Important: The GCConnex decommission will not affect GCCollab or GCWiki. Thank you and happy collaborating!
Technology Trends/Data Leak Prevention
|
|||||||
|---|---|---|---|---|---|---|---|
 | |||||||
| Status | Published | ||||||
| Initial release | May 23, 2019 | ||||||
| Latest version | May 23, 2019 | ||||||
| Official publication | Blockchain.pdf | ||||||
| |||||||
Data Leak Prevention (DLP), also known as “data loss prevention,” is a cybersecurity solution that includes a variety of strategies, processes, and tools whose purpose is to protect an organization‘s valuable data from being accessed by unauthorized users, released into an untrusted environment, or destroyed.
Business Brief
DLP provides the tools to mitigate data leak incidents from occurring within an organization. DLP software usually includes the following functionalities:
- Protection: DLP tools implement safeguards such as encryptions, access controls and restrictions to mitigate possible vulnerabilities. An organization can regulate file access by classifying data according to their level of security and by defining a set of rules each user has to abide by.
- Detection: DLP can alert administrators by generating a real-time detailed report on policy violations such as an attacker attempting to access sensitive data. By creating a baseline behavioural profile of standard patterns, the software can detect abnormal or suspicious user activity. Some solutions accomplish this using machine learning.
- Monitoring: DLP monitors the behaviour of users on how the data is being accessed, used and moved through the IT infrastructure in order to detect irregular or dangerous user activity. If an event is triggered by a rule violation, the system will notify the security personnel. The system gains visibility in order to proactively secure data from leaving the organization on policy violations.
Technology Brief
DLP technology is usually categorized into three different components related to each state of the data lifecycle: data at rest, data in motion, and data in use. In most DLP products, there is also a central management server acting as the control center of the DLP deployment. This is usually where DLP policies are managed, data is collected from sensors and endpoint agents, and backup and restore is handled. The components of a data leak prevention tool are, in general:
Storage DLP: “Data at Rest” refers to data stored on a “device,” for example, on a server, database, workstations, laptops, mobile devices, portable storage or removable media. The term refers to data being inactive and not currently being transmitted across a network or being actively processed. A storage DLP protects this type of data by using several security tools:
- Data masking hides sensitive information like personal identifiable data.
- Access controls prevent unauthorized access.
- File encryption adds a layer of protection.
- Data classification uses a DLP agent to tag data according to their level of security. Combined with a set of rules, an organization can regulate user access to use, modify and delete information.
- A database-activity monitoring tool inspects databases, data warehouses (EDW) and mainframes and sends alerts on policy violations. In order to classify data, some mechanism uses conceptual definitions, keywords or regular expression matching.
Network DLP: “Data in Motion” is data that is actively traveling across a network such as email or a file transferred over File Transfer Protocol (FTP) or Secure Socket Shell (SSH). A Network DLP focuses on analyzing network traffic to detect sensitive data transfer in violation of security policies and providing tools to ensure the safety of data transfer. Examples of this include:
- An email monitoring tool can identify if an email contains sensitive information and block the action or encrypt the content.
- The Intrusion Detection System (IDS) monitors for any malicious activity occurring on the network and typically reports to an administrator or to the central management server using a Security Information and Event Management system (SIEM).
- Firewall and antivirus software are commonly available products included in a DLP strategy.
Endpoint DLP: “Data in Use” is the data currently being processed by an application. Data of this nature is in the process of being generated, updated, viewed, and erased on a local machine. Protecting this type of data is a challenging task because of the large number of systems and devices but it is usually done through an Endpoint DLP agent installed on the local machine. Some characteristics are:
- The tool provides strong user authentication, identity management and profile permissions to secure a system.
- It can monitor and flag unauthorized activities that users may intentionally or unintentionally perform, such as print/fax, copy/paste and screen capture.
- Some DLP agents may offer application control to determine which application can access protected data.
- There are advanced solutions that use machine learning and temporal reasoning algorithms to detect abnormal behavior on a local machine.
Industry Usage
Due to the constant risk of possible breaches, such as in the example above, Data Loss Prevention technology is widely adopted amongst the tech industry to protect their data. When it comes to enterprise solutions, Gartner identifies four leading DLP vendors: Digital Guardian, Forcepoint, McAfee, and Symantec. Market worth around DLP is growing: in 2015, its estimated worth was around $0.96 million and is expected to grow to around $2.64 billion by next year at a Compound Annual Growth Rate (CAGR) of 22.3%. While data breaches and cyber-attacks have historically been the driver for demand, the growth of cloud storage will increase demand into the future. Furthermore, as things such as the use of digital services, social media, the Internet of Things (IoT) and e-commerce expand, the production of data, even big data, will grow with it as will the need for storage, whether on cloud or through other means. Thus, the desire and regulatory obligations to protect data, such as through DLP, will expand as well.
The DLP market used to have the same approach with respect to monitoring and protecting an organization’s data, but modern solutions differ significantly and have become more individualised. The traditional approach, sometimes called a project approach or a suite, involves a network gateway acting as a man-in-the-middle to monitor the traffic. It requires that the source, destination and type of sensitive information is known and well-defined. The newer method, sometimes referred to as the data visibility or individual approach, uses an agent installed locally on each system to monitor all user and system activity. This approach works well an organization is still in an age of discovery regarding its transmittal and sharing of data and most networks users would potentially have access to sensitive forms of data. The majority of organizations employ both DLP approaches to varying degrees.
Canadian Government Use
The Government of Canada (GC) has a responsibility to protect not only its data and IT assets but also that of its citizens and the data collected on or about them. Despite this, the GC itself is not free from experiencing data leaks. For example, the Canadian Revenue Agency (CRA) reported 3,763 data breaches in 2013, including incidents where taxpayer’s information were lost, compromised, or accidentally released. In order to prevent such occurrences, as well as those on both smaller and larger scales, there are various DLP protocols in place throughout the GC. Currently, DLP operations are run independently in each department. However, this is in concurrence with federal supporting policies and procedures, some of which also extend to industry.
As of November 1, 2018, private Canadian businesses and industries, along with the health sector, which are subjected to The Personal Information Protection and Electronic Documents Act (PIPEDA), are required to report all data breaches involving personal information that may harm an individual, hold a record of all data breaches, and notify the affected individuals. The goal of this act is to assure citizens have their personal information protected by appropriate safeguards in accordance to their right to access their personal information. Similarly, the federal Privacy Act stipulates how GC departments can share and provide access to personal information on or about individual Canadian citizens and also mandates reporting of security breaches involving this data.
Since the GC relies extensively on IT to provide its services, the Operational Security Standard from Management of Information Technology Security (MITS) as well as the Operational Security Standard – Business Continuity (BCP) Program defines a baseline of security requirements which federal departments and agencies must fulfill to ensure the security of information are under their control. Those prevention safeguards include incorporating identification and authentication in all networks and systems, authorization and access control to restrict accessibility on a “need to know” basis, proper cryptographic and encryption protocols, and emanations security methods such as TEMPEST. In the event of a data breach, the Policy on Government Security (PGS) establishes a mechanism to coordinate the response and recovery. Since the data breaches are primarily caused by people, the Canadian Centre for Cyber Security offers up-to-date publications as part of an awareness campaign.
Implications for Government Agencies
Value Proposition
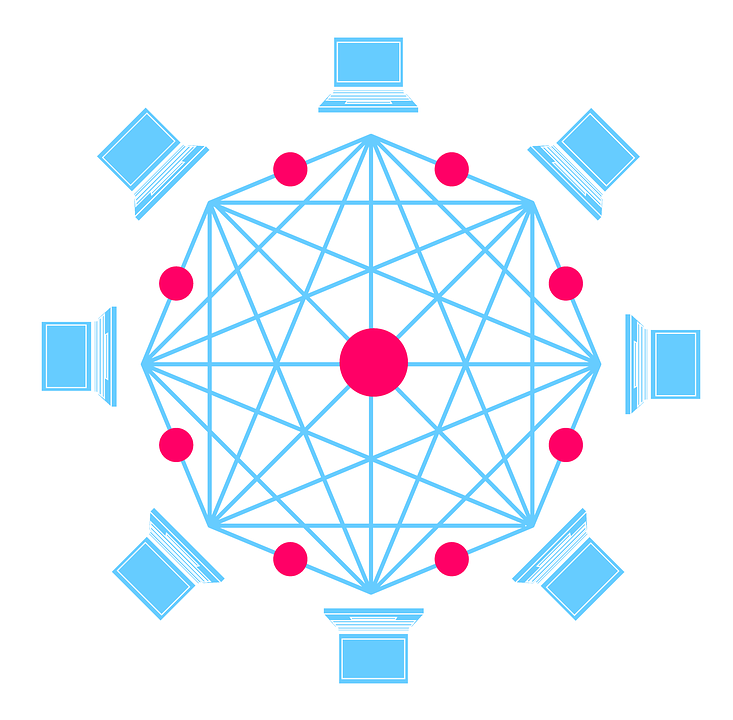
Blockchain offers a numbers of benefits to the Government of Canada, such as a reduction in costs and complexity, trusted record keeping and user-centric privacy control. It offers significant opportunities in terms of a single source for public records, support for multiple contributors and a technology ideal for multi-jurisdictional interactions. Due to its decentralized, collaborative nature, it potentially aligns well with policies and practices around Open Government, which aim to make Government services, data, and digital records more accessible to Canadians.
By eliminating the duplication and reducing the need for intermediaries, blockchain technology could be used by SSC to speed-up aspects of service delivery. A challenge for SSC in terms of blockchain will be to identify which enterprise solutions emerge as leaders and how they deal with privacy, confidentiality, auditability, performance and scalability.
- Elections Canada – practical applications to support Voter List Management, Secure Identity Management, and management of electoral geography.
- Financial Transactions and Reports Analysis Centre of Canada – exploring implications for anti-money laundering and counter-terrorism financing.
- Public Safety Canada – focused on various uses and misuses of virtual currencies, such as extortion or blackmail.
- Natural Resources Canada – use as a public registry for the disclosure of payments under the Extractive Sectors Transparency Measures Act.
- Bank of Canada – exploring a proof of concept model alongside Payments Canada, Canadian commercial banks and the R3 consortium.
- ISED – engagement with Government departments, provincial-territorial-municipal partners, and key industry players.
Challenges
The amount of time and energy required to maintain the blockchain and create new blocks is not small and this is a frequent criticism of the technology. Conventional database entry, such as using SQL, takes only milliseconds, compared to blockchain, which takes several minutes. Due to the length of time required as well as the need for multiple computers to verify the blocks, blockchains consume an enormous amount of energy.
There are also some concerns with respect to privacy. Since blockchain is built on the premise of decentralization and transparency, the data within the chain is technically available for anyone on the network, provided they have the computational power and knowledge to gain access. Instead of being identified on the network by name, users have encryption keys, which is a list of seemingly random numbers and letters.
Considerations
In a traditional transaction, all stakeholders have to keep a record of the transaction and in the case of a discrepancy, it was more difficult / costly to determine the accuracy of a record. As a result, Blockchain may offer significantly higher returns for each investment dollar spent than that of traditional internal investments. However, to doing so, it means collaborating with customers, citizens, suppliers and competitors in new ways.[4]
Further research is needed to understand the potential impacts that blockchain could have on SSC as a service provider as well on the usage amounts the GC would require. SSC should consider the identification of client areas where blockchain may be leveraged. It may be required that client departments self-identify spaces which could benefit from blockchain processes.
Lastly, SSC and the GC should consider the capacity issues in resources, network capabilities, and time required to create and maintain blockchain networks on its own. Blockchain is not a pedestrian technology, it will require dedicated teams that are appropriately resourced and financed in order for the technology to be deployed as any other service. SSC may wish to consider looking for private sector companies that specialize in providing Blockchain as a Service (BaaS), and determine the risk and cost benefits of outsourcing this process altogether.
Hype Cycle
| English | Français |
|---|---|
| Figure 1. Hype Cycle for Blockchain Technologies, 2018 | Figure 1. Rapport Hype Cycle sur les technologies de la chaîne de blocs, 2018 |
| Expectations | Attentes |
| Time | Temps |
| Blockchain Wallet Platform | Plate-forme de portefeuille de la chaîne de blocs |
| Blockchain Interoperability | Interopérabilité de la chaîne de blocs |
| Postquantum Blockchain | Chaîne de blocs post-quantique |
| Smart Contract Oracle | Oracle des contrats intelligents |
| Zero Knowledge Proofs | Preuve à divulgation nulle de connaissance |
| Distributed Storage in Blockchain | Stockage distribué dans la chaîne de blocs |
| Smart Contracts | Contrats intelligents |
| Blockchain for IAM | Chaîne de blocs pour la gestion des identités et de l’accès |
| Blockchain PaaS | Chaîne de blocs à titre de PaaS |
| Blockchain for Data Security | Chaîne de blocs pour la sécurité des données |
| Decentralized Applications | Applications décentralisées |
| Consensus Mechanisms | Mécanismes de consensus |
| Metacoin Platforms | Plates-formes de Metacoin |
| Sidechains/Channels | Chaînes latérales/canaux |
| Multiparty Computing | Calcul multipartite |
| Cryptocurrency Hardware Wallets | Portefeuilles matériels de cryptomonnaie |
| Cryptocurrency Software Wallets | Portefeuilles logiciels de cryptomonnaie |
| Blockchain | Chaîne de blocs |
| Distributed Ledgers | Grands livres distribués |
| Cryptocurrency Mining | Minage de cryptomonnaie |
| Innovation Trigger | Déclencheur d’innovation |
| Peak of Inflated Exepctations | Pic des attentes exagérées |
| Trough of Disillusionment | Gouffre des désillusions |
| Slope of Enlightenment | Pente de l’illumination |
| Plateau of Productivity | Plateau de productivité |
| As of July 2018 | En date de juillet 2018 |
| Plateau will be reached: | Le plateau sera atteint : |
| Less than 2 years | dans moins de 2 ans |
| 2 to 5 years | dans 2 à 5 ans |
| 5 to 10 years | dans 5 à 10 ans |
| More than 10 years | dans plus de 10 ans |
| Obsolete before plateau | Désuet avant le plateau |
| Source: Gartner (July 2018) | Source : Gartner (juillet 2018) |
References
- ↑ Treasury Board of Canada, Blockchain: Ideal Use Cases for the Government of Canada, 5.
- ↑ Vallée, J.-C. L. (April 2018). [Vallée, J.-C. L. (April 2018). Adopting Blockchain to Improve Canadian Government Digital Services. Retrieved on 23 May 2019 Adopting Blockchain to Improve Canadian Government Digital Services]. Retrieved on 23 May 2019
- ↑ Diedrich, H. (2016). Ethereum: Blockchains, Digital Assets, Smart Contracts, Decentralized Autonomous Organizations. Scotts Valley: CreateSpace Independent Publishing Platform.
- ↑ Treasury Board of Canada, Blockchain: Ideal Use Cases for the Government of Canada, 5.

