Government of Canada Enterprise Security Architecture (ESA) Program
Welcome
Welcome to the Government of Canada (GC) Enterprise Security Architecture (ESA) Program Portal. This portal is designed to help Government of Canada employees familiarize themselves with the GC ESA program by providing detailed, but concise information about the program, its key stakeholders, guiding principles, scope, and much more. It also includes a page with tools and templates to be used by security practitioners and a page with reference materials that provide details about different aspects of the GC ESA program for those interested in learning more about it. At the top of the screen you will find the navigation bar. You can use this bar to easily navigate between pages within the GC ESA Portal and learn more about the GC ESA program. The rest of this page provides a basic overview of the GC ESA program.
If you have any questions, suggestions or constructive criticism regarding the GC ESA program portal or its content, please feel free to contact us by clicking on the button in the top right corner, labelled "Contact Us". Also, please join our group on GCconnex by clicking on the other button in the top right corner, labelled "Join us on: GCconnex". By doing so, you will receive all of the latest news regarding the GC ESA Program and other related IT security activities, and you will be the first to know about any new tools or resources we create.
Overview of the GC ESA Program
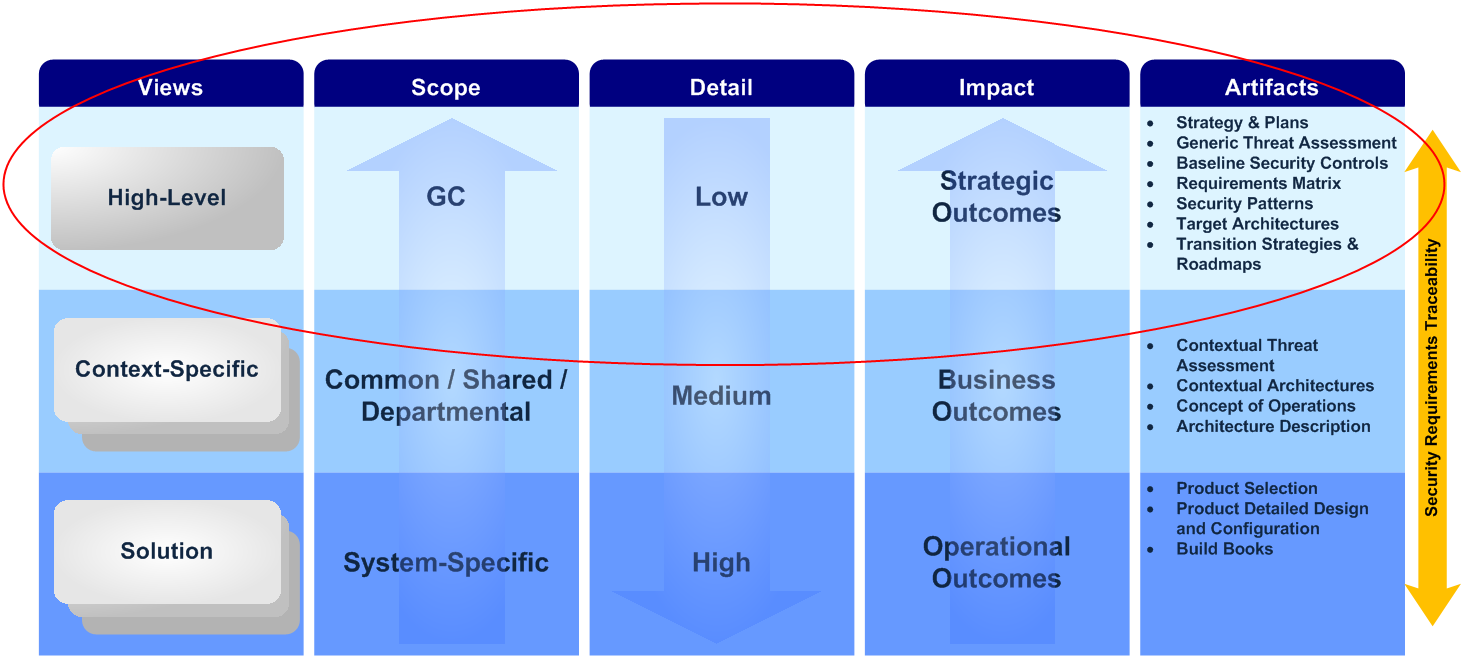
The GC ESA program is a government-wide initiative to provide a standardized approach to developing IT security architecture, ensuring that basic security blocks are implemented across the enterprise as the infrastructure is being renewed. The image on the right shows how the GC ESA program supports the direction the GC is taking with regards to GC IT security.
The GC ESA program aims to:
- Ensure more cost-effective, interoperable, resilient and secure IT solutions in support of GC enterprise objectives;
- Maintain availability of GC systems and services while complying with relevant GC legislation and policy instruments;
- Adopt an architecture methodology and approach to ensure common understanding, alignment, and reduce duplication of effort amongst interdepartmental stakeholders;
- Ensure security of information, IT infrastructure and applications with the implementation of consistent security controls which reduces total cost of ownership; and
- Keep risk at acceptable levels.
The GC ESA program will serve as a guide to departments and agencies in planning, implementing, and operating their information systems by offering the necessary framework, tools, and templates to design, evaluate, and build an IT security architecture tailored to their organization, in accordance with Communications Security Establishment’s (CSE) ITSG-33 – IT Security Risk Management: A Lifecycle Approach and other security industry best practices in the area of architecture, risk management and compliance.
For more information about the GC ESA Program, please read the GC ESA Program Charteror its synopsis.
Scope of GC ESA Program
As the image on the left shows, the scope of the GC ESA program is high-level, with a focus on enterprise as a whole, but it can also assist with security activities at all layers, in accordance with the GC ESA Program Charter.
The GC may develop IT security architectures that can be categorized into three groups based on level of detail:
High-level view: Artifacts developed at this layer are high-level with GC Enterprise in scope and have a strategic impact. Examples include an Enterprise Security Concept of Operations or a GC Baseline Threat Assessment.
Context-specific view: Artifacts developed at this layer provide supplementary details, are common, shared or departmental in scope and have a tactical impact. Examples include a specific focus area Security Requirements Traceability Matrix, or a context-specific architecture (e.g. Business Control Profile for a Human Resources System).
Solution view: Artifacts developed at this layer are very detailed, system-specific in scope and have an operational impact. Examples include a detailed design documentation or a Standard Operating Procedure for a Data Loss Prevention System.
For more information about the scope of the ESA program, please read the GC ESA Program Charteror its synopsis.
GC ESA Areas of Focus
Enhancing the security posture of GC systems and networks requires a comprehensive IT security strategy that includes defining requirements, developing IT security architectures, and designing patterns that can be used to implement defence-in-depth IT security capabilities. The GC established the ESA program for to address these areas.
Over the next several years, the ESA program will focus on the following eight focus areas:
- Identity, Credential and Access Management (ICA)
- Endpoint Security (END)
- Data Security (DAT)
- Application Security (APP)
- Network and Communications Security (NCS)
- Security Operations (OPS)
- Compute and Storage Services Security (CSS)
For more information about the ESA program areas of focus, please read the GC ESA Vision and Strategy document.
Benefits and Risks of the GC ESA Program
Implementation of the GC IT security strategy, including the GC ESA program, will result in many benefits, including:
- Enhanced security posture throughout the GC;
- Better awareness of threats to GC IT infrastructure;
- Improved understanding of the motivations and techniques of adversaries;
- Increased abilities to provide rapid response to IT security incidents affecting GC systems;
- Better positioned to acquire and share cyber threat information from/with trusted partners; and
- Enhanced level of confidence with users, citizens, allies and other levels of government.
However, while the benefits are substantial, the GC IT security strategy is not without any risks, including:
- Culture shift,
- Costs,
- Achieving balanced results,
- Long-term commitment,
- Technology advancements,
- Technology limitations, and
- Insufficient resources.
For a more detailed explanation of the benefits and risks of the GC IT security strategy and ESA program, please read the GC ESA Program Vision and Strategy document.