ESA Program Charter
Overview of the GC ESA Program Charter
The GC ESA Program Charter describes the ESA initiative and provides a framework to support the delivery of the program and its objectives. The program charter will guide the execution and control of the GC ESA program. It also documents the program's definition and characteristics, as well as provides an overview of the program governance, roles and responsibilities, and high level plans. Its key points are summarized on this page, but for more detail, please read the GC ESA Program Charter.
Context for the Program Charter
The program charter identifies two documents that provide context for and support the development of the GC ESA Program.
Canada's Cyber Security Strategy
Canada's Cyber Security Strategy (CCSS), which was published in 2018, demonstrates the GC's commitment to protecting Canada's cyberspace. CCSS is national in scope and comprises of three fundamental pillars:
- Securing Government Systems
- Partnering to Secure Vital Cyber Systems Outside the Federal Government
- Helping Canada to be Secure Online
CCSS has identified several areas that need to be addressed in terms of securing government systems, including keeping pace with evolving cyber threats, enhancing the security of the GC cyber architecture, addressing global supply chain issues, and improving cyber security education and awareness. The ESA program is focused on dealing with these Pillar 1 activities.
For more information, please read Canada's Cyber Security Strategy.
Strengthening the Security of Federal Cyber Systems: A Backgrounder
As outlined in the Strengthening the Security of Federal Cyber Systems: A Backgrounder (aka the "GC ESA Backgrounder"), enhancing the security posture of GC systems and networks requires a comprehensive IT security strategy that includes developing IT security architecture designs, implementing defence-in-depth IT security capabilities based on these designs, and detecting and effectively responding to cyber threats. It also means ensuring that GC users understand and adhere to applicable security policies and know-how to identify and respond to cyber threats directed at end users. Finally, enhancing the security posture of GC systems requires that the GC understand how the IT landscape is evolving and that it continues to align its IT security strategy with its overall IT strategy.
The Backgrounder describes three fundamental themes:
- Improve our understanding of the cyber threat landscape
- Strengthen defensive capabilities
- Establish incident recover capabilities
GC ESA Program Scope, Approach, and Deliverables
The GC ESA Program Charter states that overall objective of the ESA program is to ensure that security is built into the designs of the IT infrastructure as it undergoes its transformation. The GC must, on an ongoing basis, identify threats to GC networks and systems, prioritize and counter identified and potential threats, and continually improve the robustness and security of the GC IT infrastructure.
Scope
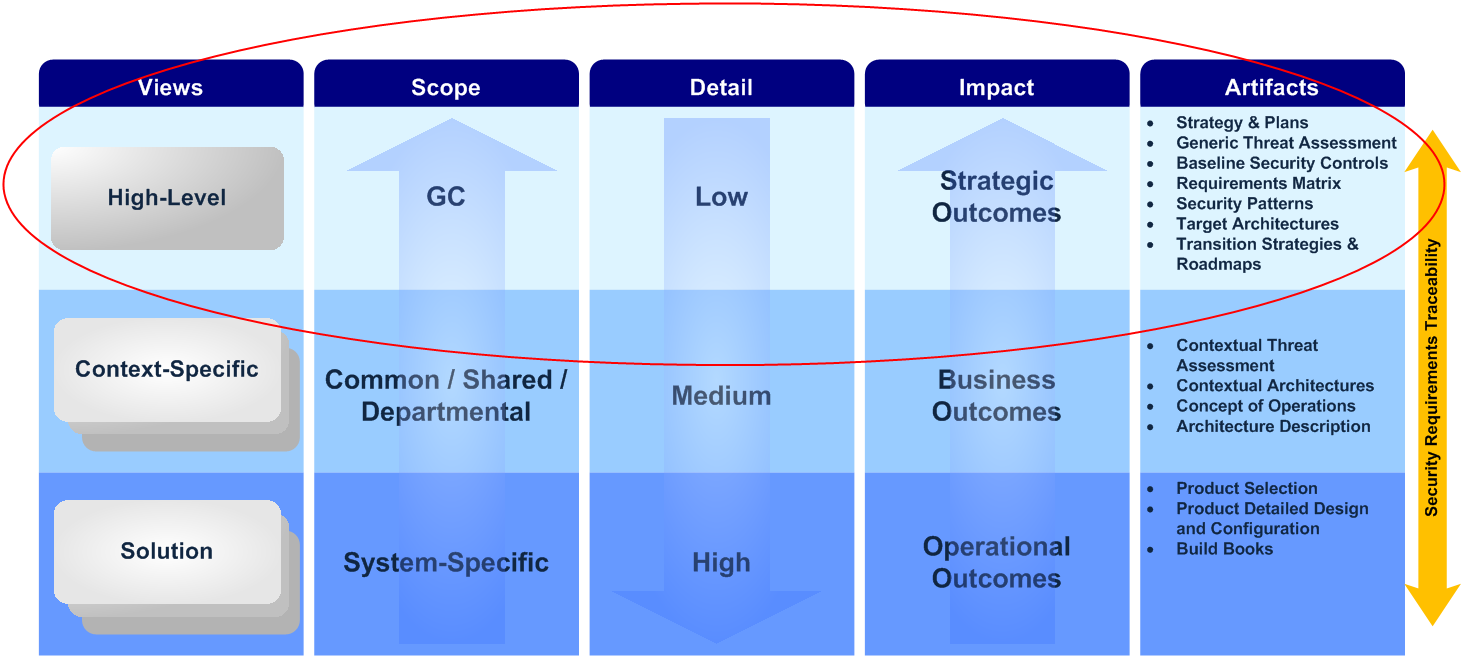
As the image on the left shows, the program charter establishes that the scope of the ESA program is high-level, with a focus on enterprise as a whole, but it can also assist with security activities at all layers.
The GC may develop IT security architectures that can be categorized into three groups based on level of detail:
High-level view: Artifacts developed at this layer are high-level with GC Enterprise in scope and have a strategic impact. Examples include an Enterprise Security Concept of Operations or a GC Baseline Threat Assessment.
Context-specific view: Artifacts developed at this layer provide supplementary details, are common, shared or departmental in scope and have a tactical impact. Examples include a specific focus area Security Requirements Traceability Matrix, or a context-specific architecture (e.g. Business Control Profile for a Human Resources System).
Solution view: Artifacts developed at this layer are very detailed, system-specific in scope and have an operational impact. Examples include detailed design documentation or a Standard Operating Procedure for a Data Loss Prevention System.
For more information about the scope of the GC ESA program, please read the GC ESA Program Charter.
Program Approach
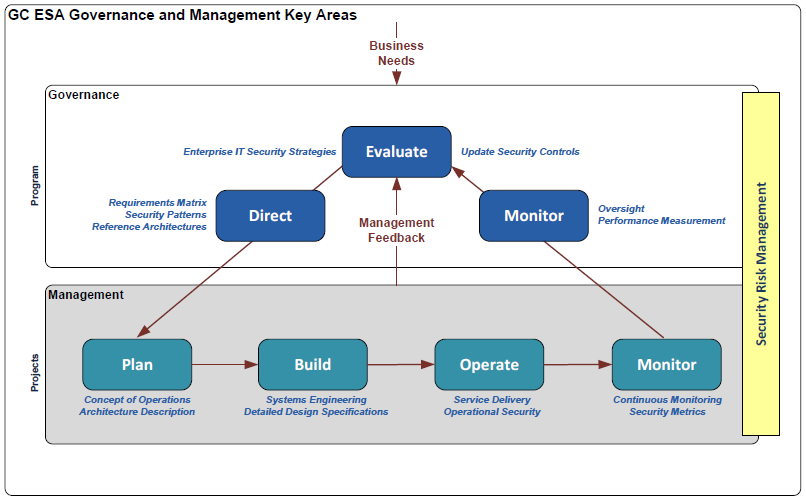
The program charter also provides an overview of the governance, risk, architecture compliance, and monitoring and measurement strategies for the GC ESA program. It notes that the desired results of the GC ESA program can only be achieved through the collaboration of departments and agencies that have a specific role in designing and implementing the GC enterprise IT security architecture, with support from other lead security agencies and key stakeholders.
Governance and Management
The program charter dictates that a clear governance model and management model must be developed. The governance model should set the direction and objectives for the ESA program within the GC, and the management plan should execute the achievement of the objectives. The key areas for the GC ESA Program Governance model are:
- Evaluate
- Direct
- Monitor
The key areas for the ESA Program Management model are:
- Plan
- Build
- Operate
- Monitor
For more information about the governance and management of the GC ESA Program, please read the GC ESA Program Charter.