Difference between revisions of "GC Service & Digital Target Enterprise Architecture"
| Line 194: | Line 194: | ||
{| class="wikitable" | {| class="wikitable" | ||
|'''Design services digitally from end‑to‑end to meet the Government of Canada users and other stakeholders’ needs''' | |'''Design services digitally from end‑to‑end to meet the Government of Canada users and other stakeholders’ needs''' | ||
| − | | | + | | |
| − | + | * clearly identify internal and external users and other stakeholders and their needs for each policy, program and business service | |
| − | + | * include policy requirement applying to specific users and other stakeholder groups, such as accessibility, gender-based plus analysis, and official languages in the creation of the service | |
| − | + | * perform Algorithmic Impact Assessment (AIA) to support risk mitigation activities when deploying an automated decision system as per ''Directive on Automated Decision-Making'' | |
| − | + | * model end‑to‑end business service delivery to provide quality, maximize effectiveness and optimize efficiencies across all channels (for example, lean process) | |
| − | |||
| − | |||
|- | |- | ||
|'''Architect to be outcome‑driven and strategically aligned to the department and to the Government of Canada''' | |'''Architect to be outcome‑driven and strategically aligned to the department and to the Government of Canada''' | ||
| − | | | + | | |
| − | + | * identify which departmental/GC business services, outcomes and strategies will be addressed | |
| − | + | * establish metrics for identified business outcomes throughout the life cycle of an investment | |
| − | + | * translate business outcomes and strategy into business capability implications in the GC Business Capability Model to establish a common vocabulary between business, development, and operation | |
| − | |||
|- | |- | ||
|'''Promote horizontal enablement of the enterprise''' | |'''Promote horizontal enablement of the enterprise''' | ||
| − | | | + | | |
| − | + | * identify opportunities to enable business services horizontally across the GC enterprise and to provide cohesive experience to users and other stakeholders | |
| − | + | * reuse common business capabilities, processes and enterprise solutions from across government and private sector | |
| − | + | * publish in the open all reusable common business capabilities, processes and enterprise solutions for others to develop and leverage cohesive horizontal enterprise services | |
| − | |||
|} | |} | ||
| Line 221: | Line 217: | ||
{| class="wikitable" | {| class="wikitable" | ||
|'''Collect data to address the needs of the users and other stakeholders''' | |'''Collect data to address the needs of the users and other stakeholders''' | ||
| − | | | + | | |
| − | + | * assess data requirements‑based program objectives, as well users, business and stakeholder needs | |
| − | + | * collect only the minimum set of data needed to support a policy, program, or service | |
| − | + | * reuse existing data assets where permissible and only acquire new data if required | |
| − | + | * ensure data collected, including from third-party sources, are of high quality | |
| − | |||
| − | |||
|- | |- | ||
|'''Manage and reuse data strategically and responsibly''' | |'''Manage and reuse data strategically and responsibly''' | ||
| − | | | + | | |
| + | * define and establish clear roles, responsibilities, and accountabilities for data management | ||
| − | + | * identify and document the lineage of data assets | |
| − | + | * define retention and disposition schedules in accordance with business value as well as applicable privacy and security policy and legislation | |
| − | + | * ensure data are managed to enable interoperability, reuse and sharing to the greatest extent possible within and across departments in government to avoid duplication and maximize utility, while respecting security and privacy requirements | |
| − | + | * contribute to and align with enterprise and international data taxonomy and classification structures to manage, store, search and retrieve data | |
| − | |||
| − | |||
| − | |||
|- | |- | ||
|'''Use and share data openly in an ethical and secure manner''' | |'''Use and share data openly in an ethical and secure manner''' | ||
| − | | | + | | |
| − | + | * share data openly by default as per the ''Directive on Open Government and Digital Standards'', while respecting security and privacy requirements; data shared should adhere to existing enterprise and international standards, including on data quality and ethics | |
| − | + | * ensure data formatting aligns to existing enterprise and international standards on interoperability; where none exist, develop data standards in the open with key subject matter experts | |
| − | + | * ensure that combined data does not risk identification or re‑identification of sensitive or personal information | |
| − | |||
|- | |- | ||
|'''Design with privacy in mind for the collection, use and management of personal Information''' | |'''Design with privacy in mind for the collection, use and management of personal Information''' | ||
| − | | | + | | |
| − | + | * ensure alignment with guidance from appropriate institutional ATIP Office with respect to interpretation and application of the ''Privacy Act'' and related policy instruments | |
| − | + | * assess initiatives to determine if personal information will be collected, used, disclosed, retained, shared, and disposed | |
| − | + | * only collect personal information if it directly relates to the operation of the programs or activities | |
| − | + | * notify individuals of the purpose for collection at the point of collection by including a privacy notice | |
| − | + | * personal information should be, wherever possible, collected directly from individuals but can be from other sources where permitted by the ''Privacy Act'' | |
| − | + | * personal information must be available to facilitate Canadians’ right of access to and correction of government records | |
| − | + | * design access controls into all processes and across all architectural layers from the earliest stages of design to limit the use and disclosure of personal information | |
| − | + | * design processes so personal information remains accurate, up‑to‑date and as complete as possible, and can be corrected if required | |
| − | + | * de‑identification techniques should be considered prior to sharing personal information | |
| − | + | * in collaboration with appropriate institutional ATIP Office, determine if a Privacy Impact Assessment (PIA) is required to identify and mitigate privacy risks for new or substantially modified programs that impact the privacy of individuals | |
| − | + | * establish procedures to identify and address privacy breaches so they can be reported quickly and responded to efficiently to appropriate institutional ATIP Office | |
| − | |||
| − | |||
| − | |||
| − | |||
| − | |||
| − | |||
| − | |||
| − | |||
| − | |||
|} | |} | ||
| Line 274: | Line 256: | ||
Application architecture practices must evolve significantly for the successful implementation of the GC Enterprise Ecosystem Target Architecture. Transitioning from legacy systems based on monolithic architectures to architectures that oriented around business services and based on re‑useable components implementing business capabilities, is a major shift. Interoperability becomes a key element, and the number of stakeholders that must be considered increases. | Application architecture practices must evolve significantly for the successful implementation of the GC Enterprise Ecosystem Target Architecture. Transitioning from legacy systems based on monolithic architectures to architectures that oriented around business services and based on re‑useable components implementing business capabilities, is a major shift. Interoperability becomes a key element, and the number of stakeholders that must be considered increases. | ||
{| class="wikitable" | {| class="wikitable" | ||
| − | |'''Use open source solutions hosted in public cloud''' | + | |'''Use open source solutions''' |
| − | | | + | '''hosted in public cloud''' |
| − | + | | | |
| − | + | * select existing solutions that can be reused over custom built | |
| − | + | * contribute all improvements back to the communities | |
| − | + | * register open source software to the Open Resource Exchange | |
|- | |- | ||
| − | |'''Use software as a service (SaaS) hosted in public cloud''' | + | |'''Use software as a service (SaaS)''' |
| − | | | + | '''hosted in public cloud''' |
| − | + | | | |
| − | + | * choose SaaS that best fit for purpose based on alignment with SaaS capabilities | |
| − | + | * choose a SaaS solution that is extendable | |
| − | + | * configure SaaS and if customization is necessary extend as open source modules | |
|- | |- | ||
|'''Design for Interoperability''' | |'''Design for Interoperability''' | ||
| − | | | + | | |
| − | + | * design systems as highly modular and loosely coupled services | |
| − | + | * expose services, including existing ones, through APIs | |
| − | + | * make the APIs discoverable to the appropriate stakeholders | |
| − | |||
|} | |} | ||
| Line 300: | Line 281: | ||
{| class="wikitable" | {| class="wikitable" | ||
|'''Use cloud first''' | |'''Use cloud first''' | ||
| − | | | + | | |
| − | + | * adopt the use of the GC Accelerators to ensure proper security and access controls | |
| − | + | * enforce this order of preference: software as a service (SaaS) first, then platform as a service (PaaS), and lastly infrastructure as a service (IaaS) | |
| − | + | * fulfill cloud services through SSC Cloud‑Brokering Services | |
| − | + | * enforce this order of preference: public cloud first, then hybrid cloud, then private cloud, and lastly non‑cloud (on‑premises) solutions | |
| − | + | * design for cloud mobility and develop an exit strategy to avoid vendor lock‑in | |
| − | |||
| − | |||
| − | |||
|- | |- | ||
|'''Design for performance, availability and scalability''' | |'''Design for performance, availability and scalability''' | ||
| − | | | + | | |
| − | + | * ensure response times meet user needs, and critical services are highly available | |
| − | + | * support zero‑downtime deployments for planned and unplanned maintenance | |
| − | + | * use distributed architectures, assume failure will happen, handle errors gracefully, and monitor performance and behaviour actively | |
| − | + | * establish architectures that supports new technology insertion with minimal disruption to existing programs and services | |
| − | + | * control technical diversity; design systems based on modern technologies and platforms already in use | |
| − | |||
| − | |||
| − | |||
|- | |- | ||
|'''Follow DevSecOps principles''' | |'''Follow DevSecOps principles''' | ||
| − | | | + | | |
| − | + | * use continuous integration and continuous deployments | |
| − | + | * ensure automated testing occurs for security and functionality | |
| − | + | * include your users and other stakeholders as part of the DevSecOps process, which refers to the concept of making software security a core part of the overall software delivery process | |
| − | |||
|} | |} | ||
Revision as of 14:30, 22 December 2020
GC Service and Digital Target Enterprise Architecture Whitepaper
Version: 1.33
November 4, 2020
Office of the Chief Information Officer of Canada
Treasury Board of Canada Secretariat
Government of Canada
The Service and Digital Target Enterprise Architecture whitepaper will be published on the Digital Government page of Canada.ca
Executive summary
The Service and Digital Target Enterprise Architecture is an enabler for the Policy on Service and Digital.
The Service and Digital Target Enterprise Architecture defines a model for the digital enablement of GC services that address many of the critical challenges with the current GC enterprise ecosystem. It seeks to reduce the silos within the current GC ecosystem by having departments adopt a user‑ and service‑delivery‑centric perspective when considering new IT solutions or modernizing older solutions. It advocates a whole‑of‑government approach where IT is aligned with business services and where solutions are based on reusable components implementing business capabilities optimized to reduce unnecessary redundancy. This reuse is enabled using published application programming interfaces (APIs) shared across government. This approach allows the government to focus on improving its service delivery to Canadians while addressing its challenges with legacy systems.
The Policy on Service and Digital and the Service and Digital Target Enterprise Architecture are guided by a commitment to the guiding principles and best practices of the Government of Canada Digital Standards:
- design with users
- iterate and improve frequently
- work in the open by default
- use open standards and solutions
- address security and privacy risks
- build in accessibility from the start
- empower staff to deliver better services
- be good data stewards
- design ethical services
- collaborate widely
Purpose of this paper
This paper is intended to assist federal institutions by providing recommendations on how systems could be implemented over the next several years to provide Canadian citizens with a more cohesive and sustainable digital landscape when interacting with the Government of Canada.
The intended audience is those involved in the delivery of digital services within the Government of Canada including deputy heads and chief information officers. The white paper will also inform suppliers of the enterprise architecture direction, assisting them to align their services when interacting with the government. Finally, the white paper will inform the Canadian public and the international community of the Government of Canada’s enterprise architecture direction for digital transition.
Unless otherwise specified, any example mentioned in this white paper does not represent any existing plans of the Government of Canada.
This white paper is not meant to replace existing documents that address the government’s strategic direction on digital services.
(Digital) vision
“The Government of Canada is an open and service‑oriented organization that operates and delivers programs and services to people and businesses in simple, modern and effective ways that are optimized for digital and available anytime, anywhere and from any device.
Digitally, the Government of Canada must operate as one to benefit all Canadians.”
Policy on Service and Digital
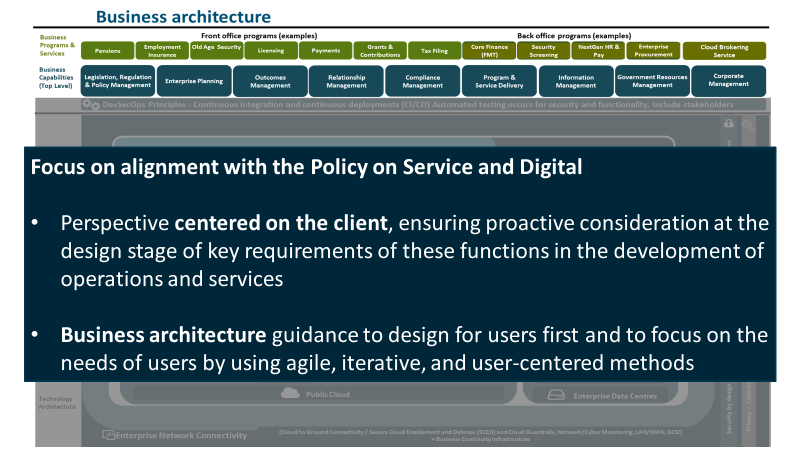
The Policy on Service and Digital and supporting instruments serve as an integrated set of rules that articulate how Government of Canada organizations manage service delivery, information and data, information technology, and cybersecurity in the digital era. Other requirements, including but not limited to, requirements for privacy, official languages and accessibility, also apply to the management of service delivery, information and data, information management and cybersecurity. Those policies, set out in Section 8, must be applied in conjunction with the Policy on Service and Digital. The Policy on Service and Digital focuses on the client, ensuring proactive consideration at the design stage of key requirements of these functions in the development of operations and services. It establishes an enterprise‑wide, integrated approach to governance, planning and management. Overall, the Policy on Service and Digital advances the delivery of services and the effectiveness of government operations through the strategic management of government information and data and leveraging of information technology.
Section 4.1.2.3 of the Policy on Service and Digital. The Chief Information Officer (CIO) of Canada is responsible for: Prescribing expectations with regard to enterprise architecture.
Section 4.1.2.4 of the Policy on Service and Digital. The Chief Information Officer (CIO) of Canada is responsible for: Establishing and chairing an enterprise architecture review board that is mandated to define current and target architecture standards for the Government of Canada and review departmental proposals for alignment.
Section 4.1.1.1 of the Directive on Service and Digital. The departmental Chief Information Officer (CIO) is responsible for: Chairing a departmental architecture review board that is mandated to review and approve the architecture of all departmental digital initiatives and ensure their alignment with enterprise architectures.
What problems does the Service and Digital Target Enterprise Architecture address?
Canadians rely on the federal government for programs and services, which in turn depend on reliable, authoritative data and enabling information technology capabilities to ensure successful delivery. The GC enterprise ecosystem consists of all the information technology used by the Government of Canada and all related environmental factors. The interdependence of all elements with the ecosystem is an essential aspect of what makes it an ecosystem. When discussing information technology within the GC enterprise, one must consider the ecosystem.
What is the issue?
The Government of Canada has reached a critical point in its management of the IT systems that are used to enable the delivery of government services. There is an increasing gap between the expectations of Canadian citizens and the ability of the government’s legacy systems to meet those expectations. The total accumulated technical debt associated with legacy systems has reached a tipping point where a simple system‑by‑system replacement approach for individual systems has increasingly become cost and risk prohibitive. The business processes in place to manage the life cycles of these IT systems have become barriers rather than enablers.
How did we get here?
| Changing expectations | The rapid evolution of the internet as the ubiquitous platform for service delivery has outstripped the government’s ability to address the demand. Citizens have an increased expectation that all government services will be reliably delivered 24 hours a day, 7 days a week with no artificial differentiation based on which department provides the service. The introduction of new disruptive technologies outside of government can quickly shift the citizen’s expectations as they become aware of new approaches or capabilities. |
| Separate mandates | Government information systems have long mirrored the legislative separation of the functional mandates of departments. In part, this is because the original approaches to a delegation of authority and accountability in legislation did not contemplate the cross‑cutting dependency on information technology that exists today. Beyond authority and accountability, there are legislative constraints on intragovernmental information sharing has historically impeded the integration of business processes across government. Budget and funding models have further reinforced this separation. As a result, there have been limited opportunities to reduce overhead and eliminate redundancies across systems and across government. |
| Evolution of technology | Initially, business process automation within government was implemented as standalone solutions, in many cases monolithic and mainframe solutions. As time passed, the life cycle evolution of individual systems tended to limit their scope to those individual systems; reinforced by a desire to restrict procurement, technical, and change complexity and risk. Current technologies that could be used to implement cohesive enterprise approaches were introduced relatively recently, many years after most government systems were implemented. This gap has been exacerbated over time by the significant difference between the ability of the private sector and the public sector to adopt and leverage new technologies. |
Why is the problem so intractable? Why isn’t “business as usual” a workable way forward?
| “Business as usual” not effective | The “business‑as‑usual” approach would be to try to address each legacy system in isolation; in other words, a simplistic system‑by‑system replacement. The costs and risks associated with this approach for major legacy systems are prohibitive in most cases. Dealing with each system in isolation results in missed opportunities for reuse and for eliminating redundancies. In addition, these “big bang” methods dramatically increase business service delivery risk. By the time a significant replacement project is completed, there is also a substantial possibility that the underlying technology is out of date. To mitigate these issues, approaches that allow for an incremental and managed transition over time are suggested. |
| An alternative strategy | One alternative strategy is to incrementally migrate legacy systems by gradually replacing functional elements with new applications and services; in other words, an “evolve‑and‑transcend” strategy. This strategy implements an architectural pattern named the “Strangler Fig,” a metaphor for refactoring rather than replacing legacy systems, by incrementally replacing functional parts of a legacy application slowly and systematically over time, thus spreading costs and mitigating risks. |
Service and Digital Target Enterprise Architecture
The Service and Digital Target Enterprise Architecture defines a model for the digital enablement of Government of Canada services that address many of the critical challenges with the current GC enterprise ecosystem. It seeks to reduce the silos within the current GC ecosystem by having departments adopt a user‑ and service‑delivery‑centric perspective when considering new IT solutions or modernizing older solutions. It advocates a whole‑of‑government approach where IT is aligned to business services and solutions are based on reusable components implementing business capabilities optimized to reduce unnecessary redundancy. This reuse is enabled using published APIs shared across government. This approach allows the government to focus on improving its service delivery to Canadians while addressing the challenges with legacy systems.
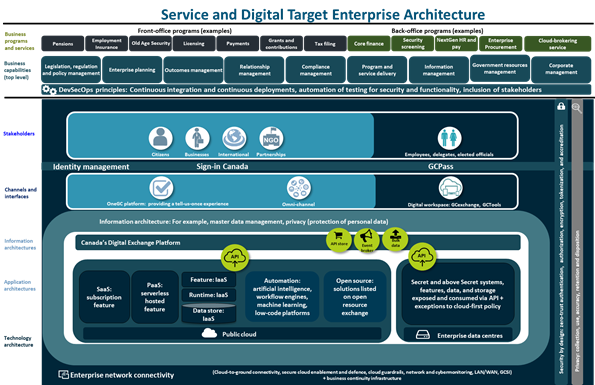
The goal of the Service and Digital Target State Enterprise Architecture is to depict the Government of Canada’s future state vision in one picture. The diagram is divided into several parts, which are based on The Open Architecture Framework (TOGAF) framework explained in a subsequent section. This framework views business, information and data, applications, technology and security each as separate layers, having their own concerns and architecture.
The top layer of the diagram represents business architecture. The programs in this layer are categorized as front office, which provides services directly to citizens, academic institutions, and Canadian businesses, and back‑office services which support the government itself. Examples of front office programs include Employment Insurance and tax filing services, and examples of back‑end programs include finance security screening, pay, enterprise procurement, and business continuity.
In the following layer, key aspects of the top level of the GC Business Capability Model are depicted. This takes into consideration the IT plan investment framework and provides a mechanism to identify potentially redundant investments across, opportunities for rationalization, and identification of opportunities for enterprise solutions.
Add image File:Business Architecture.png
.
.
.
.
.
.
.
.
In the following layer, stakeholders represent the actors that interact with GC services, either externally (such as citizens, businesses, those which the GC is in partnership with such as universities or international actors), or internally, such as GC employees, delegates, or elected officials. They have different access (use of mobile, voice‑activated smart speakers, contact centres, and kiosks) and accessibility requirements, and may communicate in either official language. Sign‑in Canada will provide a cohesive identity management solution for citizens and other external stakeholders to enable authentication and authorization across all GC departments.
The goal is to respond to external users, who as clients, want interactions across governments to be managed with consistency, integrity, and trust so that they have a beneficial, personalized, and seamless experience.
To ensure consistency, every channel will be supported through the same architecture. Examples of these channels include mobile, voice‑activated smart speaker, call centre, or in‑person kiosk. This concept is called omni‑channel.
The next layer projects the idea of a service‑oriented government, with a user‑centred approach to the business of government that puts citizens and their needs as the primary focus of our work, using “tell‑us‑once” service approaches, integrated services across the GC program and service landscape in a way that provides real‑time information to Canadians about their service applications. It is a perspective centred on users and service delivery when considering new IT solutions or modernizing older solutions. It builds on business architecture guidance to design for users first, focusing on the needs of users, using agile, iterative, and user‑centred methods in a whole-of-government context.
ADD image File:External_Stakeholders.png
Leveraging the concept of harmonization described for external users through Sign‑in Canada, GCPass will enable authentication and authorization to GC Systems for Internal stakeholders. The digital workplace will uniformly enable the work of public servants, building on a standard design.
ADD image Internal Stakeholders
Information architecture is depicted in the following layer. Information architecture best practices and principles aim to support the needs of a business service and business capability orientation. To facilitate effective sharing of data and information across government, information architectures should be designed to reflect a consistent approach to data, such as the adoption of federal and international standards. Information architecture should also reflect responsible data management, information management and governance practices, including the source, quality, interoperability, and associated legal and policy obligations related to the data assets.
Information architectures should also distinguish between personal and non‑personal data and information as the collection, use, sharing (disclosure), and management of personal information must respect the requirements of the Privacy Act and its related policies.
ADD image Information architecture
The following layer depicts how services will interoperate through a standard fabric, supported by a set of common API standards specifying protocols and payloads. These services will be published in the API Store to facilitate reuse. APIs will be brokered through an API gateway to manage traffic, ensure version control, and monitor how services are exposed and consumed, either directly, or through a common event broker. Procurement of software as a service (SaaS) offerings will be facilitated through Shared Services Canada’s (SSC’s) Cloud Brokering Service and supported through their managed services. These are services that are available to steward infrastructure that are offered by SSC include database management services, cabling, facility management, transition planning and support, system integration services, and project management, among others. GC business programs and services and their enabling capabilities are built on resources within the application and information landscapes.
ADD image application architecture and technology architecture
Also highlighted in this layer are automation capabilities such as artificial intelligence and open source solutions listed on an open resource exchange.
ADD image application architecture and technology architecture
In the bottom‑most view of the Service and Digital Target Enterprise Architecture, the focus is on the technology infrastructure that acts as the glue to bring everything together: the network. The GC network consists of local area network (LAN), wide area network (WAN), satellite, and internet infrastructure that provides general connectivity for internal government users, as well as secure and networks that support collaboration between the government and scientific communities. These are all connected with network hubs that optimize the performance of the GC network. The core infrastructure includes SSC services that ensure IT continuity (disaster recovery), including performance monitoring and reliability planning.
Add Image Enterprise Network connectivity
Security is reflected in the Service and Digital Target Enterprise Architecture diagram as a cross‑cutting factor that spans all horizontal layers. The goal is to ensure security at all architectural levels, from design to implementation to operations; and to ensure authentication, authorization, auditing, monitoring, tokenization, and encryption of all data, whether at rest or in motion.
ADD image security architecture
Improved outcomes
| Improved digital services that meet citizens’ expectations | Canadian citizens expect reliable digital services that deliver a cohesive user experience.
Their expectation for cohesive user experience is founded on their perception that digital services are being delivered by “one” government and not a collection of departments. By aligning digital service delivery to a common set of services defined within a GC Service Inventory and implemented using reusable components based on a common taxonomy of business capabilities, GC can improve the user experience. Their expectations for reliability and availability are based on their experiences with modern private‑sector internet services. By transitioning to public cloud offerings and infrastructure, GC can leverage private sector investments to meet citizens’ expectations for reliability and availability. |
| Managed costs and improved agility | GC needs to achieve economies of scale realized by modernizing and standardizing IT and by reducing its reliance on costly and outdated technology.
By encouraging the sharing of reusable components based on business capabilities and by leveraging private sector cloud solutions and open source software, GC can both reduce redundancy and help manage costs. By transitioning to an architecture that leverages public cloud offerings and infrastructure, GC can become more agile in responding to changes in business needs, thus delivering future‑ready IT systems that can support the GC digital transformation journey. |
| Engaged and effective workforce | Retention has been identified as a significant IT workforce and talent management issue. The ability to attract and retain new talent is challenging due to the perception that government IT is decades out‑of‑date. Besides the drain on workforce capacity, attrition has negatively impacted morale, the level of engagement and overall workforce effectiveness.
By adopting modern technology and practices, the government is in a better position to attract and retain new talent. Reducing attrition and boosting recent talent acquisition will have a positive impact on morale and foster an engaged and effective workforce. |
Realization practices and principles
To realize the GC Enterprise Ecosystem Target Architecture, departments should align with the practices and principles as outlined below, when considering new IT solutions or modernizing older solutions. The architectural approach was developed to facilitate managed incremental transitions but requires more strategic planning on the part of departments to be implemented effectively.
The Government of Canada Enterprise Architecture Framework defined below presents the evaluation criteria being used by GC Enterprise Architecture Review Board to align solutions to the Service and Digital Target Enterprise Architecture. In the interest of effective communication to the architecture community of practice, the material has been organized based on the architectural domains business, information, application, technology, and security.
Enterprise architecture framework
The enterprise architecture framework is the criteria used by the Government of Canada enterprise architecture review board and departmental architecture review boards when reviewing digital initiatives to ensure their alignment with enterprise architectures across business, information, application, technology and security domains to support strategic outcomes.
Business architecture
Business architecture is a critical aspect for the successful implementation of the GC Enterprise Ecosystem Target Architecture. The architectural strategy advocates whole‑of‑government approach where IT is aligned to business services and solutions are based on re‑useable components implementing business capabilities in order to deliver a cohesive user experience. As such, it is essential that business services, stakeholder needs, opportunities to improve cohesion and opportunities for reuse across government be clearly understood. In the past these elements have not been a priority. It is expected that the IT culture and practices will have to change to make business architecture, in general, and these elements a primary focus.
| Design services digitally from end‑to‑end to meet the Government of Canada users and other stakeholders’ needs |
|
| Architect to be outcome‑driven and strategically aligned to the department and to the Government of Canada |
|
| Promote horizontal enablement of the enterprise |
|
Information architecture
Information architecture includes both structured and unstructured data. The best practices and principles aim to support the needs of a business service and business capability orientation. To facilitate effective sharing of data and information across government, information architectures should be designed to reflect a consistent approach to data, such as the adoption of federal and international standards. Information architecture should also reflect responsible data management, information management and governance practices, including the source, quality, interoperability, and associated legal and policy obligations related to the data assets. Information architectures should also distinguish between personal and non‑personal data and information as the collection, use, sharing (disclosure), and management of personal information must respect the requirements of the Privacy Act and its related policies.
| Collect data to address the needs of the users and other stakeholders |
|
| Manage and reuse data strategically and responsibly |
|
| Use and share data openly in an ethical and secure manner |
|
| Design with privacy in mind for the collection, use and management of personal Information |
|
Application architecture
Application architecture practices must evolve significantly for the successful implementation of the GC Enterprise Ecosystem Target Architecture. Transitioning from legacy systems based on monolithic architectures to architectures that oriented around business services and based on re‑useable components implementing business capabilities, is a major shift. Interoperability becomes a key element, and the number of stakeholders that must be considered increases.
| Use open source solutions
hosted in public cloud |
|
| Use software as a service (SaaS)
hosted in public cloud |
|
| Design for Interoperability |
|
Technology architecture
Technology architecture is an important enabler of highly available and adaptable solutions that must be aligned with the chosen application architecture. Cloud adoption provides many potential advantages by mitigating the logistical constraints that often negatively impacted legacy solutions hosted “on premises.” However, the application architecture must be able to enable these advantages.
| Use cloud first |
|
| Design for performance, availability and scalability |
|
| Follow DevSecOps principles |
|
Security architecture
The GC Enterprise Security Architecture program is a government‑wide initiative to provide a standardized approach to developing IT security architecture, ensuring that basic security blocks are implemented across the enterprise as the infrastructure is being renewed.
| Build security into the system life cycle across all architectural layers |
|
| Ensure secure access to systems and services |
|
| Maintain secure operations |
|