern data access by establishing roles, responsibilities and accountabilities. For example, an organization may have a system that they have conceptualized to store information. To ensure that the system succeeds in doing so, it must satisfy adequate data storage capabilities as well as role-based access functionalities. To assess said capabilities, an organization should review the system’s functions and compare them to the user/stakeholder requirements to ensure adequate support to organizational policies. The system must also ensure data lineage is maintained to be able to trace back data to its origin.
Data architectures define and set data standards and principles. To accomplish the process of translating business requirements into technical requirements, some duties may entail creating blueprints for data flow and data management as well as assessing potential data sources. Plans may be devised to make these sources accessible to all employees and keep them protected according to existing security and privacy policies. Data architecture identifies [data] consumers within an organization, then align with their varying requirements and allow them access at any moment with a synchronous process to deliver usable data. For example, within a hospital, nurses and doctors utilize and work with patient data. Depending on who it is, some may be required to update data such as illness or prescribed medicine, and some should view and direct based on the data, to coordinate rooms and available medical machines. It is a necessity to have a centralized system, or systems that are interoperable, with varying features and permissions to be able to access all this information at any given time. Otherwise, if non-interoperable multiple systems for different data sets were used, it would be difficult to maintain the flow of data throughout the hospital, which would cause loss opportunities of time-sensitive action that can harm patients in critical conditions.
- define and establish clear roles, responsibilities, and accountabilities for data management
How to achieve:
* Summarize how the architecture assists in defining key data management roles and their responsibilities to ensure data is correct, consistent, and complete including:
* Identifies the data steward responsibilities;
* Identifies the data consumer responsibilities, and;
* Identifies the data custodian responsibilities.
Tools:
* Stakeholders
* Business Process Model
* Functional Requirements
* Business Glossary
- identify and document the lineage of data assets
How to achieve:
* Summarize how the architecture’s data assets demonstrate alignment with department's data governance and strategy including:
* Alignment to the data foundation of the ESDC information/data architecture practice
* Alignment to the theoretical foundation of the ESDC information/data architecture practice
Tools:
* Target state (solution data elements)
* Data Foundation – Implement (Leverage the standard definition)
* Data Catalogue
* Benefits Knowledge hub
* Data Lake (growth)
* Data Science and Machine Platform
* Theoretical Foundation
* EDRM (Conceptual and Logical)
* Business Glossary
* Departmental Data Strategy
- define retention and disposition schedules in accordance with business value as well as applicable privacy and security policy and legislation
How to achieve:
* Summarize for each key data assets:
* Retention and disposition schedules
* Disposition process
Tools:
* Target state (solution data elements)
* Non Functional Requirements
* IM Best Practices and Standards
- ensure data are managed to enable interoperability, reuse and sharing to the greatest extent possible within and across departments in government to avoid duplication and maximize utility, while respecting security and privacy requirements
How to achieve:
* Summarize how the architecture enables interoperability, reuse and sharing to the greatest extent possible within and across departments
* Summarize how the architecture avoids data duplication
Tools:
* Target State
* Data Foundation – Implement (Leverage the standard definition)
* Data Catalogue
* Benefits Knowledge hub
* Data Lake (growth)
- contribute to and align with enterprise and international data taxonomy and classification structures to manage, store, search and retrieve data
How to achieve:
* Summarize the alignment to departmental/GC:
* Data taxonomy structure
* Data classification structure
Tools:
* Data Foundation – Implement (Leverage the standard definition)
* Data Catalogue
* Theoretical Foundation
* EDRM (Conceptual and Logical)
* Business Glossary
[edit | edit source]
Organizations should be able to adhere to ethical guidelines on data sharing to address and meet emerging standards and legislative requirements. It is an organization’s responsibility to apply transparency and to respect how data is used within the organization. Using and sharing data in an ethical manner can build trust between the public and the organization. Failing to prioritize privacy, security, consent, and ownership of data can negatively harm an organization’s reputation and credibility (and create the risk of extinction). To share data ethically and legally, an organization must request participants’ consent. How personal data will be used and shared must be communicated transparently to avoid misleading anyone. Furthermore, to keep data private and more generic for future sharing purposes, it can be anonymized by removing participant’s tombstone information such as name, address, and occupation. If data anonymization is considered, it is ideal to plan it during the collection phase. It is necessary to inform third party readers when data has been anonymized. This may be done by using markings in the text for contents that have been previously removed. Additionally, an original data repository copy should always be kept separately and secured to keep a record of all data that has been anonymized in the final product. Third party readers should have valid reasons and the right qualifications to access the original data to ensure data is treated in a careful manner. Data must not be shared when: there is a conflict of interest with the need to protect personal identities; when an organization does not have ownership of the data; and when releasing the data presents a security risk.
- share data openly by default as per the Directive on Open Government and Digital Standards, while respecting security and privacy requirements; data shared should adhere to existing enterprise and international standards, including on data quality and ethics
How to achieve:
* Summarize how the architecture supports sharing data openly by default as per Directive on Open Government and Digital Standards given:
* Existing departmental and GC data standards and policies
* International data standards; and the Privacy Act,
* Fitness for purpose
* Ethics
Tools:
* Data Foundation – Implement (Leverage the standard definition)
* Data Catalogue
* Benefits Knowledge Hub
* Data Lake (growth)
* Data Science and Machine Platform
* Theoretical Foundation
* EDRM (Conceptual and Logical)
* Business Glossary
* Departmental Data Strategy
- ensure data formatting aligns to existing enterprise and international standards on interoperability; where none exist, develop data standards in the open with key subject matter experts
How to achieve:
* Summarize how the architecture utilises existing enterprise and international data standards
* Summarize how the architecture has developed any data standards through open collaboration with key subject matter experts and the Enterprise Data Community of Practice.
Tools:
* Data Standards
* NIEM
* OpenData
* National Address Register
* Reference Data Repository
- ensure that combined data does not risk identification or re‑identification of sensitive or personal information
How to achieve: * Summarize how the architecture ensures the aggregation and combing of data does not pose a risk to information sensitivity or personal information
Design with privacy in mind for the collection, use and management of personal Information[edit | edit source]
Keeping data protected in a company is important to keep sensitive information such as industry knowledge and personal information private and solely on a company server. It is a legal requirement for companies as outlined in the Privacy Act. Furthermore, when companies work with clients who are investing their money and time, it is expected for them to ensure that data will be held safely at the minimum. Data privacy can protect the reputation and credibility of a company as unprotected data can often fall victim to hackers and outside sources. For example, within a hospital, patient personal information should be kept secure and away from the public. This is expected of hospitals and failing to comply can result in legal and ethical issues. Additionally, it would be dangerous for strangers to get access to patient information such as their address and health implications.
- ensure alignment with guidance from appropriate institutional ATIP Office with respect to interpretation and application of the Privacy Act and related policy instruments
How to achieve: * Describe how the architecture aligns to guidance of the ATIP Office around personal information regulatory framework; policy framework; and consent directives
- assess initiatives to determine if personal information will be collected, used, disclosed, retained, shared, and disposed
How to achieve: * Has the initiative assessed if personal information will be collected, used, disclosed, retained, shared, and disposed
- only collect personal information if it directly relates to the operation of the programs or activities
How to achieve: * Summarize how the architecture ensures the personal information collected is directly required to the operational of the programs or activities
- notify individuals of the purpose for collection at the point of collection by including a privacy notice
How to achieve: * Does the solution’s privacy notice provide the purpose for collecting this personal information * Does the solution provide a privacy notice at the point of personal information collection
- personal information should be, wherever possible, collected directly from individuals but can be from other sources where permitted by the Privacy Act
How to achieve: * Does the architecture collect personal information directly from the individual * If no, what personal information is collect form other sources and does it comply with the Privacy Act and the consent directive of the source Tools: * Target State Architecture * Interim State Architecture
- personal information must be available to facilitate Canadians’ right of access to and correction of government records
How to achieve: * Summarize how the architecture facilitates Canadian's right to access their personal information records * Summarize how the architecture facilitates Canadian's right to correct their personal information records Tools: * Target State Architecture * Interim State Architecture
- design access controls into all processes and across all architectural layers from the earliest stages of design to limit the use and disclosure of personal information
How to achieve: * Summarize how the architecture limits the use and disclosure of personal information in accordance to the privacy legislative; policy frameworks and consent directives
- design processes so personal information remains accurate, up‑to‑date and as complete as possible, and can be corrected if required
How to achieve: * Summarize how the architecture ensures personal information remains accurate * Summarize how the architecture ensures personal information remains up-to-date * Summarize how the architecture ensures personal information remains complete as possible * Summarize how the architecture ensures personal information can be corrected if required Tools: * Non Functional Requirements * FUnctional Requirements
- de‑identification techniques should be considered prior to sharing personal information
How to achieve: * Outline the de-identification techniques used by the architecture in sharing personal information
- in collaboration with appropriate institutional ATIP Office, determine if a Privacy Impact Assessment (PIA) is required to identify and mitigate privacy risks for new or substantially modified programs that impact the privacy of individuals
How to achieve: * Describe how the architecture addresses the recommendations of the PIA * If not all recommendations of the PIA are being addressed, outline how the business will address any residual risks of the PIA
- establish procedures to identify and address privacy breaches so they can be reported quickly and responded to efficiently to appropriate institutional ATIP Office
How to achieve: * Are procedures established to identify and address privacy breaches * Summarize how the architecture enables/supports these procedures Tools: * Business Process Model